If you've got Skype, you'll want to know about the Trojan T9000.
It's malware that records your conversations, both video-calls and text messaging, and is virtually undetectable to security suites. And because it's a Trojan, you won't even know about it.
But it's actually the latest version of a previous threat detected in 2013 and 2014. So what does this update mean for you? How does it install itself? And what can you do about it?
What Is the T9000 Trojan?
The T9000 Trojan provides backdoor access to your private information, automatically capturing encrypted messages, taking screenshots, recording audio files and documents sent via Skype.
The really worrying thing about it is that its simple code is smart enough to recognize and evade 24 different security suites that might be running on your system upon its own installation. This includes big names like BitDefender, Kaspersky, McAfee, Panda, TrendMicro, Norton, and AVG.
Even worse, you're the one who's accepted the Trojan. The problem is, many of us have clicked a download without knowing quite what it is, especially on work computers when you think it's something specifically to do with a job. Indeed, this is exactly the actor vector veing used so far. Palo Alto Networks, who identified the malware, say:
"We have observed T9000 used in multiple targeted attacks against organizations based in the United States. However, the malware’s functionality indicates that the tool is intended for use against a broad range of users."
The T9000 was apparently distributedthrough a spear phishing campaign email to companies in the USA. These emails typically masquerade as an individual or firm you know, encouraging you to download an attachment, which in truth is dangerous, and utilises vulnerabilities.
This malware, however, has a multi-installation process that checks whether it's being scanned by security products at every stage then customizes itself in order to sidestep this detection. Its creators really have gone above and beyond to avoid being found out. (This is a more advanced version of the T5000, which was revealed to have targeted the automotive industry, rights activists, and Asia-Pacific Governments in 2013 and 2014.)
Then the Trojan sits silently on your PC and collects juicy information, sending it automatically to the central servers of the hackers.
Why's It Doing This? Intelligence!
Josh Grunzweig and Jen Miller-Osborn, researchers at Palo Alto Networks who identified the Trojan, say they uncovered a directory labelled "Intel" on the system of a T9000 victim. And that's its whole purpose: collect a range of personal details on a victim.
The aim of all hackers is the same: leverage in order to obtain financial gain. This is no different.
The T9000 aims to capture monetary data, trade knowledge, intellectual property, and personal information including usernames and passwords.
You can't underestimate how important your private data is: even though Personally Identifiable Information (PII) like your name, address, cell number, and date of birth can be sold on the Dark Web for surprisingly small amounts, just imagine if a hacker hit the jackpot and gained a whole stash of personal information!
If the T9000 were used to exploit medical institutions, that would be particularly concerning.
Though it's only been exposed as targeting companies, the Trojan could be utilised elsewhere to similar effect – namely, home PCs. For all we know, that's already how it's being used. It would certainly still acquire private data, but a further warning must go to anyone using Skype for NSFW chats.
We've seen how the so-called "Celebgate" ruined reputations and caused major ripples on the Internet, but you don't have to be in the public eye to be vulnerable. The Snappening, in which the images of an alleged 20,000 Snapchat users were leaked online, is a prime example of this.
The abhorrent practise dubbed "sextortion" involves a victim being blackmailed into surrendering money or further adult material; otherwise, whatever content a hacker already has on him or her is released online.
It's an increasingly-widespread concern, and has even evolved to take further control of the victim by tricking them into downloading malware that collects details of family and friends. This allows direct threats of leaking the material to those who the victim might seek solace with.
What Can You Do About It?
According to Palo Alto Networks, the security suites the T9000 checks for include the following big names:
- Sophos
- Comodo
- Norton
- AVG
- McAfee
- Avira
- BitDefender
- Kaspersky
In addition, it also adapts to these less-well-known security solutions: INCAInternet, DoctorWeb, Baidu, TrustPortAntivirus, GData, VirusChaser, Panda, Trend Micro, Kingsoft, Micropoint, Filseclab, AhnLab, JiangMin, Tencent, Rising, and 360.
If you're an average user, you probably have one of those running. But don't panic.
Here's the most important thing: beware any Rich Text Format (RTF) files in your email inbox. Those used to deliver the T9000 Trojan take advantage of the CVE-2012-1856 and CVE-2015-1641 vulnerabilities in Microsoft Office software. Meanwhile, keep your eyes open for any Windows request concerning "explorer.exe". You should be alerted of this when you open Skype with a simple message asking for your permission.
Don't open it. Deny access.
Otherwise, you should always abide by good downloading practises, whether you're at work or at home. Learn how to spot a questionable email, and apply those lessons no matter who you're supposedly contacted by. And ensure you're using Skype in the most secure and private way possible.
As businesses are at the moment largely under attack, firms need to educate their staff in the latest security measures. If you're an employer, alert employees of this vulnerability.
What Else Can Be Done?
Be careful about what information you're sharing on Skype. If it's sensitive information, maybe the messenger service isn't the best place to exchange that sort of data. Remember, those infecting PCs with malware are also hoping to harvest intellectual property and trade secrets.
Skype has assured the press that they're looking into the T9000 Trojan and its implications.
But what measures are you taking? What tips should businesses give to their staff? Let us know your thoughts below.
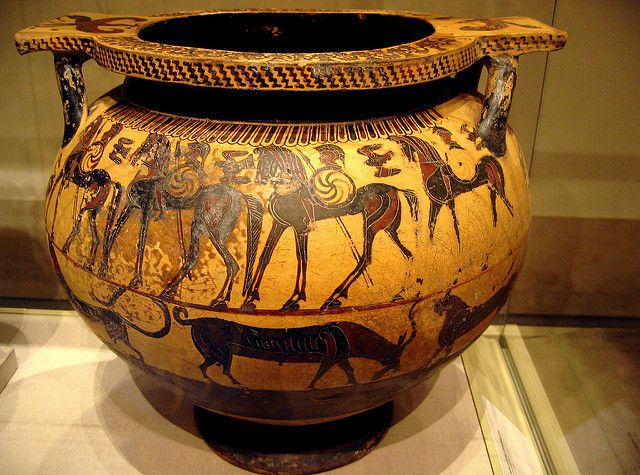
Image Credits: scene of the trojan war by Xuan Che; System Lock by Yuri Samoilov; and New Webcam by Hannaford [No Longer Available].