Whenever you register with a site, you're trusting them with your personal details. They have access to your email address at least, and probably much more---including, of course, your password.
But how can you tell if the site is taking proper care of your private information? Why is it a problem when sites store account details in plaintext? And what can you do about it?
What Is Plaintext? Why Is It a Problem?
Plaintext is precisely what it sounds like: your password is stored exactly as you write it down.
Let's say a site you use has been hacked. The hacker has access to a list of accounts with passwords noted down. Let's suppose your password is "Pa$$w0rd" (and we really hope it isn't). The cybercriminal can scan down the list, find your email address, and easily read that your "secure" login is "Pa$$w0rd".
The big issue is, it doesn't matter how obscure and unguessable your password is. Because anyone with access to your account can read it, as easily as you're reading this.
It's even more worrying if you use the same password across numerous platforms. MakeUseOf advises against doing that for this very reason, as do all security experts. Nonetheless, we understand the temptation to stick with a password that's easy to remember.
But if you do, you risk hackers using leaked plaintext sources to get into your online banking accounts, your Facebook, and whatever else you duplicate the password on.
An estimated 30 percent of eCommerce sites store their passwords in plaintext. This isn't something we can easily overlook.
It's not confined to small, independent sites either. Some big companies have been caught out, including the NHL, Match.com, LinkedIn, the National Trust, and Vodafone. Fortunately, they've since implemented more secure methods of storage.
How Can Passwords Be Stored Securely?
What's the alternative to plaintext? Actually, there are a few options for storing passwords, but not all are as secure as they may initially sound.
Many sites use a hash function, which transforms your password into another set of digits. If a hacker gets in, they can only see these randomized characters. It's a flawed algorithm, however, because every time you enter your password, it generates the same hash. The system then makes sure those digits correlate to give you access to your account.
And yes, they can be cracked, especially through brute-force attacks.
If you run an eCommerce site, though, you should instead use salted hashes. These take the same principle, but additional digits bookend your password before it enters the hash algorithm.
Slow hashes are even better---they limit the number of times a hacker can attack the data set per second. If a cybercriminal knows it will take them longer to crack a password, they're less likely to target the account.
How to Tell If a Site Stores Passwords as Plaintext
It's difficult to tell unless you work for the company in question. And if you do, you need to alert your technical team that storing private data in plaintext is unethical.
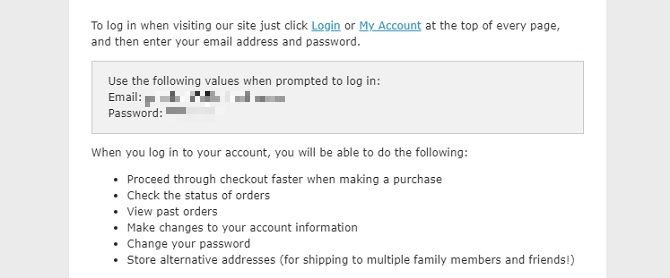
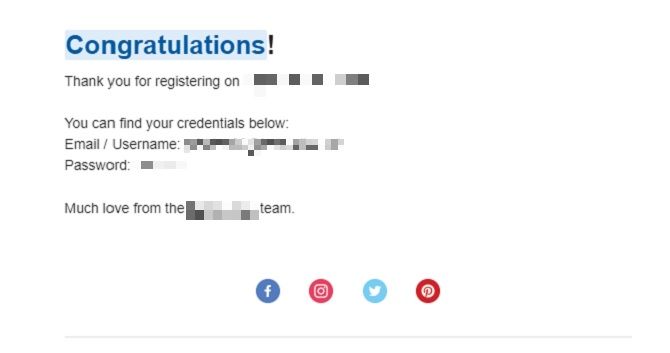
Still, there's a good indicator you can go by. If you set up an account and the site sends you an email which lists your password, it's likely stored in plaintext.
They're certainly unsecure if you click "Forgot Password" and they send it to you via email. If it had been encrypted, they wouldn't be able to do this. Instead, you'd need to verify that it's your account then reset your password altogether.
Emails aren't secure anyway. They're susceptible to hacking. Even if the site doesn't store your information as plaintext, sending you a detailed message isn't safe.
If you want to take a thorough approach to your online actives, use a placeholder password when registering with an online store. Then click "Lost My Password" (or a variation of it) and check your email. If the only option is to reset it, do that.
Otherwise, if you can clearly see your placeholder password in your inbox, this is a worrying sign.
You could also check out Plaintext Offenders, a site dedicated to highlighting firms which don't take your security seriously enough.
What Can You Do About It?
If you suspect a site stores your password in plaintext, email them. Ask them to address your concerns.
You should hear back from them, in which case they will likely assure you that they use encryption to secure your details. But don't let that dissuade you. Don't believe the myth that encryption is fool-proof.
Otherwise, we need to talk about damage limitation. Don't use the same credentials for everything. We know it's tempting and you probably figure there's no real harm in it. But you're wrong. We're sure a firm you've used in the past has been hacked already. That could be MySpace, Tumblr, Dropbox… or a whole host of sites.
Check by typing your email address into Have I Been Pwned.
Do Password Managers Secure Plaintext?
Password managers are a neat way of keeping your credentials safe without having to remember them all. You use one secure password to access the manager which knows the rest for you.
But they don't help fight sites using plaintext. The manager is a storage system for your security, not the site's. Your private data will still be readable if anyone gets into your account.
Nonetheless, you're clearly interested in keeping your private information to yourself, so there are definitely benefits of using password managers.
Plaintext Passwords Are Not Secure!
Plaintext just means your password is stored exactly as you write it. And that's a problem because hackers can easily read it. Be sure to read up on credential dumping and how to protect yourself.
Once registering with a site, any welcome emails you received shouldn't have your password included; if they do, that's indicative of an account using plaintext. If you click "Forgot my password", and they email the actual password to you, that's a definite sign your personal information is held in an unsecure manner.
Concerned a site isn't doing this securely? Email them about your worries. They might assure you that they use encryption, but nothing is unbreakable. If not, find out how reputable websites should store passwords and tell them.