This is a short tale of blocks, broken trust, compromised accounts, cover-ups, and one of the most popular Minecraft community sites. The accounts of more than 7 million members of Lifeboat were compromised earlier in the year, and the data has reportedly been sold to the highest bidders on the Dark Net.
7 Million Users!
The massive breach was discovered in January by Troy Hunt, the security researcher behind the Have I been pwned? breach notification site. He received a tip off concerning the data from someone actively engaged in the trade of hacked login credentials, and had received other data from the individual in the past.
"The data was provided to me by someone actively involved in trading who's sent me other data in the past"
His discovery exposed the lackadaisical security in place at Lifeboat, and the equally lackadaisical sequence of events that followed the breach.
Lifeboat runs servers for custom Minecraft Pocket Edition environments. It allows players using the mobile version of the extremely popular voxel-builder to participate in the various multiplayer modes, such as Capture the Flag, or Survival. Lifeboat users connect to a community server, registering their desired username with an email address and password. Pretty standard stuff.
Unbeknownst to the users, Lifeboat then hashed the passwords with the now infamously weak MD5 algorithm, meaning the passwords would have been easy to crack using basic (and easily available) tools.
Following the Leak
When a company experiences a data breach involving the personal details of its users, the common course of action is to inform them. Letting the users know their private email address and password for their account has unfortunately been acquired by a potentially malicious entity. It seems quite reasonable.
Lifeboat neglected to do this seemingly basic task, instead deciding that as the breached data contained no financial information, triggering a silent site-wide password reset would likely suffice. Even then, the security flaw story continues, with Lifeboat advising their users to create short passwords – literally the opposite of widely accepted password generation practice.
"By the way, we recommend short, but difficult to guess passwords. This is not online banking."
However, despite Lifeboat's claims of a site-wide password reset, many users contacted in relation to the breach responded negatively, saying that they did not receive any such reset email, or a notification when entering the game or connecting to a Lifeboat server.
"It's bad that they were breached in the first place, but not telling us about it is even worse"
What Went Wrong?
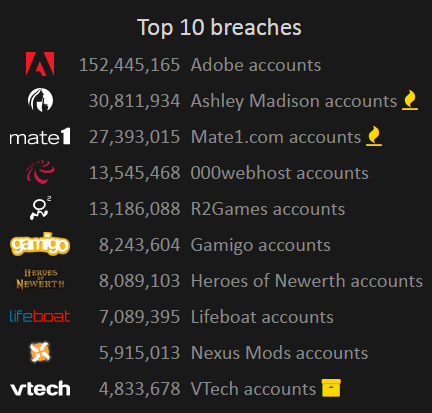
The Lifeboat data breach reads like a list of what not to do in the event of an emergency. The breach itself has immediately placed at #7 in the Have I been pwned top 10.
It is the systematic failings that have attracted such attention. Not only were the email address and passwords breached, but users were actively encouraged to weaken their own chance at ensuring personal data security by an ill-advised password recommendation. Then to really top it off, Lifeboat had hashed the passwords using an easily breakable encryption method.
MD5
If Lifeboat had chosen the opposite advice – use longer passwords featuring a combination of letters, numbers, and symbols – the data would have been much less attractive for those data traders. Consider this: a password containing six alphanumeric characters is limited to just 626 (26 lowercase, 26 uppercase, numbers 0-9). Even using basic online tools, security researchers or malicious parties will have that password cracked in weeks. Offline tools, using a powerful computer, it'll be cracked in seconds.
Compounding the terrible password advice was their own poor security housekeeping. Lifeboat opted for unsalted MD5 hashes to obscure the plaintext passwords. While offering a base level of protection, MD5 was designed to offer extremely fast, resource-light encryption. At its genesis, these qualities made MD5 a pretty handy tool. Most retail computers simply didn't have enough power to crack the encryption.
However, times change, and our home computers are vastly superior to those developed just a decade ago, drastically undermining the effectiveness of anything hashed using MD5.
Unsalted Passwords
And just to rub salt in the wound, Lifeboat made a final blunder. The MD5 hashes protecting the passwords were unsalted. This means the plaintext passwords weren't combined with a unique value for each user account, making the cracking and matching process that much easier.
Salting basically ensures each individually hashed password is entirely unique, even if they contain identical characters. Anyone wishing to view the passwords would have to crack each hash individually.
Safe to Return?
Lifeboat haven't issued too many statements concerning the breach. Their stance, I believe, remains that while the data breach is reprehensible, as they do not hold any additional personal information or financial information, the damage should be relatively limited. Lifeboat has also confirmed that MD5 is no longer in use at the site, or on any of its servers.
"When this happened [in] early January we figured the best thing for our players was to quietly force a password reset without letting the hackers know they had limited time to act. We did this over a period of some weeks."
Even if the direct damage is limited, there could be other fallout. People are generally lazy when it comes to passwords, using only a handful to protect all of their online accounts.
While the risk of a single breach exposing a number of accounts is magnified, the lesson should be clear: if you really care about the sanctity of your accounts, your private, personal data and more, use a strong, unique password for each one. So when a service is breached, you won't become a statistic.
By the way, Lifeboat users: it is time to change all of your passwords.
Have you been affected by the Lifeboat hack? Will you trust Lifeboat again? How do you keep track of your passwords? Let us know below!