Before I get started writing this article, I'm just going to say that Apple does a good job protecting its customers from malware, viruses, and various other mythical beasts on the internet. However, a lot of monitoring software still exists for Mac, and you should know about it, right?
I'm going to be honest with you in that I didn't download any of these at all, and this was done for two reasons – they aren't free, and I don't trust them.
Just know that the first purpose of this article is to let you know that this enemy actually exists, and the second purpose is to help you know your enemy by name.
Spector Pro [Snow Leopard]
As a product of SpectorSoft, Spector Pro markets itself as a way to check in on the kids or make sure that your employees are staying on task. It even prides itself with its ability to block websites and specific contacts on instant messaging. However, we all know that this doesn't mean people wouldn't use it for malicious reasons. (As a note, the website also has some sketchy user testimonials anyway.)
Besides its basic run-of-the-mill keylogging methods, Spector Pro forwards all emails, transferred files, and screenshots to its primary operator (read: stalker). Also, like most keyloggers, the software will likely run in stealth mode if it is being used on you, so just keep that in mind. However, at the price of $99, the perpetrator would likely use it only if they had serious intentions.
SniperSpy [Snow Leopard]
SniperSpy is one of three spy-related pieces of software produced by Retina-X Studios. Once again, we have the typical explanation of "Watch your children!" and "Watch your employees!". However, in addition to its basic functions of screenshot capturing, location mapping (based on the current IP) and keylogging, SniperSpy allows its operator to view everything that you are doing totally live in a VNC-like fashion.
Basically, as you are typing out your romantic messages to your hypothetical forbidden lover, your spouse could be watching you as it happens. Another feature allows for operators to send the computer user an onscreen message – perhaps something classic like, "All your base are belong to us."
Aobo Keylogger [Snow Leopard & Lion]
Aobo claims that you can use the software to "spy and discover the truth" and "get back a stolen Mac". This is perfectly fine and seemingly honest, but there is always the chance someone might have ulterior motives while using it. The website for this software is a little iffy, so just keep in mind its users could be equally so.
The software comes in two varieties – standard and pro – and both of them collect the standard information that any keylogger would. However, the professional version is noted for its ability to record passwords that are typed in-browser, and it claims to have been the first keylogger for Mac to do so. All logs (including screenshots, keystrokes, and websites) can be sent to the operator's email or FTP.
Amac KeyLogger [Snow Leopard & Lion]
Much like the other monitoring programs mentioned in this article, Amac Keylogger requires the operator to install the software on the actual computer itself. Granted, this could always possibly be done remotely by a well-versed operator, but in the meantime, just reconsider who regularly plugs flash drives into your computer.
Amac Keylogger functions just as you would expect it would – it watches you do whatever you do, sending information of your activities to the mystery man behind another screen. Although it displays itself as employee monitoring software, it is easily exploitable. If you download it once, it monitors all user accounts on the Mac in question, and it always will open up in stealth mode on the user's computer. Also, much like Aobo, the professional version of this software can record passwords.
Conclusion
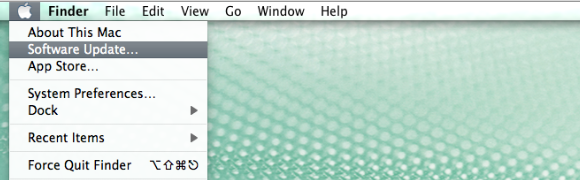
Keep in mind that Apple does subtly protect its users from these Internet demons anyway, but if you want a basic method to combat keyloggers yourself, you should take a look at this MUO article – 4 Ways To Protect Yourself Against Keyloggers. Besides this, remember to always update your OS to prevent unintentional installation, and don't be surprised that some people do not. Take this example – a close friend of mine who works primarily with Macs once knew someone who hadn't done so since the day that they bought it!
Have you ever encountered an attack on your Mac? Do you have any further knowledge about the ones mentioned here? Share with us in the comments.