Social engineering is an important term in the security world, but you might not be familiar with exactly what it means. While it's a broad subject, there are specific types of social engineering that we can examine to learn more.
Let's look at social engineering as a concept so you can avoid falling victim to it.
What Is Social Engineering?
In the realm of security, social engineering is the act of manipulating people to steal private information from them, or make them give up such confidential details. Social engineering relies on taking advantage of human nature, which is usually the weakest link in an otherwise strong system.
Social engineering, unlike many other technical attacks, doesn't try to break into computer systems directly. While a hacker might write a program that tries to brute-force someone's password or exploit a bug in software, social engineering relies only on tricking or manipulating victims to do something that the attacker wants.
While social engineering predates the internet age (think about sales tactics that pressure you to buy something you don't want), the practice has become much more widespread online.
Even with strong passwords, top-notch security software, and physically secured machines, a deceived person can be a vulnerability and still invite a security breach into a company or their own setup.
Key Elements of Social Engineering
Most people recognize blatant scams. Since awareness about these tricks has risen over time, the fraudsters who run them have to regularly change up their tactics to keep them viable.
As a result, specific social engineering schemes adapt over time. However, a lot of these tricks use some mix of the following elements:
- Scare tactics: If a scammer can make you fearful that something bad is about to happen, you're more likely to follow along without thinking critically. For example, they might pretend to be the government and demand tax payments at the threat of being arrested.
- A sense of urgency: To pressure you to act before you think, a lot of social engineering scams call for immediate action, lest you "lose your account" or similar.
- Posing as a legitimate company: To convince you that they're not phony, attackers will use authentic-looking elements in their email or other communication.
- Vague wording: Because social engineering attacks typically go to many people at once, most aren't specific to you. Generic wording and a lack of a particular reason for the communication are signs that you're dealing with a fake.
Common Types of Social Engineering
Next, let's take a look at some common forms of social engineering to see how it plays out.
Phishing
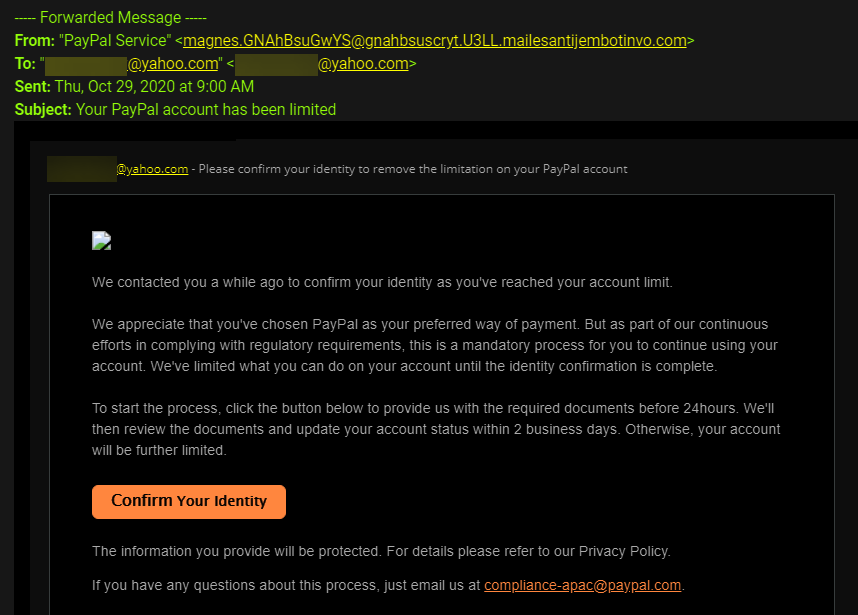
You're probably familiar with phishing. It's one of the most common kinds of social engineering. This is an attack where someone pretends to be a legitimate entity, usually over email, and requests sensitive information.
It often professes to be from PayPal, Apple, your bank, or another trusted company, asking you to "confirm" your details or review a suspicious transaction.
To protect against phishing, you should never click links in emails, and remember that legitimate companies don't ask for sensitive information in this way. Be sure you're familiar with the various forms of phishing as well.
Phone Scams
Phone scams are more old-school than email phishing, but they're still popular. In these schemes, someone calls you claiming, for example, to be from your credit card company and asking you to confirm your details because of suspicious activity.
They might also pretend to represent a computer firm that needs to "fix virus infections" on your machine.
Over the phone, a thief can establish a more personal connection than via email. But if you pay attention, it's easy to know when you're on the phone with a scammer.
Baiting
While it's not as widespread as the above forms, baiting is a form of social engineering that preys on human curiosity. In these attacks, a fraudster leaves an infected CD or USB drive in a place where they hope someone will pick it up. If you then insert the media into your PC, you could end up getting hit by malware if the contents of the drive run automatically.
This attack is more complicated, since it uses physical media. However, it illustrates that you should never plug a flash drive or other device into your computer if you don't trust it.
Tailgating
This attack, unlike the others, relies on the scammer being physically present. Tailgating refers to the act of gaining access to a secured area by piggybacking on another (legitimate) person.
A common example of this is a door at a workplace that requires you to scan a keycard to get in. While it's common courtesy to hold the door open for someone behind you, most companies don't want you to do this. The person behind you could be trying to sneak into an area where they shouldn't be, preying on your kindness.
This one is mostly applicable to business use, but it's smart to remember that you should protect physical access to your computer, too. Someone who's able to sneak onto your machine without you looking could do a lot of damage.
Scareware
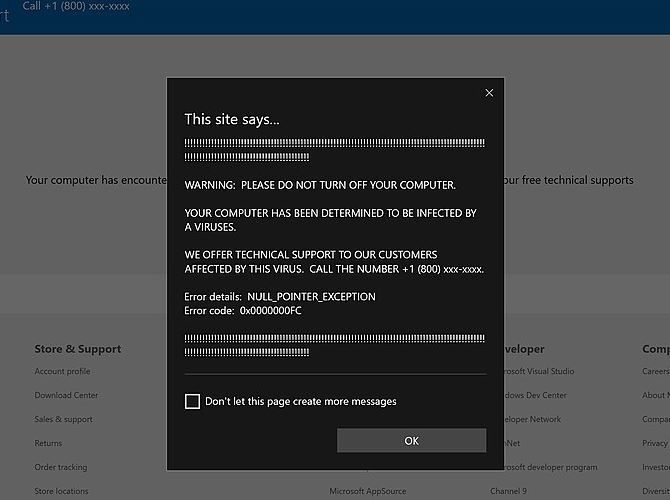
Sometimes called "scareware," this serves as kind of a mix between phishing and malware. In these attacks, you're threatened using bogus messages, in the hopes that you'll pay money to a scammer or give up sensitive information.
One common form of scareware is fake virus warnings. These aren't dangerous on their own, but trick you into thinking that they're actual signs of infection on your device. Scammers hope that you'll fall for the fake and either send them money to "fix" the infection or download their software, which actually is dangerous.
Another common scaring technique is extortion emails. In these, you receive an email from someone who claims to have compromising content of you, or similar. They demand a payment to prevent them from releasing the video or image to all your friends. Of course, they don't actually have such information; they just hope that you believe them.
How to Stay Safe From Social Engineering
As we've seen, social engineering takes many forms and can often be difficult to detect. To protect yourself from these and similar attacks, keep the following in mind:
- Do not trust emails. Emails are one of the easiest forms of communication to fake. Never click a link in an email unless you were specifically expecting it. It's always safer to visit websites directly.
- Don't act without thinking. If you receive a message that preys on your emotions, it's likely designed to trick you. Stop and think when you feel especially worried or curious, as you're more likely to make hasty decisions in these instances.
- Always confirm suspicious information. If someone claims to come from a certain company, ask them information to prove it. If they respond with vague excuses, they're a liar.
Social Engineering, Exposed
Even if you never fall victim to a complicated exploit or have your password cracked, you could still get hung out to dry by a social engineering scheme. By recognizing these common scams and thinking critically when these situations arise, you can avoid playing into a fraudster's hands.
Meanwhile, social engineering isn't the only way that human psychology is exploited online.
Image Credit: wk1003mike/Shutterstock