In theory, not only are Tor users, who explore the Internet through Onion networks, able to visit all the pages a typical user can, but they also enjoy added benefits including searching the Deep Web.
The important thing about Tor is anonymity. But new research suggests users are either being blocked outright or have to jump through additional hoops on many sites.
What's Happening?
Users of Onion networks are being penalised for wanting an extra level of encryption, of security, and of anonymity, according to a recent research paper.
The Universities of Cambridge and California-Berkeley, University College London, and International Computer Science Institute-Berkeley published their findings as Do You See What I See? Differential Treatment of Anonymous Users, focusing on how some 2 million daily users of Tor are treated.
It's something annoyed users have complained about in the past, but this study is the first of note to confirm that 3.67% of the top 1,000 Alexa sites (a service that analyses web traffic data) block anyone trying to access them via a known Tor exit node.
If you're unfamiliar with Onion networks, they essentially let you surf anonymously by relaying your requests through proxy servers that further encrypt your data at each step. The exit node is the final step, the last router that allows you onto the Deep web.
Except users are finding that they're faced with a substandard service from some websites, CAPTCHAs and other such nuisances from others, and in further cases, are denied access completely. The researchers argue that this:
"[D]egraded service [results in Tor users] effectively being relegated to the role of second-class citizens on the Internet."
Two good examples of prejudice hosting and content delivery firms are CloudFlare and Akamai -- the latter of which either blocks Tor users or, in the case of Macys.com, infinitely redirects. CloudFlare, meanwhile, presents CAPTCHA to prove the user isn't a malicious bot. It identifies large amounts of traffic from an exit node, then assigns a score to an IP address that determines whether the server has a good or bad reputation.
This means that innocent users are treated the same way as those with negative intentions, just because they happen to use the same exit node. A Tor user complained:
"[CloudFlare doesn’t] appear open to working together in open dialog, they actively make it nearly impossible to browse to certain websites, they collude with larger surveillance companies (like Google), their CAPTCHAs are awful, they block members of our community on social media rather than engaging with them and frankly, they run untrusted code in millions of browsers on the web for questionable security gains."
Why You Might Want Anonymity
To understand why some sites frown on anonymity, we have to look at the positives of it too. Not to preach to the choir here, but sometimes, you need to stay anonymous. Researchers point out that:
"[Anonymity networks] often provide the only means for citizens to access or distribute censored or restricted content without a threat to their privacy or even safety."
Anyone can create a Tor site or server. It's not easy, but you could.
The Deep web -- and the Dark web in particular -- is increasingly thought of as something sinister, and indeed, illegal trades flourish, including identity fraud, drugs, and taboo porn. ISIS are even using it in an attempt to hide their identities. The media's attitude, as with most things, is "what have you got to hide?" But it's certainly not all bad.
PRISM; why emails can never be secure from Big Brother; the UK's Snooper's Charter: Staying off-the-grid certainly sounds a fine idea when faced with this degree of state surveillance...
You might be trying to operate around repressive countries' Internet blocks, trying to dodge DRM copyright and read ebooks, or even researching something the Surface web doesn't like.
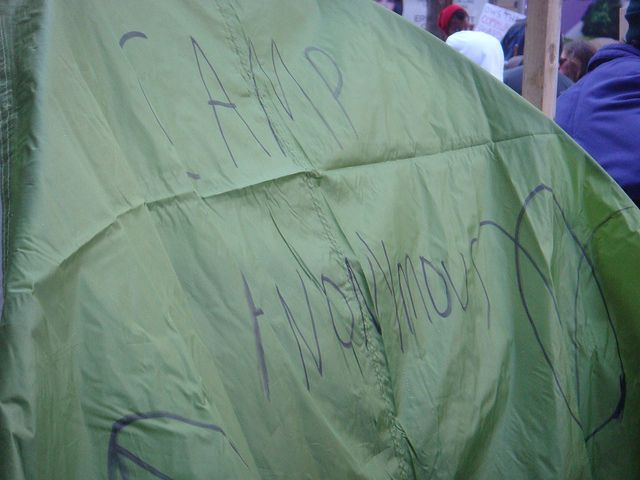
Take Anonymous itself. The hacktivists aim to make society safer -- anonymously. It means that people can make a stand without getting unwanted attention. Sometimes it backfires, but most of the time, altruism wins out.
Why Are Tor Users Becoming Victims?
On the flipside of the coin, however, some want to stay hidden due to nefarious purposes, and that's what sites blocking users are trying to address.
Those running the sites want their visitors to be accountable for their actions: for what they do, and for what they say on the Internet. Government and public-funded sites -- including the European Central Bank, senate.gov, and the US Mint -- largely deny Tor users access, for example. Nonetheless, in many such cases, like healthcare.gov, visitors using the everyday "Surface" web are immediately asked to register their email address (although not doing so doesn't prohibit the use of the site in general).
You could argue blocking anonymous commenters is a way of combating trolls; creating fake profiles for abusive reasons -- sextortion, grooming, cyberbullying -- has just become illegal in the UK, and while Tor users aren't completely untraceable, it would make work harder for trackers.
Blocking Onion networks isn't solely about comments, though. It's also in a bid to protect the site's services.
Hulu blocks anyone using Tor exit nodes, and when one user complained to them, the response was:
"Tor's mostly used for pirating, that's the main reason we're against it as a company."
You may argue this is counter-productive, but to lift the block, you still have to go through a lengthy process in order to be "whitelisted."
If a site sees bad traffic from one IP address, they're understandably going to block it, even if that means excluding benign Tor users too. That's a fair prerogative, especially if it avoids cyberattacks such as Distributed Denial of Service (DDoS) compromises, the like of which Moonfruit recently suffered.
What Can You Do About It?
Unfortunately, there's not a great deal you can do. However, many are turning to Tor's "Don't Block Me" project, which describes itself as:
"A gathering of affected user communities, the internet at large, TPO speakers, and the central Tor themes and use cases around the ListOfServicesBlockingTor in order to encourage these sites to stop blocking people merely for using Tor. This project also develops, documents, and promotes Best Practices for services to use instead of indiscriminately blocking Tor as a whole. Another subproject works to remove Relays from RBL and other blocklists."
It's not futile: while commenting and account sign-up are still not allowed, the popular gaming site, GameFAQs lifted the block on Onion networks. CloudFlare are also reportedly considering removing CAPTCHAs and other hurdles.
It's worth finding out and further supporting those sites that are part of the "We Support Tor" campaign.
Do you blame sites for wanting to protect themselves against bad-intentioned Tor users? Would you do the same? And what else can be done to both include anyone using Onion networks, and keep services safer from anonymous attacks?
Image Credits: stressed businessman by Marcos Mesa Sam Wordley via Shutterstock, Onions by Global Panorama; Camp Anonymous by Jagz Mario; and Commercialization by Kevin Wong.