Data breaches are rapidly becoming a part of everyday online life. Even a cursory glance at the news highlights the latest leak of confidential or personal information onto the internet. While many people are increasingly concerned by these developments, it can often seem as though you are powerless against them.
Some suggest taking your PC offline to isolate your data away from the online world. Without a connection to the outside, your data should be safe, right? However tempting it might seem as a solution, it might not be the fail-safe you were hoping for.
1. USB Drives and Social Engineering
The TV show Mr. Robot introduced a broad audience to online security and hacking. It even gained favor with the infosec community for its accurate portrayal of hacking, internet culture, and hacking tools. Unlike the similarly-themed but widely-mocked 1995 film, Hackers, Mr. Robot went to great lengths to educate, as well as entertain, its viewers.
In the show's first series, an attack was put into motion after some infected USB drives were left strategically near the building the hacker wanted to infiltrate. This is a form of social engineering attack. The assailant knew that if one person picked up an infected drive, they would quite likely take it inside, plug it into a computer, and see what's stored on it.
This is often done in good faith, as they want to return the drive to whoever may have mislaid it. The attacker takes advantage of this human trait, effectively tricking the victim into loading malicious software onto the target computer via the infected flash drive. This type of manipulation is known as social engineering.
As they don't want to draw attention to the hack, there is usually no visible sign that the computer has been compromised, so the victim doesn't take further action to defend against the attack. This leaves the now-vulnerable PC unprotected and open for the attacker to exploit.
In the context of an offline PC, a rogue USB drive could be used in a range of attacks, even ones where the intruder has physical access to the computer to load malicious software themselves via the infected storage device. The CIA used this in an attack known as Brutal Kangaroo, and Wikileaks exposed the technique as part of the Vault 7 disclosure in 2017.
2. DiskFiltration Attacks
If an organization has highly sensitive data or systems, they may consider air-gapping the host computer. In this case, the PC is taken offline, but it is also physically disconnected from the internet and all internal networks to effectively isolate it. If the setup is NATO compliant, the PC will also be positioned away from outside walls and all wiring to prevent electromagnetic or electrical attacks.
Air gapping is widely considered an appropriate way to protect high-value systems from exploitation, but some research suggests that it may not be as secure as once thought. Studies conducted at Ben-Gurion University examined how an air-gapped computer may be compromised, but without malicious software installed, access to the PC, or social engineering.
The extraction method, known as DiskFiltration, relies not on exploiting the computer but analyzing its sounds. Although Solid State Drives (SSDs) are becoming more commonplace, many of us still rely on Hard Disk Drives (HDDs). These devices store data on a disk, much like a vinyl record. Similarly, the HDD requires the movement of an arm across the drive to read and write data.
This physical movement generates noise, which we perceive as a low background hum or whirring. However, in a DiskFiltration attack, the drive's noises are used to glean the information stored on them. Air-gapped computers usually don't have speakers or microphones attached, so they can't amplify the hard drive's audio. Instead, this noise is relayed to a smartphone or smartwatch receiver up to two meters away. This exploit is just one of the ways that an air-gapped PC isn't really secure.
While this can affect air-gapped computers, it can also be used to compromise network-connected devices, even if they are heavily monitored for security events or intruders. During testing, the DiskFiltration attack could transfer data at 180 bits per minute, or 10,800 bits per hour. Fortunately, this attack is ineffective against devices with SSDs as there are no moving parts, and thus, no noise.
3. Analyzing Fans With Fansmitter
While it seems logical that hard drives might leak data in unexpected ways, it's harder to imagine other computer components doing the same. However, the Ben-Gurion University researchers developed a similar method for extracting information from an offline PC using the computer's fans. This attack is known as Fansmitter.
Your computer's fans enable air to pass over the warm, sometimes hot, internal components of your computer. The exhausted air removes heat from the system to keep your computer operating at optimal performance. In most computers, there is an ongoing feedback loop between the fan and the motherboard. The fan's sensors report rotation speeds back to the motherboard.
The computer calculates whether the fans need to be increased or decreased based on the temperature. The Fansmitter attack exploits this feedback loop by overriding the stored optimal temperature value. Instead, the fan speed is adjusted to emit a particular frequency, which can be used to transmit data. As with DiskFiltration, the resulting audio is captured by a smartphone receiver. The most effective countermeasure is either to install low noise fans or a water-cooling system.
4. Changing Temperatures With BitWhisper
While many offline PC hacks rely on analyzing noises and audio outputs, there are alternative methods. The BitWhisper attack uses heat to compromise an offline computer. First, there are several caveats to this exploit. There need to be two computers; one offline and air-gapped, the other connected to a network. Both machines also need to be infected with malware.
The two devices must be within 15 inches of each other. Given this exact setup, it's the least viable for real-world application but is still theoretically possible. Once all pre-conditions have been met, the networked PC changes the room's temperature by adjusting the load placed on its CPU and GPU. The thermal sensors on the air-gapped PC detect these changes and adapt fan performance to compensate.
Using this system, BitWhisper uses the networked computer to send commands to the air-gapped PC. The offline computer converts the sensor data into binary, so either a 1 or a 0. These inputs are used as the basis for computer-to-computer communication. Aside from the precise setup needed to make this work, it's also a slow attack method; it achieves a data transfer rate of just eight bits per hour.
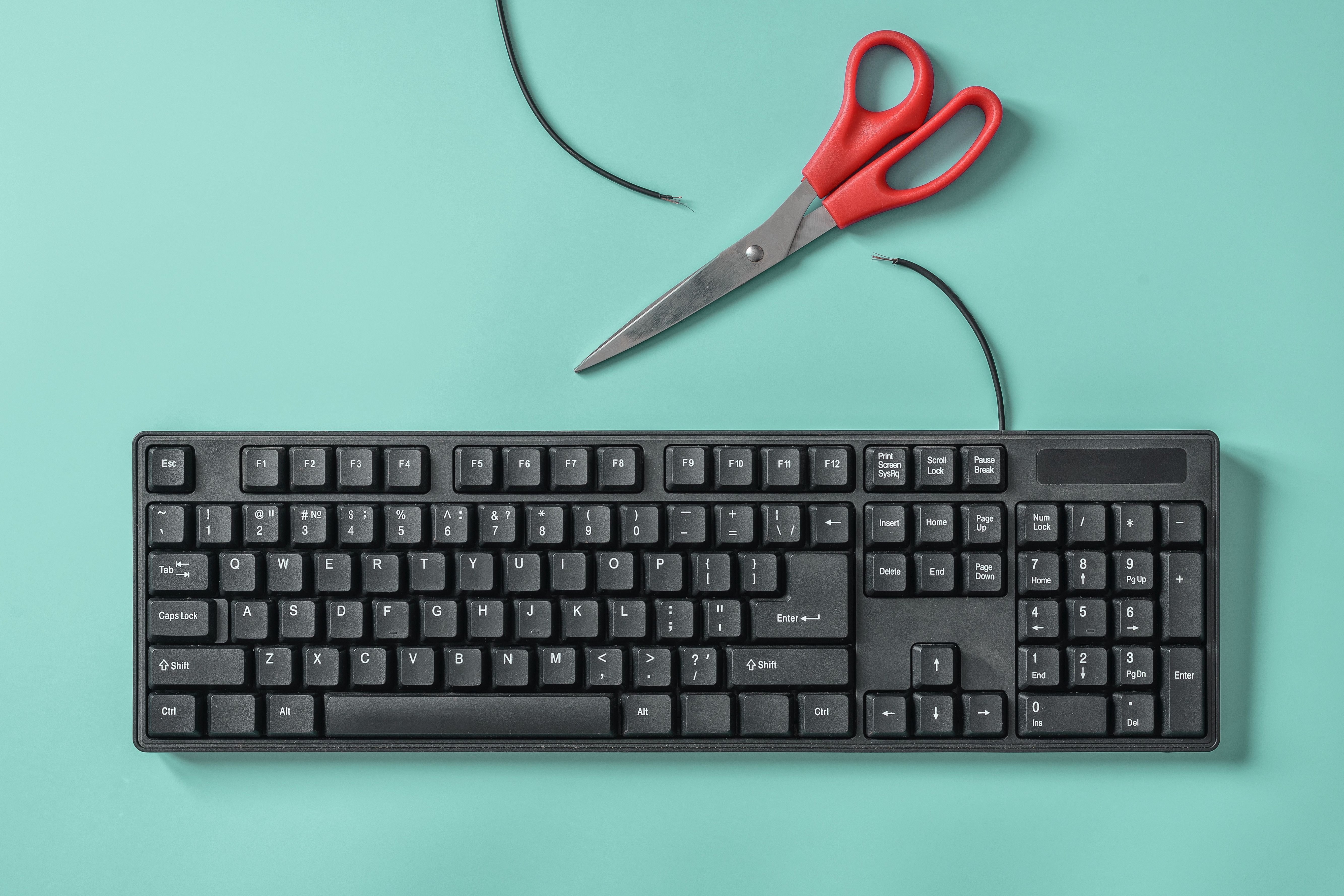
5. Wired and Laptop Keyboards
Although many of us now use wireless keyboards, wired varieties are still common worldwide, especially in business or institutional settings. These facilities are most likely to be storing sensitive data and systems, and therefore the most at risk of attack.
When you press a key on a wired keyboard, it is converted into a voltage and transmitted to the computer via the cable. These cables are unshielded, so the signals leak into the PC's main power cable. By installing monitors are the electrical socket, detecting these small changes in power requirements is possible.
Although the data initially looks messy and unclear, once a filter is applied to remove background noise, it becomes possible to assess individual keystrokes. However, this type of attack is only possible for PCs that are consistently plugged into the mains.
Portable devices like laptops can also leak data from the keyboard. During a presentation at Black Hat in 2009, titled "Sniffing Keystrokes With Lasers and Voltmeters," the researchers showed that by pointing a laser toward a laptop's keyboard, it was possible to translate vibrations from keypresses into electrical signals.
Due to the laptop's construction and design, each key has a unique vibration profile when pressed. An attacker could gather precisely what was typed on the keyboard without malware like keyloggers by assessing the electrical signals.
Still More Secure Than a Networked PC
These attacks demonstrate that it is possible to hack an offline PC, even if you don't have physical access. However, although technically feasible, these attacks aren't straightforward. Most of these methods require a particular setup or optimal conditions.
Even then, there's a lot of room for error as none of these attacks directly captures the desired data. Instead, it has to be inferred from other information. Given the difficulty in attacking an offline or air-gapped PC, many hackers have found an alternative route; installing malware before the computer reaches its destination.