latest
Meet the Most (In)Famous Hacking Groups Active Today
Get a sneak peek into the world of modern hacktivists and cybercriminals.
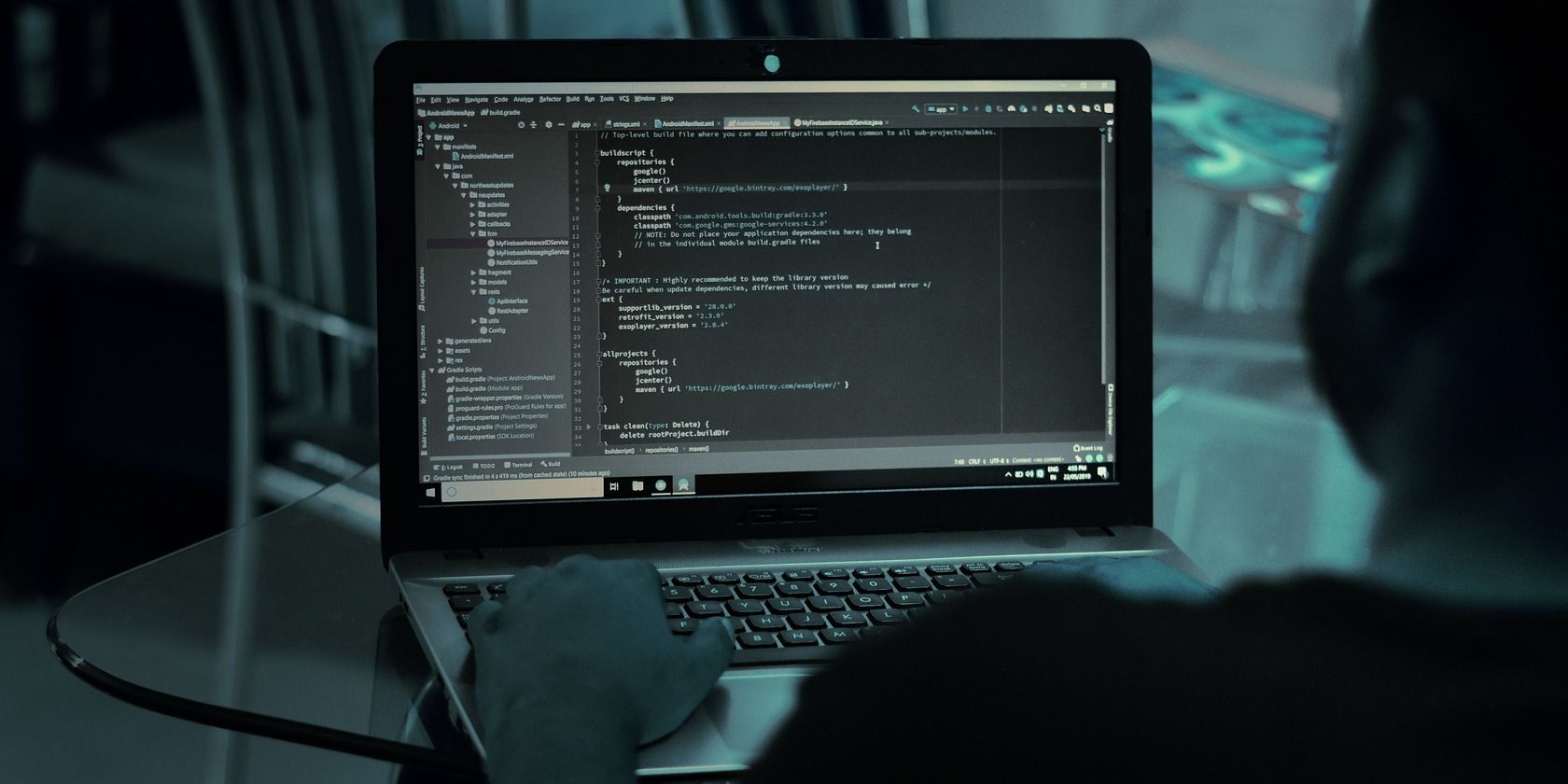
Ethical Hacking: What Are the Stages of Penetration Testing?
How do cybercriminals hack into systems? How can you protect against them? Ethical hackers can show you via pentests.

5 Powerful Linux Tools to Discover Subdomains as an Ethical Hacker
If you're an ethical hacker, gathering information about the subdomains of a website is important. Here are some free Linux tools that will help you.

What Is the Certified Ethical Hacker (CEH) Certification and Who Needs It?
These credentials let people know that you have the necessary skills and that you're working to fight crime, not commit it.

Cybersecurity vs. Ethical Hacking: How Do They Differ?
Explore the key differences between cybersecurity and ethical hacking to better understand their roles in protecting digital systems.

Who Is a Red Teamer and How Can You Become One?
Hacking is a valuable skill. Becoming a red teamer is one way to put that knowledge to good use and help others in the process.

What Is Crowdsourced Security?
When new software hits the market, it's tested for vulnerabilities. One way is through crowdsourcing. But is that reliable? Is it actually safe?

Are University Courses Helpful for a Career in Cybersecurity?
University might not always seem the right route for you, especially if you want to go into cybersecurity. But is university worth it after all?

What Is Scambaiting? Here's Everything You Need to Know
Not all scammers are bad. No, really. Some are here to educate, inform, and entertain. That's where scambaiting comes in.
How to Use Burp Suite's Intruder Tool to Pentest Web Apps
Are you an ethical hacker or pentester? You'll likely have used Burp Suite. So how do you use its Intruder tool to get better targeted results?

How Do Hackers Make Money, Legally and Illegally?
You're probably picturing a shady hacker stealing your personal information. But how do they actually make money, both illegally and legally?
What Are Bug Bounty Programs? Here's Everything You Need to Know
Have you found a flaw in a system or product? Want to know how ethical hackers actually make money? That's where bug bounties come in.

Everything You Need to Know About BlackArch Linux
BlackArch is a well-known penetration testing distribution based on Arch Linux, but not everyone is aware of the unique features that set it apart.

Kali Linux 2022.3 Released With Major Hacking Tool Upgrades
The developers have also announced a new Discord server. What will happen to their IRC channel?

What Is a Gray Hat Hacker?
You may have heard of black and white hat hackers, but what does a gray hat hacker do? Let's find out.

How to Make a Career Out of Ethical Hacking
Interested in exploring the field of ethical hacking? Here's your guide to building a successful career in ethical hacking.

Steam Deck Repair, Windows 11 Ethically Hacked, Anonymous Browsers, and External Hard Disk Errors
Our tech podcast looks at the Steam Deck repair notes from iFixit, anonymous browsing, and more!
The World's Most Famous and Best Hackers (and Their Fascinating Stories)
White-hat hackers versus black-hat hackers. Here are the best and most famous hackers in history and what they're doing now.

Pwn2Own Hackers Just Broke Into Windows 11 and Teams in a Single Day
The hacking competition saw some big wins for hackers, and some major losses for Microsoft.

Kali Linux 2022.2 Lands With Desktop Tweaks, Hilarious Hollywood-Hacking-Homaging Screensaver
The latest version of Kali Linux shows that developers like to kick back and have fun while developing powerful hacking tools.
