Have you ever wished you could have ultimate control over your Windows PC? Having the power to not just peek under the hood of almost any Windows process or application, but also the ability to see what files and registry keys your applications are accessing in real-time, is amazing.
Perhaps you are a computer technician looking to add some serious know-how to your Windows tool belt. If we've piqued your interest look no further as we break down Sysinternals, one of the most pedigreed and powerful suites of system and administration utilities for Windows.
A Brief History of Sysinternals
Sysinternals is a collection of free system, administration, and troubleshooting utilities for Windows.
Sysinternals go almost as far back as Windows itself, with the first iteration dating back to 1996. Since then, the Sysinternals suite has evolved with each successive version of Windows, with the arsenal expanding to over 70 distinct utilities. Microsoft outright purchased and acquired the software in 2006, and has kept it free and available for download as either a complete package or individually.
Sysinternals also receives regular updates with new utilities being added over time. Best of all, the software is portable and doesn't require you to install it. Most of the utilities are simple EXE files you can put on a USB flash drive and add to your Windows portable app toolkit for system administration.
How to Get Sysinternals
First, you'll need to load Sysinternals onto your PC. Thankfully, this isn't difficult.
Download Directly From Microsoft
To get started, visit the Sysinternals Utilities Index, where you can also read a short description of each tool's function.
If you opt to download the full Sysinternals suite, your browser will download a ZIP file of around 45MB.
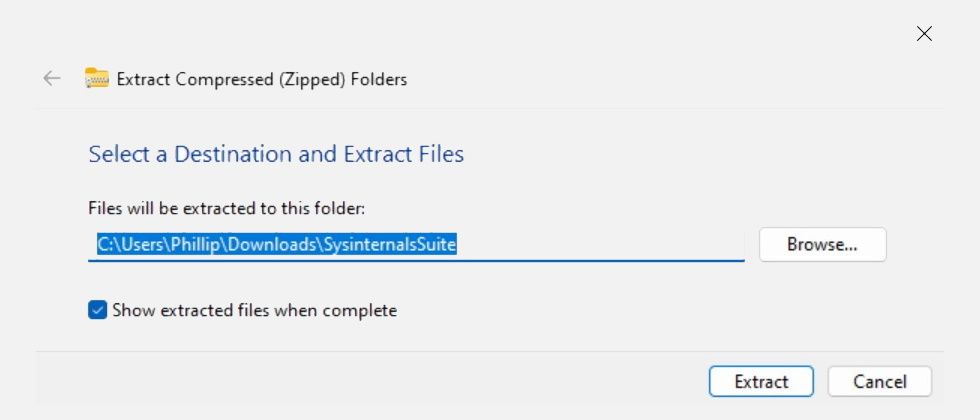
In your downloads folder, simply right-click on SysinternalsSuite.zip and select Extract All. Then, configure a destination folder of your choice and click the Extract button.
Now you are free to explore and use the tools as you see fit. It's worth bearing in mind that most of the tools require administrator access, so be sure to right-click on each tool and select Run as administrator before use.
Running the Tools From SysInternals Live
Sysinternals Live is a service provided by Microsoft that enables you to execute Sysinternals tools directly from the web.
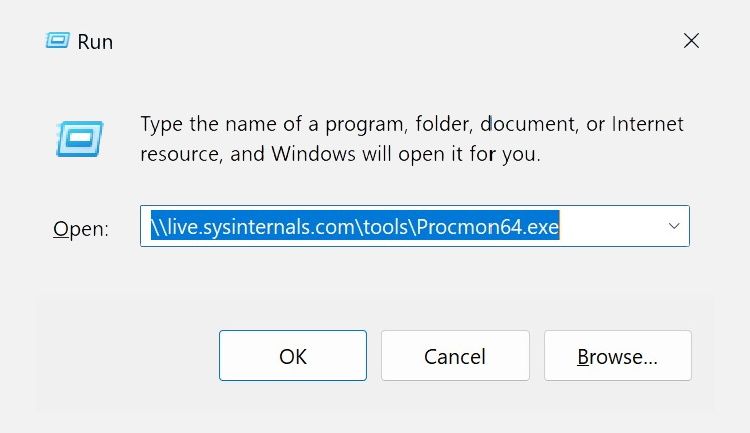
You can run an individual tool directly by entering the tool's Sysinternals Live path into either Windows Explorer or the Run dialog. Use the following syntax: \\live.sysinternals.com\tools\<toolname>
Press Win + R to bring up the Run dialog. Specify the tool name at the end of the path and hit Enter or press OK.
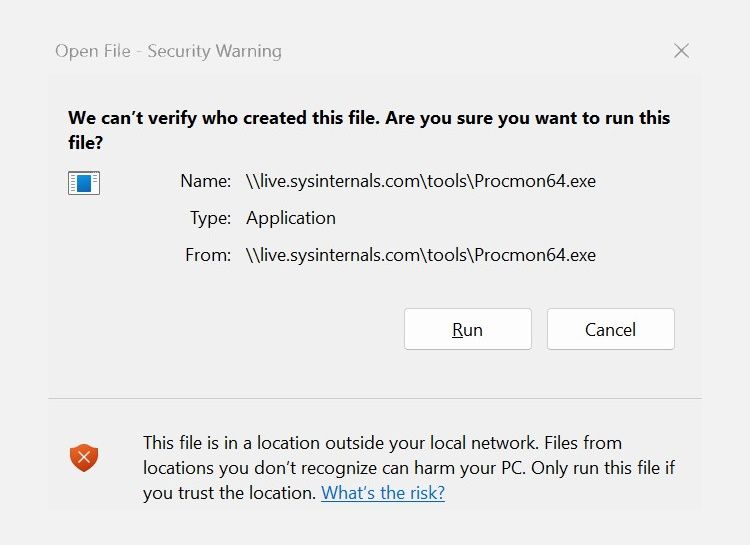
After a moment or two, you will be met with a Security Warning where you can simply select Run to continue. Note that you can view the entire Microsoft Sysinternals Live tools directory in your browser.
What Can You Do With Sysinternals?
Whilst it is unlikely that any one person will ever make use of all the tools available within the suite, there is a plethora of utilities at your disposal.
There are tools such as Process Monitor, which monitors file system, registry, process, thread, and DLL activity in real time. Process Explorer, on the other hand, is similar to Windows Task Manager but with a ton of additional features.
Autoruns helps you manage Windows startup processes as well as detect particularly pesky embedded malware. See how to manage Windows Startup programs with Autoruns for more information.
SDelete, which is a DoD-compliant secure delete program, also cleanses your free space and leaves no traces of previously deleted files.
There are also a variety of heavy-duty command line utilities that help with everything from network and file share security to advanced Active Directory installations and many more.
Next, let's look at some of the more popular tools and how you might want to use them.
Process Explorer: Task Manager's Big Brother
When you open Process Explorer for the first time, you may be slightly overwhelmed by the sheer amount of options and data you are presented with.
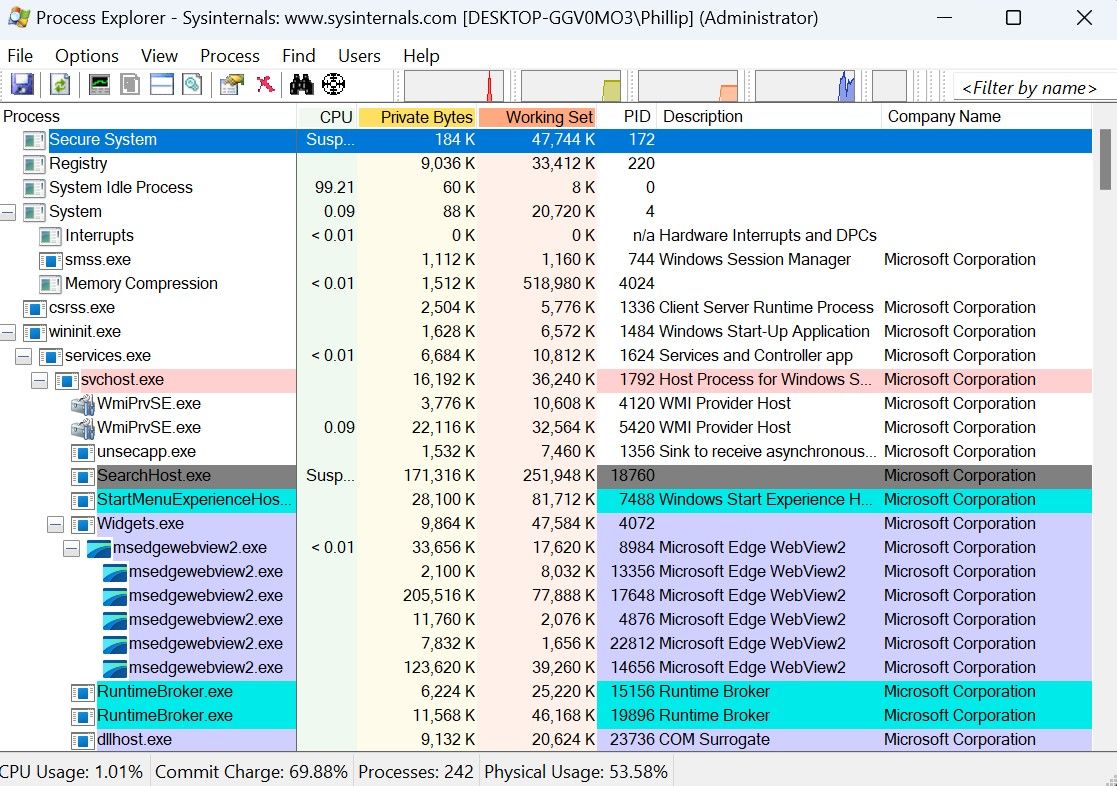
On the left pane, there is the hierarchical tree view which lists all processes and sub-processes running on your computer. Next to that, you will find the CPU and RAM usage, PID (process identifier), Description, and Company Name all presented in columns that can be sorted and customized.
In the toolbar, there are mini activity graphs for CPU, Physical Memory, and Input / Output that once clicked open in a separate window. Under Options > Tray Icons you can also select which activity you would like to have displayed in your Windows Taskbar when you minimize the application.
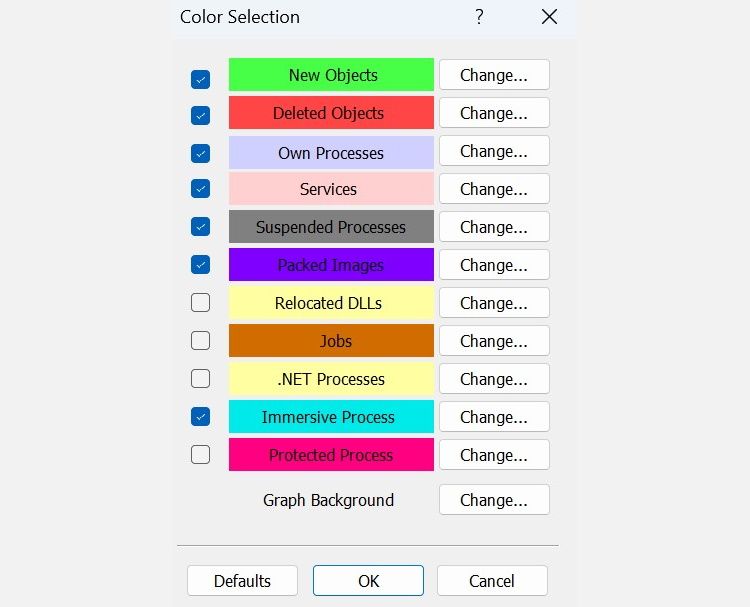
One of the major differences between Process Explorer and Windows Task Manager is the color-coded key used to identify different types of processes. You can bring this key up by going to Options > Color Selection. Keep an eye out for processes marked in purple as these contain compressed code and could be a sign of hidden malware.
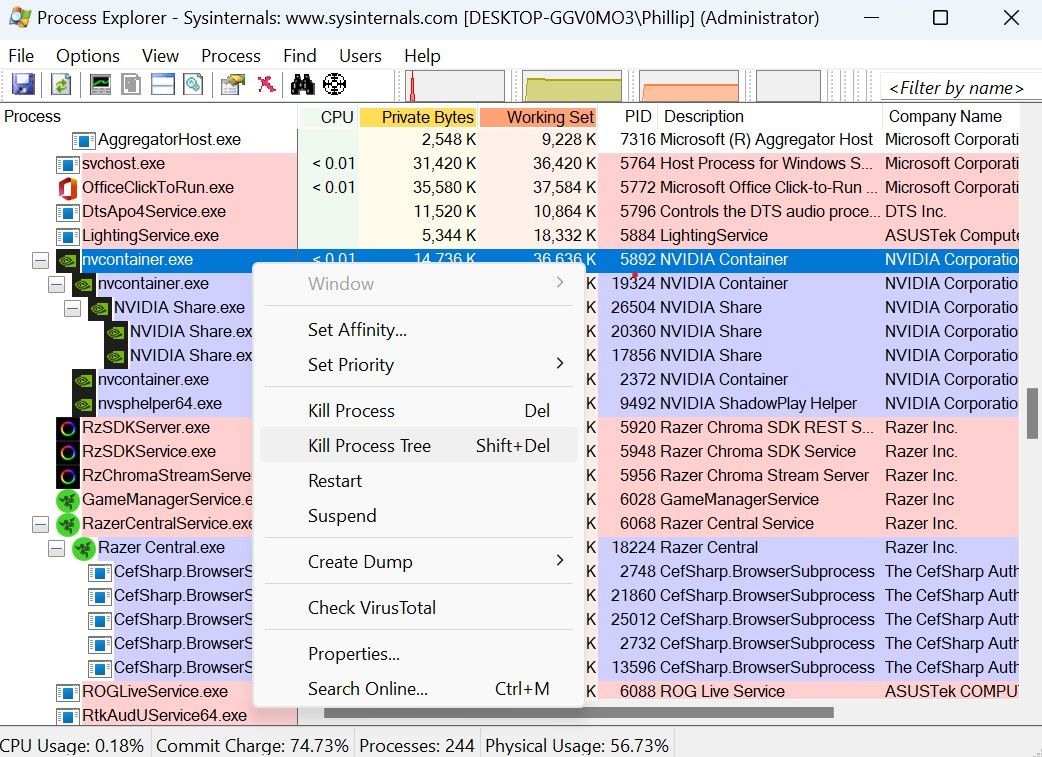
Right-clicking on any process will display a set of options, enabling you to Set Priority, Kill, Kill Process Tree, Suspend the process, and more.
Process Monitor: The Ultimate Windows Log
Process Monitor is quite different from Process Explorer.
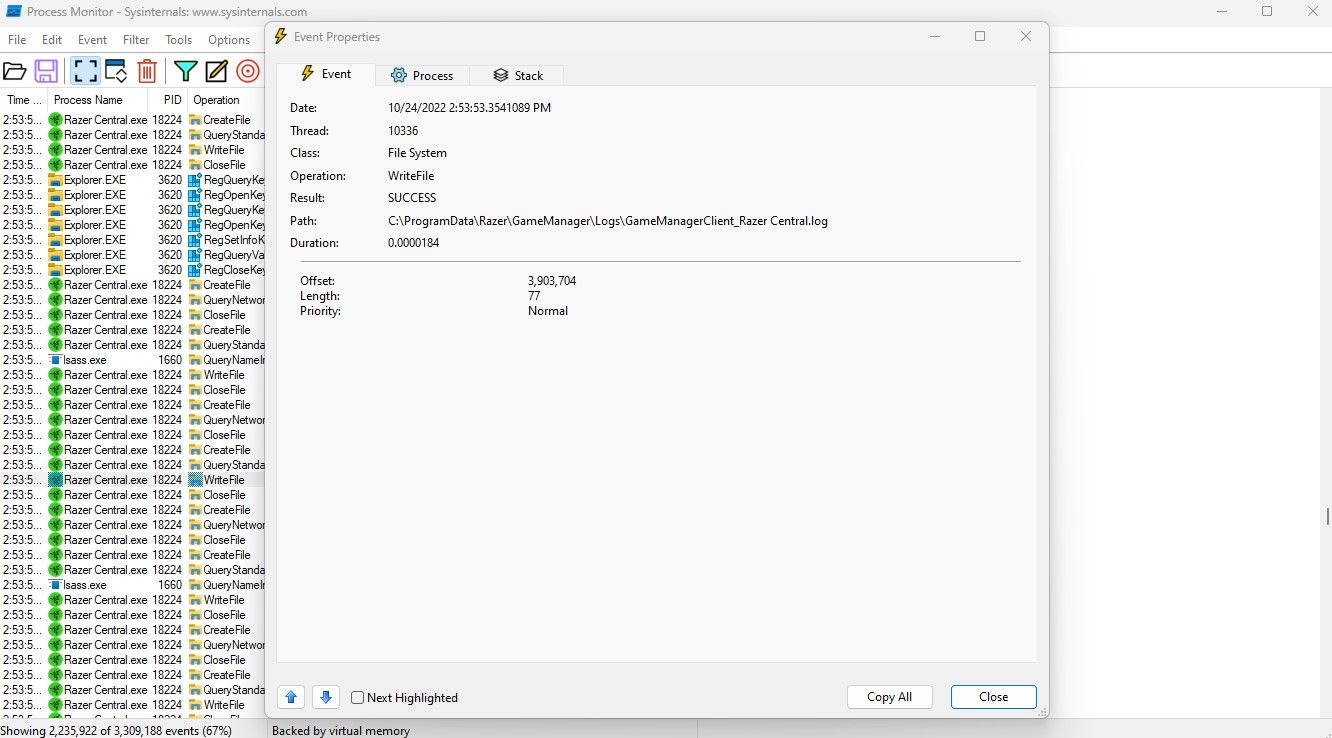
Process Monitor allows you to capture a log of every single event that happens on your Windows PC. With Process Monitor, you can see which registry keys are being updated by any application. Even if a service or application is spawning a new process, changing the file system in some way, or connecting to a network, you can track it with Process Monitor.
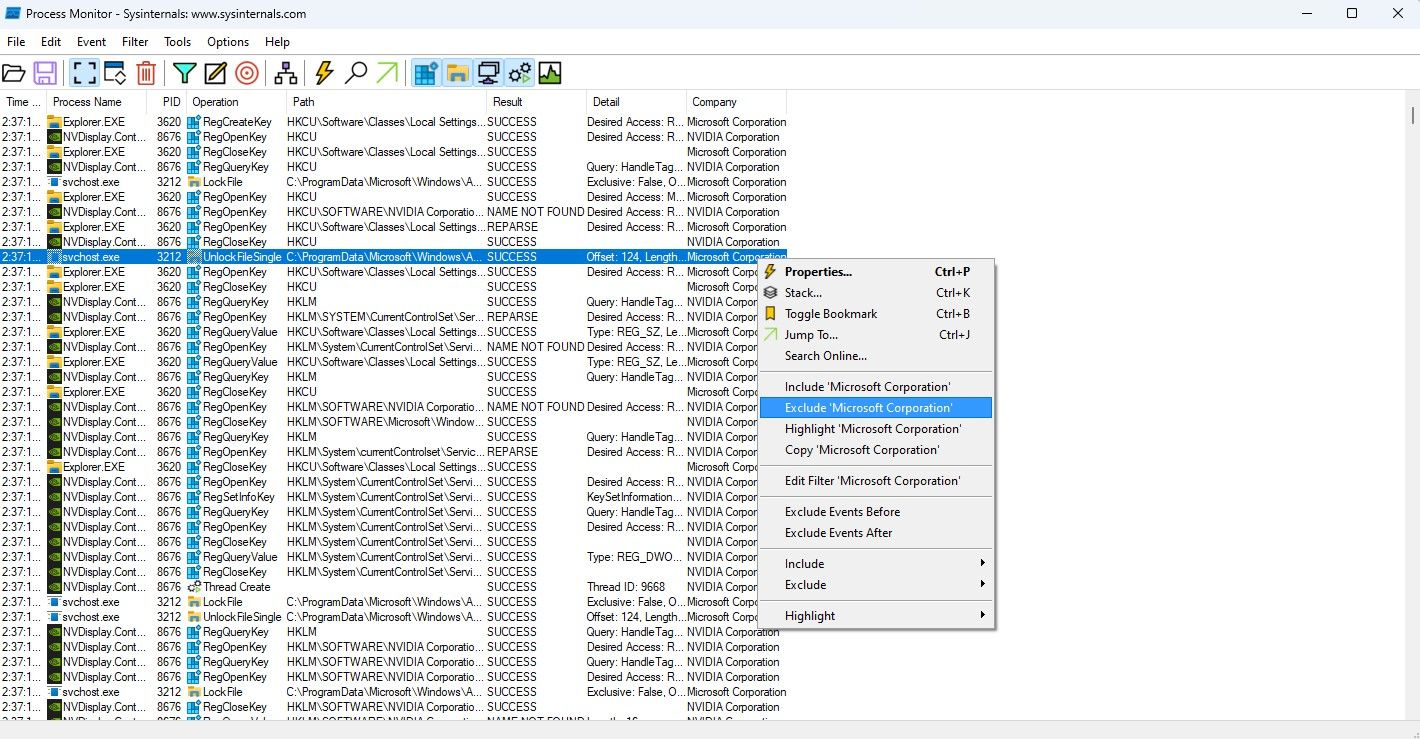
When you first open Process Monitor, you will be greeted with an enormous amount of rows and data. In the background, Process Monitor will continue logging any registry, file system, network, process, and profiling event that may occur. This means that the list of data will rapidly grow even if your machine is idling away, as services interact with your system.
The key to using Process Monitor effectively is to filter out and only focus on the events that interest you. For example: to quickly filter out Microsoft processes you can go to Options > Select Columns and include Company Name. Then simply by right-clicking on the column, you can use the Include / Exclude function in the context menu to quickly filter these events out.
Double-clicking or right-clicking on an event and selecting Properties will open an additional dialog with a wealth of information. From this dialog, you will be able to determine the class of the event (i.e. File System or RegistryQueryKey,) the path to the physical operation, and the result.
From here you can dig even deeper by going to the Stack tab where you can see the individual DLL files associated with the event.
By default, Process Monitor uses your computer's virtual memory to store events which is temporary. If you go to File > Backing Files you can specify a file for the data to be written and saved to.
Autoruns: Configuring Startup Processes and Applications
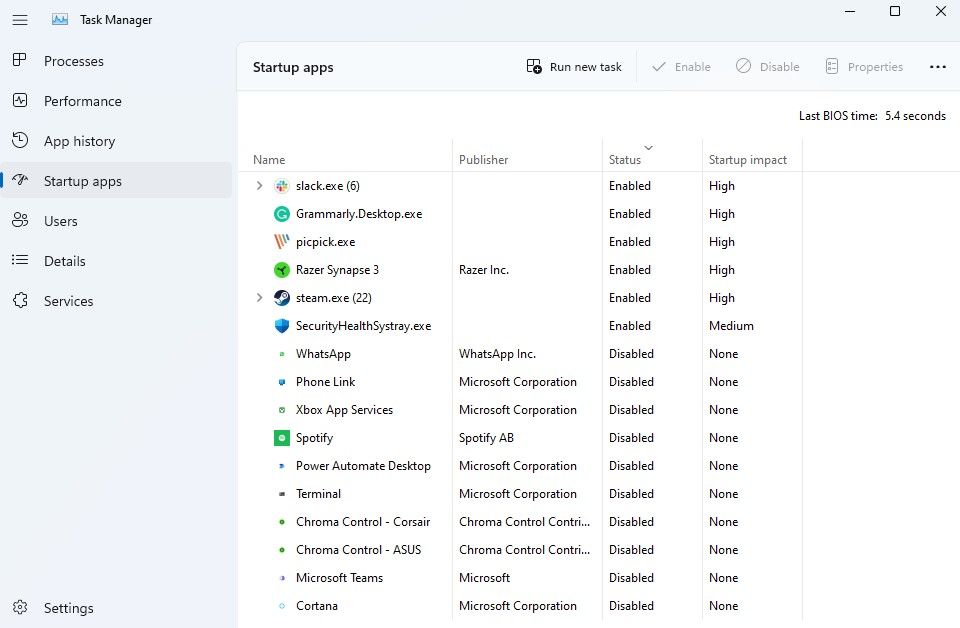
Windows provides a few options for dealing with startup processes and applications out of the box. Task Manager, for example, has a dedicated Startup apps section within its navigation pane. The same information can also be found in the Settings app under Apps > Startup.
Whilst this is probably good enough for most people, it doesn't really give you a full picture of what is being loaded each time you boot up your PC. In reality, there are many more sophisticated ways software can be configured to auto-start on Windows. There are browser helper objects, scheduled tasks, services, drivers, and even some nearly undetectable methods like image hijacks and AppInit_dlls.
If you are looking for a comprehensive list of startup items then Autoruns is your answer.
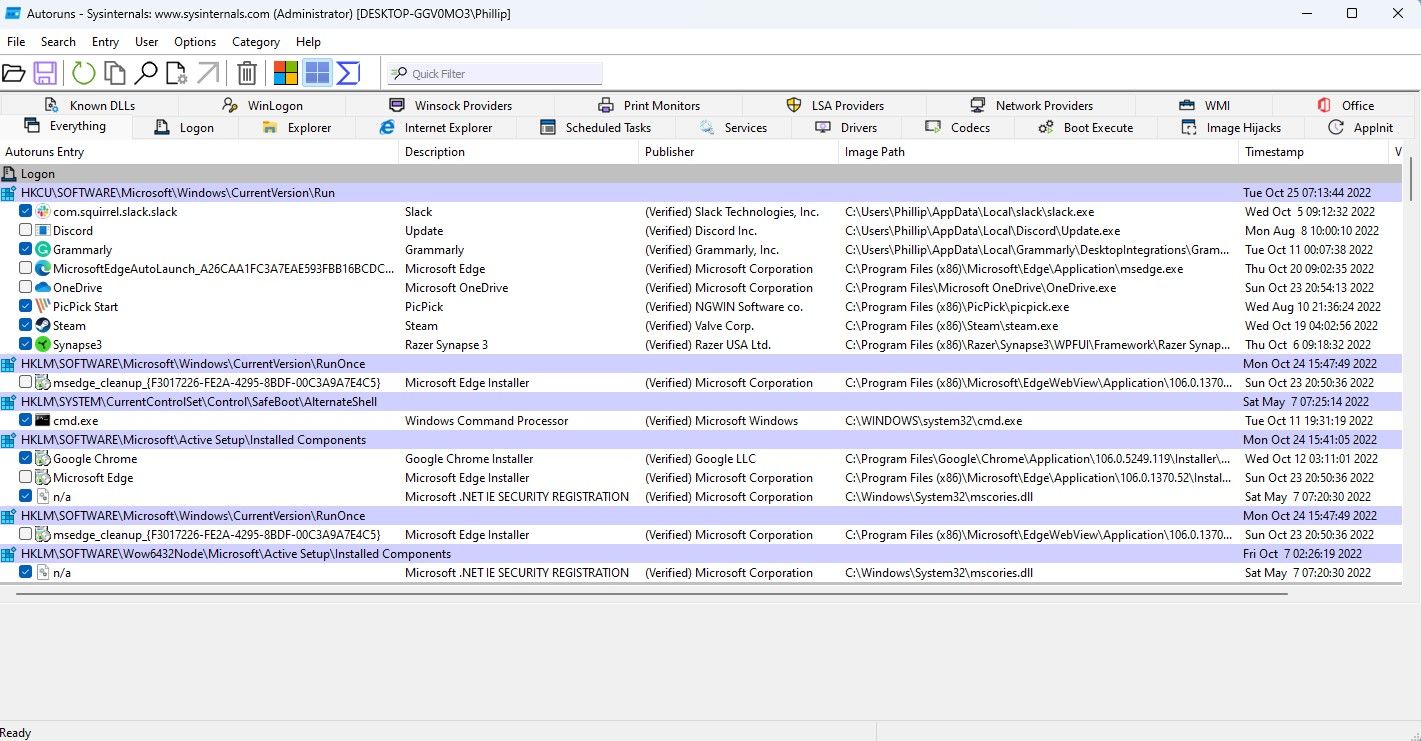
By default, when you first open Autoruns you will land on the Everything tab. This displays every single startup item from each and every tab. Naturally, you can cycle through the tabs to distill the information further.
Each tab gives you an idea of the mechanism being used by the startup item. For example, the Logon tab displays all items loaded when your user logs in to Windows. The Explorer tab on the other hand lists all startup items that attach themselves to the File Explorer process when it runs.
To stop any startup item from running, simply uncheck the checkbox next to the program on the left. That's all there is to it. Just be careful when deselecting anything in the Drivers and Services tabs as most of these are essential for your Windows apps and components.
Sysinternals Offers So Much More
Hopefully what we have covered so far has turned you on to the idea of Sysinternals. Whether you want a complete snapshot of everything happening on your PC with Process Explorer, the granular detail exposed by Process Monitor, or the ultimate authority of what programs get to run at startup with Autoruns, Sysinternals has a tool for just about everything.
We've only covered the basics of what's possible using the tools in the Sysinternals suite. Feel free to explore them on your own, but just remember with great power comes great responsibility.