A VPN, or Virtual Private Network, is an easy way to link two locations like they are using the same local network. Once the reserve of large organizations and businesses, people now use VPNs to protect privacy, enhance security, and access geo-locked services, such as Netflix.
Let's go over the reasons you might want to use a VPN, the difference between a VPN tunnel and other VPN services, and why a paid VPN is always the best option.
What Is a VPN?
First things first: VPN stands for Virtual Private Network.
A VPN is a secure tunnel between two parts of the web. Think about it like this: a tunnel that goes under a mountain. Both sides link to a direct path through the mountain. In this case, the mountain is the internet.
One of the main reasons for using a VPN is privacy and security. The VPN uses encryption to protect your data in transmission. Anyone snooping on your connection will struggle to figure out what you're doing online when you use a VPN. Encryption is a vital privacy tool for all internet users.
You can use a VPN connection for any number of reasons, including privacy, security, logging into remote services, accessing your office intranet from an external location, and watching geo-locked content from a restricted location, to name but a few.
What Is a VPN Tunnel?
A VPN tunnel is an alternative way of referring to a VPN. The phrase "VPN tunnel" isn't used as commonly as just "VPN," as more people became aware of and began using VPNs for regular internet activities, not just protecting privacy or logging into a remote computer network.
How Does a VPN Work?
Without a VPN, your data flows between your computer and the servers of whichever website you are visiting, like MakeUseOf. Your ISP, government, and other organizations can track and analyze the data you use and it could be vulnerable to snooping and other internet attacks.
A VPN protects your data in transit from your computer to the VPN server. The VPN provider encrypts your data, making sure that no prying eyes can intercept or read data coming from your PC, laptop, smartphone, or otherwise.
The VPN connection only protects your data as far as the VPN server. Once your data leaves the VPN server, it is back in the wild. The website server won't know the originating IP address and therefore won't trace you to a single location. However, as mentioned, if you connect to your Facebook account even while using a VPN, they still know that it is your Facebook account.
In the early days of VPN use, you would have to set up a VPN tunnel that forwarded all of your web traffic. Whereas, you now have a massive choice of VPN providers, most of whom provide an easy to use VPN client for your computer.
Is It Safe to Use a VPN?
Using a VPN is safe. But the legality of using a VPN depends on your locale. There are several countries around the globe where the use of a VPN is illegal specifically, or the use of encryption (for private citizens) is illegal. You should always check local laws before using a VPN in a new country, especially those with a restrictive government.
The other side of VPN safety is understanding how secure your data really is. A VPN will protect your privacy to an extent. If you log into your Facebook account while using a VPN, Facebook will still know that it is you. It'll just appear that you're in a different location to usual and because of that, you might encounter an extra security check.
If your Google account remains logged in, Google can still link your Google searches to your profile, and so on. Did you know that some people avoid Google search altogether? Google even has its own VPN. Check out one of these privacy-focused Google search alternatives to boost your privacy.
So yes, a VPN does protect your privacy. But only if you attempt to use the internet in a private manner.
Is a Free VPN Safe?
There are two types of VPN: free and paid.
Many people see the word "free" and think that a VPN is just a VPN; it does what it says on the tin. That isn't the case though. A free VPN is free because it monetizes the service through alternative methods. In the case of a free VPN, the monetization can come from collecting your data and selling it, displaying intrusive ads, and more.
There are other issues with free VPN services, too. A free VPN might skimp on important security measures, such as the level of encryption, the type of VPN protocol, the number of available servers, and speed restrictions to name a few.
The safety of your VPN can come down to a paid-for VPN versus a free VPN. If you know that you're paying for the service, and the VPN has no need to advertise or sell your data, that is a positive privacy and security step.
What Is the Best Paid VPN Service?
MakeUseOf always advises using a paid VPN service where possible. There are times when using a free VPN is okay, but you shouldn't expect it to protect your privacy in the same manner as a paid VPN.
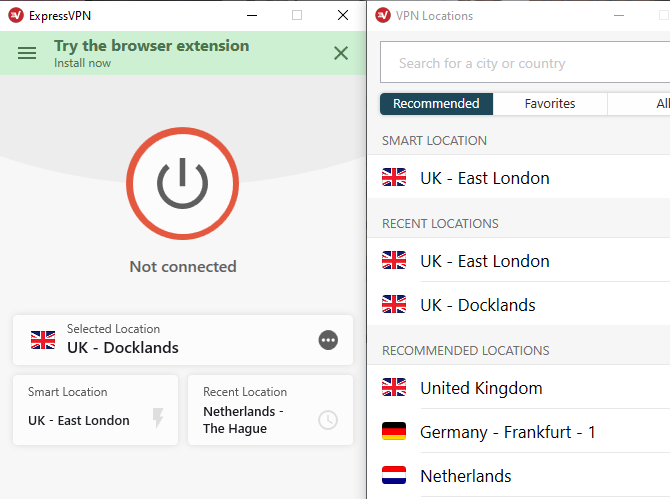
With that in mind, MakeUseOf recommends ExpressVPN. ExpressVPN protects your privacy, provides outstanding connection speed, and has servers all around the globe. MakeUseOf readers can grab an exclusive 49% discount on an ExpressVPN subscription, so give our top-ranked VPN a try.
VPNs Protect Your Privacy
When you use a premium VPN, you're giving your privacy an instant boost. A VPN isn't perfect. It won't protect against malware or block tracking scripts online. That isn't what a VPN does. It can make accessing certain content easier, and it definitely makes it more difficult to pinpoint your location, which is excellent for many VPN users.
There are many VPN providers out there. ExpressVPN is one of MakeUseOf's top recommendations, but there are lots of excellent paid VPN alternatives, too.