In my last post I spoke about Windows system commands and touched on a few portable network analysis tools. Today we will look into those applications and another few portable applications. We will talk about Angry IP Scanner, WireShark and Network Stuff. Using these applications in conjunction with the commands we covered previously, you should be able to accurately troubleshoot and diagnose your network issues. Let's start with the Angry IP Scanner first.
Angry IP Scanner allows you to not only scan a network for all hosts, you can also identify open ports to find security holes and identify Mac addresses and host names. This tool is very handy for finding what machine is using the same host name or IP address on your network.
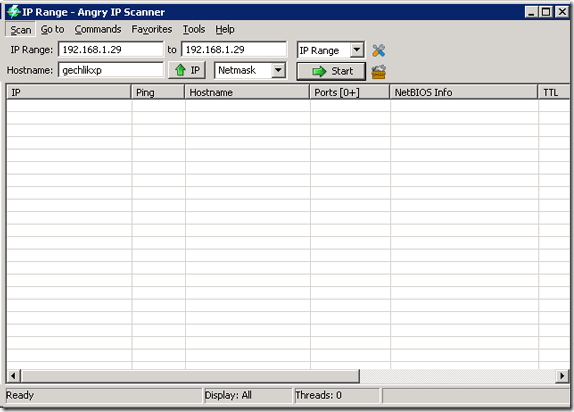
You can simply copy the EXE file out of the zip to your memory stick and run it. Once you run it you will see this screen that allows you to specify what you want to scan for. You can also customize the fields it grabs when it scans such as Host name, IP, net bios info, TTL, web port detected and much more.
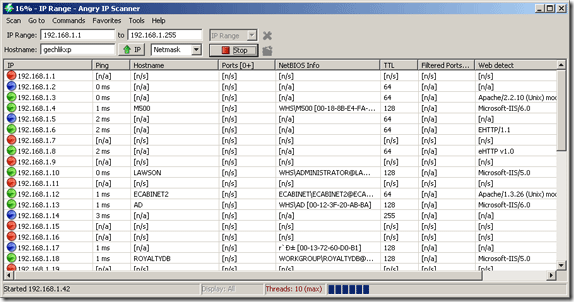
Your machine's name and IP address will automatically appear in the fields as you can see above. You can modify them to suit your needs. I ran a scan on my local subnet and returned the following information:
You can use this information to also track down rogue DNS or DHCP servers lurking around your network or spot a machine not named using the company standard at a glance.
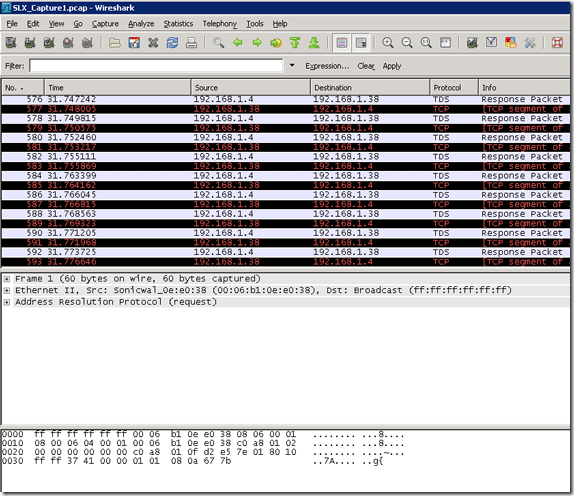
The next portable network analysis tool is WireShark which is a network sniffer. A network sniffer allows you to copy a segment of traffic on your network and all the conversations back and forth. This is the ultimate tool for diagnosing network issues because it gives you all the details you need to figure out the issue. But it is up to you to decipher the information and use it accordingly.
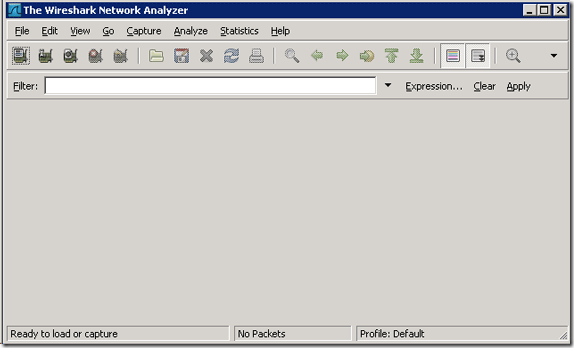
You can download portable WireShark from here [Broken URL Removed] and they explain to you how you can build your own (as most security experts would do!). If you do not run this as shown as a portable application you will need to have WinPcap installed or running to capture traffic but not to analyze already captured packets. Once you run the application you will see a screen that looks like this:
From this screen you would go to Capture "“> Interfaces to choose what you want to capture. You can choose your network adapter and create filters for what types of traffic you want or want to hide because a network can be very noisy and busy as you can see by my unfiltered capture below.
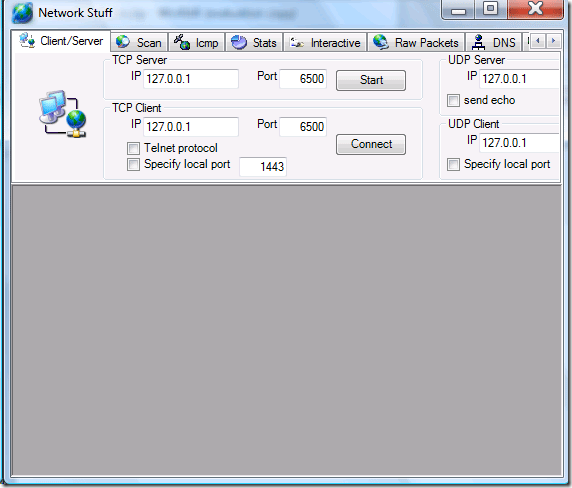
And the last portable network analysis tool from my toolkit that we will be covering today is Network Stuff available from this link here. I was unable to bring up the author's website though which should be here. Once you download and run the exe file you will see this.
This is bringing out the big guns for me as this can scan and query everything from one easy to use console. It covers lots of console commands as well such as Telnet, Ping, Traceroute, Whois, DNS resolver, MAC address getter , IP address scanner, view TCP/UDP/ICMP stats and a lot of other stuff jam-packed into one package.
This is just another glimpse into some of my network kung-fu tools. If you have specific questions let us know in the comments!