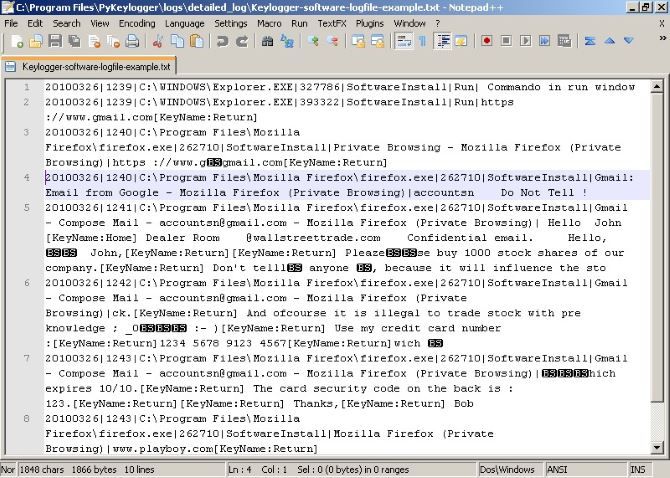
How would you feel if your computer was keeping a log of everything you type in an insecure text file sitting on your hard drive? Someone (or some piece of malware) who knew where to look could unearth every password and credit card number you've typed, along with your recent browsing history and more.
If you're using an HP computer to read this article, I've got bad news for you. Security researchers have discovered that a problem with a driver in some HP computers recording everything you type. Everything you've recently typed on your computer could be neatly sat in a text file with no protection.
Read on to find out how this happened and how you can combat it.
The Issue: Conexant Driver Woes
The root of the problem lies in an audio driver manufactured by the company Conexant. As you may know, drivers allow the variety of devices you own to interface with your computer. If you build your own PC, you'd have to install most of the drivers on your own. When buying off the shelf, they're already included.
In this case, HP computers such as HP EliteBooks, ProBooks, ZBooks, and Elites were shipped with a version of the Coxenant audio driver that includes a keylogger. Even scarier, this started on computers sometime around December 2015, and affects other PCs with the Conexant driver installed.
As the user of an affected machine goes about their business, the keylogger stores all of their typed data in an insecure text file. While this file starts fresh every time you reboot your computer, it's easy to recover older versions of a file. Plus, if you're smart and back up your PC regularly, the log file with your older keylogged data was probably included in the backup.
Is This Another Superfish?
Thankfully, this situation is far less dangerous than Lenovo's Superfish debacle a few years back. That violated your browser's secure HTTPS connection to websites, allowing it to snoop on secure connections to places like your bank. Conversely, the HP keylogger doesn't send the data anywhere.
HP can't access it, so the risk lies with a person gaining physical access to your computer. Someone who knows about this exploit could easily search for the file containing all your typed information, with obviously disastrous results.
According to HP's vice president, the keylogger function was accidentally added during development. It seems that they used it to check to make sure that certain key combinations were triggering audio shortcuts as intended. This is a crude solution, and fine during development, but clearly a problem when shipped to consumers.
Am I Affected?
Even if you don't have an HP computer, you should still check to see if you have the Conexant audio driver installed. You can do so by typing Device Manager into the Start Menu to open that utility. Expand the Audio Inputs and Outputs header and look for Conexant Audio or something similar. If you have anything by that name installed, continue to check if the keylogger is on your system. You're safe from this if you don't have Conexant drivers.
Next, you should check for the log file of your keystrokes. Using the File Explorer, navigate to C:\Users\Public and look for a file named MicTray.log. That's the log file. If you don't see it, you're probably safe. If you do, then you need to take action to stop this driver from recording your keystrokes.
How Can I Fix This?
Thankfully, HP has already released updates for these drivers to remove the keylogging functionality and delete the log file. Before these, the best fix was to rename or delete the file C:\Windows\System32\MicTray.exe (on a 32-bit computer) or C:\Windows\System32\MicTray64.exe (for 64-bit machines). However, this could cause your audio keys to stop working properly, so you should install the patches instead.
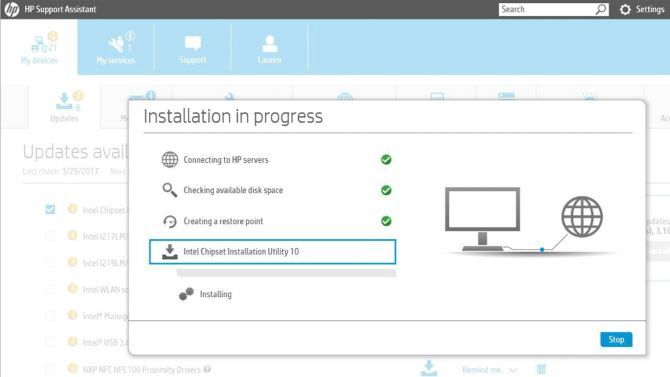
HP released the audio driver patches through Windows Update. Type Windows Update into the Start Menu and click Check for Updates to make sure you're up-to-date. If you don't see them or want to download the audio driver updates manually, install the HP Support Assistant software, which makes updating your audio, network, and other drivers easy.
Your other option is to search for your PC model on HP's Support Page and manually download the new Conexant audio driver from there. The Support Assistant is easier, though.
That's all you need to do to cut off this problem. After applying the updates, the driver won't log your keystrokes anymore and the log file is gone. However, you should still be careful about older versions. Because the log file resides in the Public users folder, it likely got included in your system backups. Check out the history on whatever backup software you use to make sure that an older copy of MicTray.log isn't in your backup. If you find anything, erase it.
Battling Keyloggers in the Future
As keyloggers go, this one was relatively minor. It didn't send your data to anyone, only a person with physical access to your machine could access its contents, and HP fixed it quickly. However, more keyloggers are out there, and they're scary. The idea of having someone read every key you hit on your computer is pretty scary. What's more, some keyloggers can also capture what's on your clipboard and even take screenshots without your knowledge.
Unfortunately, there's no longer a good free anti-keylogger solution. We wrote about several of them years ago, but they've since eliminated their free plans. Your best defense against keyloggers is running a good antivirus program that will catch them before they affect you. We also recommend running a scan with Malwarebytes Free occasionally for an additional layer of protection.
Were You Affected by This Keylogger?
If your HP computer contains an affected version of the Conexant driver, you can apply these patches quickly and return to using your computer safely. This underlines basic security principles that keep you safe: make sure you're installing updates automatically and use an anti-malware solution to defeat rogue applications.
Don't let this incident be a reason to avoid HP in the future -- Lenovo is far worse when it comes to security.
Do you own an HP computer that had this keylogger running? We want to hear from you if you removed it after learning about this exploit!
Image Credit: Sviat Studio via Shutterstock.com