<firstimage="https://www.makeuseof.com/wp-content/uploads/2010/05/identitytheft_thumb.jpg" />
The Internet's a great place for working together and building a better world, but it also has its dark side. Every year billions of dollars are made in a number of different cyber crimes, and the victims are usually people like you and me.
It's natural that you'd want to avoid being such a victim, and there are a number of things you can do to protect yourself and your family. Let's take a look at the top five computer crimes out there, and what you can do to help keep yourself safe.
Malware
Let's begin with the obvious, shall we? If you use a computer, you're vulnerable to malware. And if you're vulnerable to malware, you're enabling crime on a mass scale.
Malware, as I'm sure you're aware, refers to viruses, Trojans, worms and other software that gets onto your computer without you being aware it's there. Back in the early part of the century, most such software's primary aim was thrill. The people writing the software found it amusing to write a program that exploited security flaws just to see how far it could spread.
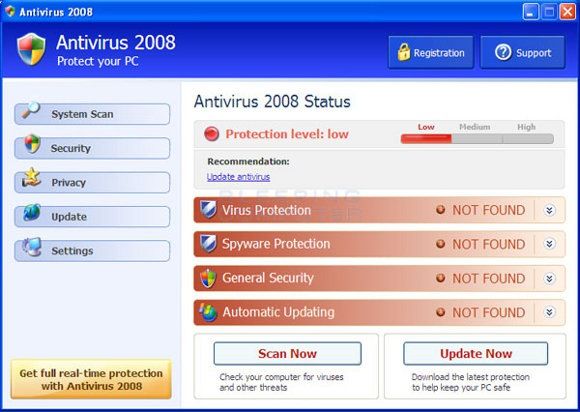
Today the incentive for making such software is generally more sinister and the reason it makes the list of the top five computer crimes. In some cases a piece of malware will pretend to be a legitimate piece of software, and will ask you for money to remove it:
Never, ever give money to programs you don't remember buying. Not all malware tries to extract money from you directly, however. Many simply embed themselves into your computer in order to make use of it. Black-hat hackers may intend to launch an attack against a government or institution, and will use a network of compromised machines to do so. This sort of network is referred to as a botnet, and is a key tool of the trade for a number of Internet crimes.
Of course, whatever the motivation, such software is a drain on your computer's resources so it's best to be protected against it. If you're using a Windows computer it's best to ensure you have proper anti-malware protection. My recent article about the 10 best free antivirus programs is a great place to start.
Just as important as any software, however, is common sense. Don't download software from sites you're not sure you can trust, regardless of what operating system you run. Avoid pirated software: it may seem like a good way to save money, but frequently you're also getting some malware thrown in.
In general just use common sense before opening any sort of file, because you don't want to compromise your system.
Identity Theft
Identity theft easily makes the list of the top five computer crimes. In America alone there are almost 9 million victims of identity theft every year. The concept is simple: someone gains access to your personal information and uses it for their own benefit. This could range from a black-hat hacker stealing your online banking account login and password to getting access to your social security number and using it to pretend to be you. Such people can make themselves a lot of money with your personal information, and screw you over in the process.
Never connect to your bank account on a public computer, or using a WiFi access point you're not absolutely sure you can trust. The same goes for using your credit card or Paypal account to pay for something.
The most important thing is to never share any personal information - such as your bank account number, your social security number or any information a fraudster could use to steal your identity - in an email, instant message or any other form of unencrypted communication. None of these communication channels were designed to be secure, and as such are not the proper way to share such information.
When logging into your bank, ensure the communication is secure by verifying the address begins with "https" instead of "http" - this means your connection to the site is secure.
Never use your credit card at a site you're not sure you can trust.
If you get an email from your bank, your credit card company, eBay or any other service with access to financial information asking you to "update your personal information" ignore it. This is a common ploy used by fakers. Make sure you're very familiar with the interface of all such sites, because fakers can severely take advantage of you if you're not careful.
Nigerian princes do not ask strangers online to accept a money transfer.
Ever.
Seriously.
The Federal Trade Commission of the United States has a lot of good information about identity theft applicable to all countries; check it out.
Cyberstalking
People leave a lot of information about themselves online. Such information can leave you vulnerable to cyberstalking, a term that essentially refers to using the Internet to stalk someone in the traditional sense.
Cyber stalking is essentially using the Internet to repeatedly harrass another person. This harassment could be sexual in nature, or it could have other motivations including anger or outright hostility.
The town of Mesa, Arizona's website shares some solid advice for avoiding cyberstalkers:
When you are online, only type things you would actually say to someone face to face. Think about how what you say might be interpreted without the context of body language and voice.
Mesa's website includes more tips on the subject, so be sure to check it out.
Child Pornography
It's tragic, but the Internet is often used to exploit children. What's perhaps even sicker is that people make money doing this.
Your child being exploited in this way is extremely unlikely, but that doesn't mean it's not worth trying to protect them. Anti-child-porn site asacp.org recommends the following core strategy:
1. Install and use parental control software on all computers.
2. Know what sites your children frequent and monitor their online activity.
3. Foster communication with your children so they understand the potential dangers they may be exposed to online.
Good advice, all of it. The site also recommends a number of tools for achieving these goals, so check it out. Also check out Tim's article, which points out 5 sites that promote internet safety for kids.
Spam
This one needs no introduction. These annoying email messages aren't just an irritant; they're big business.
Named for the amazing Monty Python sketch about a processed meat product, spam is illegal in many countries. So how does it spread? For the most part, using the botnets explained in the "malware" section of this article. As such, one thing you can do to help stop the spread of spam is to ensure your computer is protected from such malware.
If you don't want spam in your inbox, the simplest thing to do is to switch to Gmail. This email service seems to have a spam problem licked, and it is the only service I personally use.
Know another spam-free service? Share it in the comments below.
There are a few other things you can do to slow spam from getting to your inbox, however. Tina suggests five ways to protect & hide your email to stop receiving spam. You could consider using a temporary email addresses as a means to avoid spam, as an article by Will points out. Finally, be sure to report particularly evil spam to the authorities, as Dean explained recently.
Conclusion
The Internet's not a place without crime, but it's also not a place where you're helpless. As this article points out, there's lots you can do to protect yourself and your family on the Internet.
Can you think of any others beyond this list of the top five computer crimes? What are some other strategies for protecting yourself? If so please share in the comments below; a little knowledge can help us all a lot.