Nearly all smartphone spyware promises to log everything a phone does while remaining undetectable. A compromised device is traceable via GPS, can have its incoming and outgoing text messages and call logs stolen, and even have remote access to photos, videos, and browser history.
Installing spyware on an iPhone was once no mean feat. Apple's stringent security settings and iOS architecture made installing spyware difficult. That hasn't changed---but spyware developers have learned how to circumvent many of these iOS spyware defense mechanisms.
Think someone has compromised your iPhone? Wondering how to detect iPhone spyware? Here's what you need to know.
Is There a Legitimate Use for Spyware?
Spy software, by its very nature, is designed to snoop on people. It is for this reason that anyone reading this who is contemplating installing such software probably doesn't care what I have to say about any aspect of doing so. If you're already thinking about doing this, you've probably already ethically justified the practice in your head.
Whatever your reasoning for doing so, it's always worth considering how you would feel if someone did the same to you.
Most spy software is marketed in a very broad way. Not only is it advertised to snoopers who want to track the location of an individual, or spy on someone's smartphone usage but it's also marketed as a legitimate security tool. This is ethically questionable at best, and a massive breach of privacy at worst.
Unfortunately, we can't change the minds of those who are already engaged in the practice, but we can try to redress the balance for those drawn in by dishonest marketers.
Parents should reconsider using spyware to trace their children. There are free and safe ways to share the location from an iPhone (and other iDevices), which you can find at the bottom of this article.
At times, spyware marketing targets employers. Employers should not use spyware to keep tabs on your workforce. If you want to use a Mobile Device Management (MDM) policy on your employee's hardware, don't use a BYOD policy alongside it.
There is no doubt MDM policies are important. But a personal device should remain private and installing MDM software compromises device privacy.
Is It Difficult to Install Spyware on an iPhone?
For a long time, no spyware in the world could do all it claims without voiding the target iPhone's warranty. That includes spying on any activity, tracing any location, uploading video and camera images, and so on.
Parents installing iPhone spyware void the warranty on their kid's devices. Paranoid spouses and partners invalidate their other halves' iPhone warranty, and the same goes for employers and so on.
"Unauthorized modification of iOS is a violation of the iOS end-user software license agreement and because of this, Apple may deny service for an iPhone, iPad, or iPod touch that has installed any unauthorized software."
That is because the most potent forms of iPhone spyware require a jailbreak before allowing access to the full gamut of private data. Not all legal interpretations of jailbreaking and warranty provisions agree with Apple's interpretation. But if something happens to the device while jailbroken, Apple can use that against you.
Jailbreaking will also void any AppleCare after-sales warranty. Jailbreaking is fine if it's your iPhone and you understand the risks involved in doing so. Even a jailbreak gone wrong is unlikely to "brick" your iPhone. But jailbreaking someone else's device without their knowledge isn't very nice.
iPhone Jailbreaking Spyware Installation
In comparison to Android, installing iPhone spyware is difficult. Apple takes a commendable hardline approach to security and privacy. The iPhone isn't designed to run non-Apple software which is seen as a security violation. Tampering with system-level software isn't illegal, but Apple can and will detect any changes, even if you take your device in for a basic repair.
Whereas, Android does things differently. Unchecking a box in the Settings allows the installation of non-Google Play apps. The process is instantly reversible, too, but allows those apps to remain.
Jailbreaking involves loading custom firmware onto the iPhone. Jailbreaking allows greater freedom on the device, allowing users to run unsigned software. The most advanced spyware is always unsigned, for two reasons: the spyware would breach iOS permissions, and Apple would never allow that level of spyware on the App Store in the first place.
Is Jailbreaking Easy or Quick?
In the early days of jailbreaking, new vulnerabilities were found frequently. It was relatively easy to jailbreak iOS, allowing for the installation of custom apps (and in this case, spyware). It is possible to jailbreak an older iOS device in minutes, with a little preparation.
More recent versions of iOS are more secure and have taken much longer for jailbreak developers to crack. At the time of writing, jailbreaks exist for iDevices running up to iOS 12.4. The jailbreak process is remarkably quick, too. The latest jailbreak method (at the time of writing) takes a couple of minutes to complete and doesn't require you to connect the iPhone to a computer at any point.
There was a long period during which jailbreakers could not find a new vulnerability to exploit. Installing and updating the most invasive forms of spyware during that period was difficult. Unfortunately, through Apple's internal incompetence, iOS version 12.4 introduced a vulnerability that jailbreakers pounced upon, quickly releasing a new option.
Are Unsigned iOS Apps Safe?
Unsigned apps can potentially include malware. If the root SSH password remains unchanged once the jailbreak is complete, malware could run riot on your phone. With no Apple guardians to oversee software, you must rely on third-party developers to be the judge and jury. If you think about it, spy software is malware marketed as valid software.
Jailbroken iPhones and other iOS devices can sometimes have problems running legitimate App Store apps. Developers have ways of detecting a jailbreak and can now prevent jailbroken devices from using their services. One example would be DIRECTV which delivers streaming video and another reported app is Skype for iOS.
Many banking apps are also restricted for obvious reasons, as is PayPal. Getting these apps working again involves playing a game of cat and mouse between developers and the jailbreak community.
Jailbreak-Free iPhone Spyware
The period of time where there was no option to jailbreak the latest iOS version sent spies toward different spyware options. A raft of jailbreak-free spyware apps are now available. The jailbreak-free iPhone spyware apps cannot provide the same level of data as spyware installed using a jailbreak exploit.
Jailbreak-free iPhone spyware uses the iCloud credentials of the victim and exploits the data found there. The spyware app can then use integrated iCloud services such as Find My iPhone to track the target device, or read through the victim's iMessage history without alerting anyone. The spy is not only violating the privacy of the target, but they are also handing over the password to the target's entire Apple identity
How to Detect iPhone Spyware
There is no guarantee you will find evidence of the iPhone spy software. As you might expect, developers design spyware to remain hidden from view and to operate without leaving a trace.
Instead, you are more likely to encounter other issues with your iPhone relating to spyware. For example, you might find the evidence of a jailbreak, rather than a spyware app. You might also note your device using more battery, or your data allowance drops faster than usual.
The biggest telltale sign is the Cydia app. The Cydia app installs during the jailbreak process and is the portal to jailbroken unsigned apps and unofficial iOS tweaks. Even if the spy hides the Cydia from the home screen, you should still find it using the iOS home screen search function.
There is no guarantee of finding Cydia, and the careful snooper will probably try all they can to hide any signs of a jailbreak. Other apps to search for that might suggest a jailbreak include Installer, Icy, SBSettings, Absinthe, and Installous. Similarly, installing an app like PayPal (mentioned above) might reveal an issue if the app refuses to run.
To find out more methods for spotting iPhone spyware, check out how to protect yourself from illegal spying of all kinds.
How to Remove iPhone Spyware
Jailbreaking is a game of cat and mouse between Apple and the jailbreak community. Keeping your iDevice up to date and performing all iOS updates reduces the chance of installing the most invasive forms of iPhone spyware.
Apple is quick to patch security vulnerabilities and jailbreak exploits. Rolling your iPhone back to an older firmware version is rarely an option. As such, even if someone has jailbroken your iPhone, reversing the issue is simple.
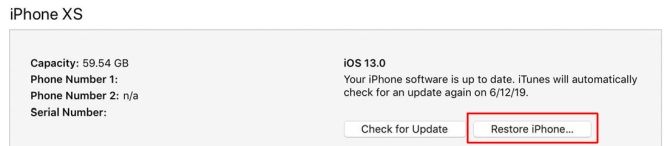
If you suspect spyware is on your iPhone, a factory reset is the easiest option to restore your device---and your privacy. Even though Apple keeps track of the unique identification numbers (UDIDs) of jailbroken devices via the App Store, it seems restoring your phone "as new" removes all traces of the jailbreak.
To restore your iPhone on a macOS or Windows PC, first launch iTunes. Then, head to Summary > Restore iPhone. You can opt to Back Up Now before the firmware restore process begins, which will save your personal data.
If you do choose to backup and restore, there's a chance some evidence of the jailbreak will remain, but the jailbreak itself will be gone. If your phone needs attention from Apple (either as part of a 12-month warranty or the extended AppleCare package) an Apple technician may refuse you service if they detect evidence of a jailbreak.
Should Parents Install Spyware on Their Kids iPhone?
There are two easy to use iPhone spyware alternatives for concerned parents.
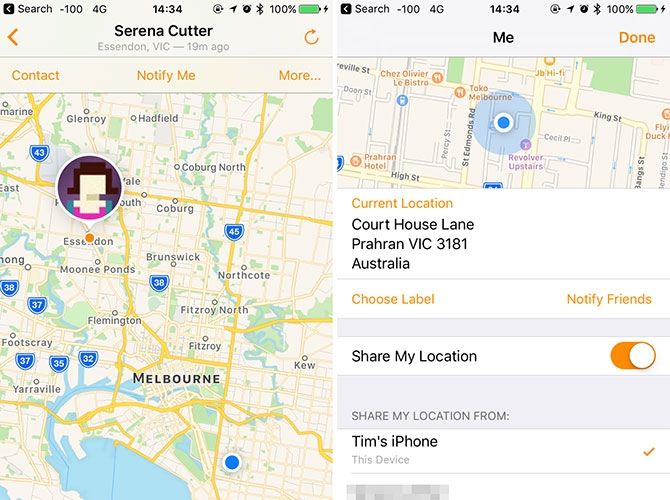
Find My Friends works across Apple devices and uses Apple IDs to connect friends and family. By authorizing a friend or family member to view your location in Find My Friends, they will be able to see where you are whenever they like. If you have young children you can enable location sharing within Find My Friends, then use iOS restrictions to prevent changes to Location Services.
The Find My Friends app works best with the consent of the user. You can use Find My Friends as an opportunity to establish a system of trust with your children. The app will not record messages, phone calls, or camera activity because it is not spyware. It is a tool for staying in touch that you can also use to open a personal safety dialogue with your kids.
The second way to share location between iOS devices is via the Messages app. Simply open a conversation on the device, hit the "i" button in the top-right corner, and hit Share My Location or Send My Current Location. You can choose to do so for an hour, for a day, or indefinitely. You can then stay in touch by opening the same conversation on another device and hitting the "i" button.
iPhone Spyware Is Invasive and Dangerous
iPhone spyware is dangerous, for a multitude of reasons, including data theft, malware, fraudsters, and more. It's also a lesson in ethics and trust between you and your kids; it might lead to a conversation with your employer regarding personal space and respect.
Remember, spyware isn't the only iOS security issue you should know about. Despite a superior security record, your iPhone is still susceptible to malware and other vulnerabilities.