Is your Raspberry Pi secure? Of course it is. But is it really secure? Is the data on it safe? Can the project be subverted against you?
Now you're thinking.
We've previously looked at the steps you should take to keep your Raspberry Pi secure, but do you understand why? Are you sure you're aware of what is at risk?
If your Raspberry Pi is online at any point during the development or use of your latest project, then you need to be aware of these possibilities.
1. Your Device Is a Target
You may have various purposes in mind for your Raspberry Pi. It doesn't matter. At this stage, just understand one thing: it is a target, just as any connected device is.
Look, this shouldn't be a surprise. While the chances of any mainstream worms or ransomware infecting your Pi are unlikely (Linux is famously resilient against malware), there are other considerations here. Indeed, we're really not talking about virus, worm, or other sorts of frustrating malware. Rather, the risks come from targeted attacks from threat actors with a specific aim in mind.
Usually, this aim involves personal profit, although it could be more destructive. This isn't to say that traditional malware will never be used -- software running on the Pi could be vulnerable, and the device could potentially be used as part of a botnet.
So, it could be something that impacts a media center project, or a games project. More worryingly, it could be an attack that threatens a Raspberry Pi smart home project. Anything you're doing with your Raspberry Pi is a target, really.
In fact, even if your Raspberry Pi project is offline, it could be targeted. We'll come to that in a moment, but first...
2. Does Your Pi Need to Be on the Network?
It's almost a reflex action: when your Pi's operating system is installed, you connect it to your local network. Indeed, if you've installed the OS using the NOOBS tool, it might even be connected already.
And then there's the Raspberry Pi 3, and the Pi Zero W, with their built in wireless networking. While these devices don't automatically connect to your network, the facility is there, ready and waiting. But does your Raspberry Pi really need to be connected to a network?
Sure, if you're using it as a media center or as a retro gaming device, then some network access is probably necessary. And you might want to establish an SSH connection to send instructions, or install software to the Pi for the current process.
But if there's no need for a network connection, then you can keep the Pi offline.
3. Is SSH Completely Secure?
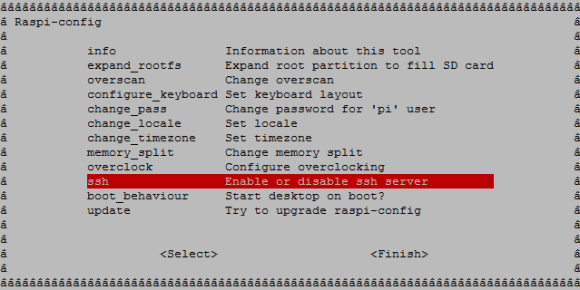
These days, the Raspberry Pi's main operating system, Raspbian Stretch, comes with SSH disabled. (Enabling it is simple: just create a text file, without a file extension, called "SSH" in the boot directory of the SD card.)
It's likely that you've enabled SSH at some point. But is it secure?
For starters, you should have changed your Pi's default username and password. Without doing this, anyone could remotely connect to you Pi over SSH. It won't take them long to login with the default credentials. They might even change the username and password to prevent you from ever connecting to your Pi again!
You can further tighten up SSH by limiting users by username. This can be done in the SSHD configuration file. Open this in nano with:
sudo nano /etc/ssh/sshd_config
At the end of the file, add this line:
AllowUsers [your_username] [another_username]
Press Ctrl > X to exit, saving as you do so. Once you've done this, restart the sshd service:
sudo systemctl restart ssh
Note that you can use the DenyUsers command in the same way to explicitly block attempts to connect over SSH. For the best results, however, disable SSH in the Raspberry Pi Configuration tool when it is not needed.
4. Can Your Raspberry Pi Be Physically Accessed?
Another risk to consider is your Pi's physical location. After all, it isn't all about remote access -- someone taking your Raspberry Pi could prove to be potential dangerous, especially if the device is already attached to your wireless network.
With default credentials set, it would be trivial for an attacker to use the Pi to get onto your home network. Chaos could then ensue.
How you use your Pi can betray its location in your home. For instance, a Kodi media center (using OSMC, LibreELEC, or some other software) will probably be found close to your TV. The same goes for a gaming center. You know that, and so does a potential thief.
This is without even considering your Pi's use. A Raspberry Pi being used as a NAS could already be attached to some valuable data. Unless this is kept strictly out of site, you could find that data going missing quite suddenly. The same goes for using your Pi as a router or hardware firewall. Permitting physical access to a device used in this way could potentially open you up to many attacks. All it takes is for the SD card to be replaced with one running a similar project, but configured to the hacker's specification.
5. What Projects Are Running on Your Raspberry Pi?
The physical and digital risks combine to potentially unseat your security when it comes to the Internet of Things. Smart home projects utilizing a Raspberry Pi can be damaged, destroyed, or simply undermined without the correct attitude to security.
There is probably no situation in which you want your device to be controlled by a stranger. Projects using NFC to unlock drawers or doors, for instance, could be hacked using known vulnerabilities in NFC.
Meanwhile, if the device is being used to display information (some sort of kiosk application) or targeted advertising using iBeacon technology, this could be hacked to relay material curated by a hacker.
Keep Your Raspberry Pi Safe, Secure, and Yours!
It's not difficult to keep your Raspberry Pi secure. Just keep the points above in mind. Here's a recap:
- Is your Raspberry Pi a target?
- Can your Pi run offline?
- Is your SSH secure?
- Can anyone reach the Pi?
- Consider the security of the project.
Once you've got to grips with these concepts and the possibilities they present, it's time to act. Change the password and username, configure SSH, and keep your Pi under lock and key!
Have you faced security issues with your Raspberry Pi? What steps have you taken? Tell us in the comments below!
Image Credit: BrianAJackson/Depositphotos