“If you knew what I know about email, you might not use it either,” said the owner of secure email service Lavabit as he recently shut it down. "There is no way to do encrypted e-mail where the content is protected," said Phil Zimmermann as he suddenly shut down Silent Circle's secure email service. The reality is that email is fundamentally insecure and can never be protected from government surveillance in the same way some other communications can.
Sure, you may be using a different encrypted and "secure" email service that hasn't shut down yet. But they're vulnerable to the same US government pressure Lavabit faced -- that's why Silent Circle shut down before it was contacted by the government. Some less principled services will opt to cooperate with governments rather than shut down. We don't know exactly what demands Lavabit faced, as they're forbidden from disclosing anything they experienced as a result of backdoor orders from the secret US surveillance court that enables PRISM and other NSA surveillance programs.
Now, let's look at why email is a poor choice for secure communications, and how it's an easy target for government snooping.
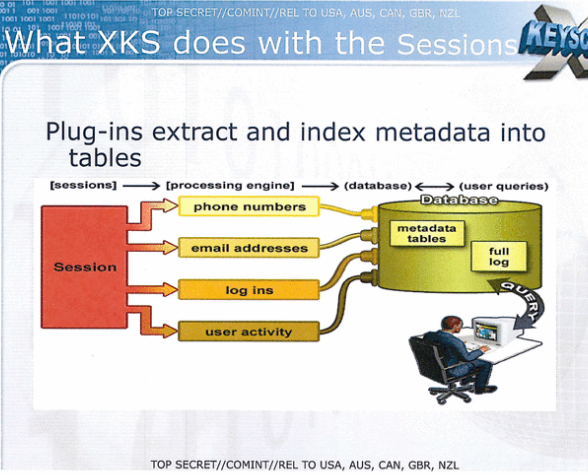
Metadata Can't Be Encrypted and XKEYSCORE Can Intercept It
An email isn't really a single piece of data. It's multiple pieces of data: There's the message body, the subject line, the From field, the To/CC/BCC fields, and other metadata that includes the location you're sending the email from.
Even if you use the best email encryption technology possible, you can only encrypt the message body of the email. Anyone monitoring the connection you're using can view the subject of the email, who you're communicating with, and where you're emailing from. Under the XKEYSCORE program that essentially allows the US government to capture most of the traffic flowing over the Internet by intercepting it at large backbone routers and gateways, the government can build up quite a picture of who you're communicating with, when you're communicating with them, where you're each communicating from, and what the subject lines of your emails are, which gives them an idea of what you're talking about. They may find the fact that you're encrypting the contents of your emails suspicious and target you for further, more in-depth surveillance of everything else you do.
The US government collected US email records in bulk until 2011. According to the NSA, this program was discontinued because it wasn't effective -- but they're still gathering metadata under XKEYSCORE, so they're likely intercepting all the email metadata they can get their hands on. They'll get lots of information from you even if you encrypt your emails.
For more information, read about the things you can learn from an email's "header", or metadata.
Many "Secure" Email Providers Have the Encryption Keys For Convenience
Encrypting and decrypting emails is complicated. In theory, you'd use something like PGP or GPG on your local computer to decrypt emails. In practice, the setup can be complicated and confusing, even for more tech-savvy users. This also makes it impossible to access the encrypted emails via a browser or lightweight mobile client.
In practice, many secure email providers have dealt with this by holding the encryption keys at their end, decrypting emails when you access them. This is how Silent Circle's secure email service worked -- they had the encryption keys so they could easily decrypt emails and offer a good user experience. In practice, this means that the government could demand all the encryption keys -- or just the ones they needed -- and decrypt all the emails they wanted to. If the provider has the keys, they could hand them over. The only way to securely encrypt and decrypt email bodies is with complicated desktop software. Even all this effort leaves the metadata exposed.
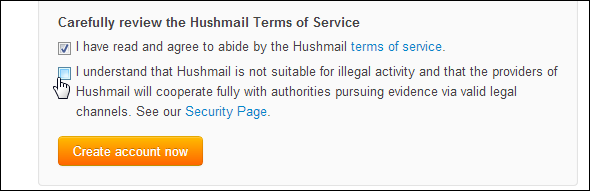
The Government Can Demand Backdoors: See Hushmail
Canada-based Hushmail is one of the most popular and widely-known encrypted email services. In 2007, Canadian courts compelled Hushmail to hand over the emails of one of their users. The emails were then passed to U.S. courts under a mutual legal assistance treaty between Canada and the USA.
Hushmail theoretically couldn't do this. They didn't keep users' encryption keys on their servers. They recommended users use PGP or similar software to decrypt the emails on their computers for maximum privacy. However, many people thought this was too inconvenient, so Hushmail also offered a downloadable Java applet located on a web page that allowed you to access your email. When you accessed the web page, the latest version of the Java applet would download to your computer, you'd enter your encryption key, and the applet would download and locally decrypt your email without Hushmail gaining access to your encryption key.
Hushmail was compelled to serve a version of the Java applet with a built-in backdoor to the user in question. The modified Java applet sent the user's encryption key to Hushmail after it was entered and Hushmail gained access to the user's emails, which they handed over to the courts.
If you do use secure email, the provider can be forced to acquire your key in any way possible. Even if they couldn't gain access to your key, the provider could hand over your encrypted emails themselves, which would show the government who you're communicating with, when, and about what (via the email subject line).
Email Messages Are Stored on a Server, Instant Messages Are Not
Even if the government can't get or intercept the encryption key, they may be able to decrypt your emails anyway. Your encrypted email messages are stored on a server -- that's just how email works. If the government were to demand this data, the hosting provider would have to hand it over in encrypted form. The government could then try to break the encryption -- new hardware regularly makes current encryption mechanisms much weaker, and the US government may be storing such encrypted communications in the hopes of breaking them in the future.
In contrast, instant message-style communications are harder to archive. An encrypted message can be sent directly to the recipient and not stored on a server where it can be accessed in the future. The government would have to install a monitoring device and capture all the communications in real time. If they failed to do so and didn't have all the encrypted data, they wouldn't be able to go get it years later -- but they can often do this with email.
Other Types of Communication Can Be Secured
Email just wasn't designed with encryption in mind. It's been bolted on after-the-fact, and it shows. Even the most careful of secure email service users can't hide who they're communicating with and when. If you really want to avoid government surveillance, you're better off using different secure messaging services instead of relying on email.
That's why Silent Circle still offers a secure messaging service that they're confident in the security of. It's not the only option either -- Cryptocat is another. Cryptocat had a recently publicized vulnerability and other services may have their own problems that we'll hear about in the future, but these services are on the right track -- they're not fundamentally insecure by design the way email is.
Of course, encrypted email isn't necessarily worthless. For example, if you want to secure important business communications against eavesdropping, it can be useful. But encrypted email isn't going to slow down the government very much -- it's not the ideal communications tool when you're trying to talk without the NSA hearing.
Do you agree with the principles behind Lavabit's and Silent Circle's shutdown? Do you use a secure messaging service to communicate without your conversations being stored in a massive government database? Leave a comment and let us know which email-alternative you prefer.
Image Credits: Metal detector Via Shutterstock