When Edward Snowden fled from the United States to a Hong Kong hotel room, and then on to Russia, he took with him a massive cache of documents from the American intelligence establishment. These would form the main part of the Snowden revelations, which ultimately showed the extent to which ordinary people have been spied upon by the services they use, and by their own governments.
But it wasn't just NSA and CIA documents that were leaked by Snowden. He also managed to bring light to the secretive inner workings of the British, Australian, Canadian and New Zealand intelligence agencies, known collectively along with the USA as the Five Eyes.
Few people expected Canada's intelligence agencies to have the same level of sophistication that GCHQ and the NSA has. After all, Canada is a country of 30 million people that is more famous for its livable cities, harsh winter climate, progressive domestic policies and a somewhat non-interventionist foreign policy above anything else. But according to a recent article by Pierre Omidyar's First Look Media, in association with the Canadian Broadcasting Corporation, Canada possesses a sophisticated array of cyberweaponry, and is able to compromise and decimate networks across the world.
Hack The Planet
Most governments have some form of cyberwarfare facilities, which allow them to commit acts of digital sabotage and break into computer systems, both foreign and domestic. America has the NSA. Britain has GCHQ. Even North Korea has some form of cyberwarfare capabilities, although experts aren't certain to of what extent. So, it should come as no surprise that Canada too has a cyberwarfare organization, known as the Communications Security Establishment.
It's a relatively small organization, with just under 2000 employees. Much like the NSA and GCHQ, the CSE is rather secretive about its activities and capabilities. What we do know about it comes from what they have publicly and willingly disclosed, and from what we have learned through leaked documents, many of which came from Edward Snowden.
One thing that isn't entirely certain is the scope to which the CSE acts. Where are their targets, and who are the state and non-state actors behind them?
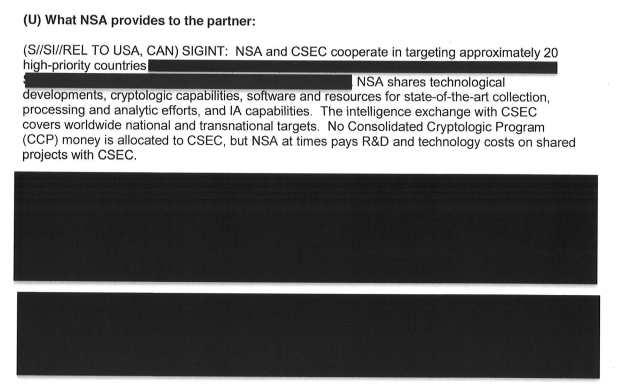
This question was answered in a leaked NSA memo, titled "NSA Intelligence Relationship With Communications Security Establishment Canada (CSA)", dated 3 April 2013. The memo puts the relationship between the NSA and CSA into a historical context, and then goes on to establish the current levels of cooperation between the two organizations. The paper has some redacted lines, and is peppered with intelligence agency jargon, but notably it shows that the CSA has worked with the NSA to 'access and exploit' the networks for a number of foreign intelligence targets, including ones found in the Middle East, North Africa, Europe and Mexico.
The paper also continues by mentioning the NSA and CSA have worked together on targeting 20 'high-priority countries'. These are listed later on in the document, although we can't know for sure which countries they are, due to this information being redacted.
Capabilities and Capacities
Also mentioned in the document is a brief assessment of the CSA's ability to produce cryptographic software, and software that can assist in the compromising of computer systems. It mentions that Canada is a noted importer and consumer of 'U.S. IA products', due to an inability to produce them domestically.
That's hardly surprising. Canada is nothing like the USA, which has the largest defense budget in the world, and invests billions of dollars into private sector companies to build surveillance hardware and systems.
But what kind of software has Canada been importing?
One of the Snowden documents reveals that the CSE has access to QUANTUM; a family of malware applications that were developed by the NSA in order to surreptitiously gain access to a system's hard drive, and to disrupt its operations.
According to First Look, there are up to five variants of QUANTUM being used at RAF Menwith Hill, which is a crucial intelligence site in the United Kingdom, based just outside of Harrogate, North Yorkshire. There's QUANTUMSKY, which prevents a user accessing certain websites; QUANTUMCOPPER, which corrupts downloaded files; QUANTUMHAND, which impersonates Facebook; plus two others. Details on the remaining two unmentioned malware programs are scant.
https://www.anrdoezrs.net/links/7251228/type/dlg/sid/UUmuoUeUpU53667/https://vimeo.com/88822483
Most intelligence agencies have some form of internal cottage industry that is responsible for the production of custom malware. A few years back, Iran's nuclear ambitions were temporarily halted after a number of centrifuges were destroyed as a result of Stuxnet; a malware program that was spread through infected USB drives, and caused the centrifuges to unstoppably spin out of control, which ultimately caused severe damage to the sensitive machinery. It was suspected that the United States and Israel were responsible for Stuxnet. It seems plausible that Canada also has this internal capability, although at a smaller scale.
Outside of specific malware applications, the CSE seemingly has a trained, skilled workforce, able to disrupt and compromise networks and applications. A leaked PowerPoint presentation from the Communications Security Establishment called 'CSEC Cyber Threat Capabilities - SIGINT and ITS: An end-to-end approach' gives a top-down assessment of what they're capable of. This includes pro-active system defense, but also mechanisms to "disable" and "destroy adversary infrastructure", as well as distribute malware.
Another Version Of The Truth
In recent years, governments have seen the opportunities presented by social media for creating and communicating a certain narrative. Many countries, including China, the UK and Israel, have entire units of employees whose job is to pump propaganda on to Twitter, Facebook and in the blogosphere.
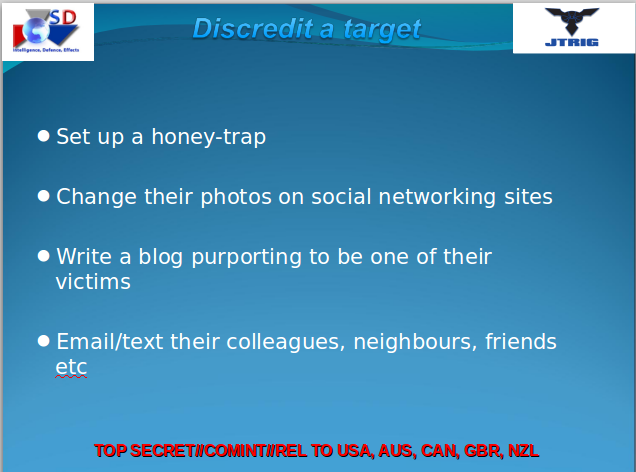
It has also been revealed, courtesy of these documents, that Canada is also capable of 'deception tactics'.
These include 'false flag' actions, where a criminal act is falsely attributed to a state or non-state actor, as well as other mundane, but also troubling, deception tactics. These include rigging online polls to produce a favorable result; distributing information that is known to be false; and 'astroturfing' social networking sites with deceptive or dishonest messages, in order to drown out contrary messages, and to present one viewpoint as a dominant one.
What Does This Means For Canadians?
Most sensible people see the need for an intelligence service. The 21st century is a dangerous one, and it's only getting more dangerous. But, it's also undeniable that having an intelligence service that operates with impunity and no judicial oversight is ultimately harmful to privacy, security and freedom.
This was a sentiment echoed by Ronald Deibert, director of Citizen Lab, speaking to the Canadian Broadcasting Corporation.
"These are awesome powers that should only be granted to the government with enormous trepidation and only with a correspondingly massive investment in equally powerful systems of oversight, review and public accountability,"
Whether there's the political will to actually reform the Canadian intelligence services remains to be seen, especially with the ever-present threat from extremist terrorists such as ISIL.
Some doubt that the CSE's strategies for protecting Canada are helpful, or just exacerbating the threats that exist. I spoke to Cory Doctorow, the Canadian author of "Little Brother" and founder of Boing Boing. He said:
"Securing Canada's electronic infrastructure should start by finding and fixing as many flaws in the code, OSes and systems that Canadians, Canadian business and the Canadian government and its institutions rely upon for life and death. The security services prioritise offense - -- finding bugs and keeping them secret so they can use them to hack "bad guys" -- and that means that they're constitutionally incapable of doing their defensive duty to us without compromising their main tactic.
Whatever bugs they're [The CSA] discovering and weaponizing are also being discovered and exploited by foreign spies, crooks petty and organized, and voyeurs and creeps of every description. By leaving us vulnerable to these threats so that they can play Tom Clancy live-action role-playing games, they are abrogating their duty to the Canadian public and Canada itself. It is depraved indifference on a grotesque scale."
Timing Is Everything
It's no coincidence First Look Media released these documents just weeks before the Canadian parliament is due to vote on Bill C-51, also known as the Anti Terrorism Act, and whilst this bill is still being very much debated. We have learned the extent to which the Canadian security services can compromise and disrupt computer networks, and reveal how they've been doing it with little to no judicial oversight, and it's *worrying*.
But nowhere near as worrying as Bill C-51 is. This controversial piece of legislation would see domestic intelligence agency, CSIS (Canadian Security Intelligence Service) more easily use the sophisticated infrastructure of the CSE.
Civil liberties groups also worry that C-51 could also result in a curtailment of the freedom to protest, freedom of expression, and a weakening of privacy rights.
These revelations alone are unlikely to scupper Bill C-51. That will only happen as a consequence of people getting outraged and putting pressure on their representatives. However, what we've learned highlights the powers already possessed by the Canadian security services, and raise the question of whether they should be extended even further. Especially when Canadians are already being heavily surveilled, both at home, online, and even at the border.
But what do you think? Is it ever acceptable to mass-surveil citizens and hack computers without a warrant, when it's in the name of public safety? Would you like to see more judicial oversight of the CSE? Whatever you think, I'd like to hear it. Leave me a comment below, and we'll talk.