What's in your wallet? That famous credit-card company tagline takes a more serious meaning these days. Credit and debit cards with an embedded Radio-Frequency Identification (RFID) tag are now the norm.
This is one place you use RFID. But there are plenty more places you use RFID technology, probably without even realizing. The RFID market was worth over $10 billion in 2015, forcast to rise to over $13 billion in 2020.
So, what is RFID?
What Is RFID?
Radio-Frequency Identification is the use of radio waves to read, capture, and interact with information stored on a tag. Tags are usually attached to objects, and can be read from several feet away. Furthermore, the tag doesn't always have to be in the direct line-of-sight to initiate interaction.
An RFID tag is an easy way to assign a unique identity to an object. Additionally, they do not need an internal power source, while a tag can be as small as a grain of black pepper. Meaning they are easily embedded almost anywhere -- hence their popularity.
How Does RFID Work?
A basic RFID system comprises two parts: the tag, and the reader.
Tag
The RFID tag has an embedded transmitter and receiver. The actual RFID component contained in a tag has two parts: an integrated circuit for storing and processing information, and an antenna to receive and transmit a signal. The RFID tag has non-volatile memory storage, and can included either fixed or programmable logic for processing transmission and sensor data.
Tags can be passive, active, or battery-assistive passive.
A passive tag is the cheapest option, and features no battery. The tag uses radio energy transmitted by the reader.
An active tag features an onboard battery, periodically transmitting its credentials.
A battery-assistive passive tag also features a small onboard battery, but is only activated when in the presence of an RFID reader.
Furthermore, a tag may be either read-only, or read/write. A read-only tag has a factory assigned serial number used for identification in a database, while a read/write tag can have specific custom data written to the tag by the user.
Reader
The RFID reader features a two-way radio transmitted-reciever (transciever), sometimes referred to as an interrogator. The transceiver transmits an encoded radio signal to interogate the tag. The radio signal essentially wakes or activates the tag. In turn, the tag transponder converts the radio signal into usable power, and responds to the reader.
Types of RFID System
We generally classify the type of RFID system by the type of tag and reader. There are three common combinations:
- Passive Reader Active Tag (PRAT): The reader is passive, only receiving radio signals from an active tag. Because the tag is battery powered, the transmit/reception range can be from 0-2,000 feet (0-600m). As such, PRAT is a flexible RFID solution.
- Active Reader Passive Tag (ARPT): The reader is active, transmitting an interrogator radio signal, receiving authentication signal replies from passive tags.
- Active Reader Active Tag (ARAT): The reader is active, and interacts with active or battery-assistive passive tags.
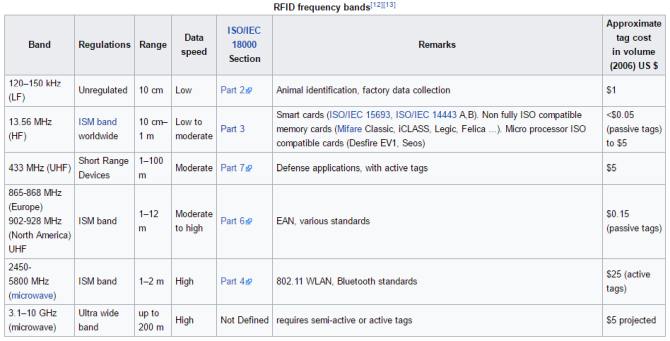
In addition to the RFID system type, RFID uses a set of regulated frequency bands. See the frequency band table below for an understanding of certain frequencies and their uses.
What is OPID?
Optical RFID (OPID) is an RFID alternative that uses optical readers. OPID operates in the electromagnetic spectrum between the frequencies of 333 THz and 380 THz.
How Much Data?
The amount of information stored on an RFID tag varies. For instance, a passive tag may only store up to 1024 bytes of information -- that's just one kilobyte (KB). Laughable in terms of modern storage capacity, but enough to store a full name, identification number, birthday, SSN, credit card information, and so much more. The aerospace industry, however, use passive ultra-high frequency RFID tags with 8KB storage to track part history over time. These could store a massive amount of personal data on.
Common RFID Uses
RFID tags are everywhere. Because they're easily attached to almost anything, have no power requirement, and are potentially minute, they are used in all walks of life, including:
- Goods management and tracking
- Person and animal tracking
- Contactless payments
- Travel documents
- Barcodes and security tags
- Healthcare data management
- Timing
RFID is also making waves in the ever-growing smart home market. (Check out Ian Buckley's tutorial on making a smart lock using an Arduino and RFID). In 2010, the cost of RFID significantly decreased. At the same time, RFID reliability increased due to global drive in RFID standards. Suddenly, an extremely reliable but cost-effective tracking or identifcation system was available.
Security
The sudden surge in RFID has created security issues, too. Most recently, the advent of contactless payment cards featuring an RFID tag has come under scrutiny. Nefarious individuals were "skimming" payments from contactless cards using portable payment terminals, all while the RFID-enabled card resides in the targets pocket or wallet. If you're worried about this type of fraud, check out Joel Lee's run-down on RFID blocking wallets.
In the U.K., another example involves RFID tags stored in passports. When first introduced, the encryption on the new U.K. passport was cracked within 48 hours. Additionally, reports emerged that criminals were stealing post containing a new passport, scanning the RFID tag for the data, and then sending them on their way.
RFID is Here to Stay
RFID is an enormous industry. We use it almost everyday. The package that arrived at your house, the card you paid for your lunch, your door-opening smart home hand-implant, and more, all use RFID.
And as it RFID evolves, so will its uses -- exciting times!
What do you use RFID for? Do you use it in your smart home setup? Have you bought an RFID blocking wallet? Let us know your RFID tricks and tips in the comments below!