Do you run a personal blog? Perhaps you're part of the ongoing blogging boom. If you can write well, take beautiful pictures, and capture the mind of audience, there is a lot of money in blogging. It depends on what you're blogging about, too. However, whether you've 10 million monthly views or just 10, your blog may still be a target for hackers.
The relative ease of hacking some blogging platforms make them a low-hanging fruit for some unscrupulous individuals. Additionally, there are numerous hacking methods for the most popular blogging platforms, such as WordPress. I'm going to show you some of the most common, as well as a relatively new play from the hacker's handbook.
Chrome Font Social Engineering
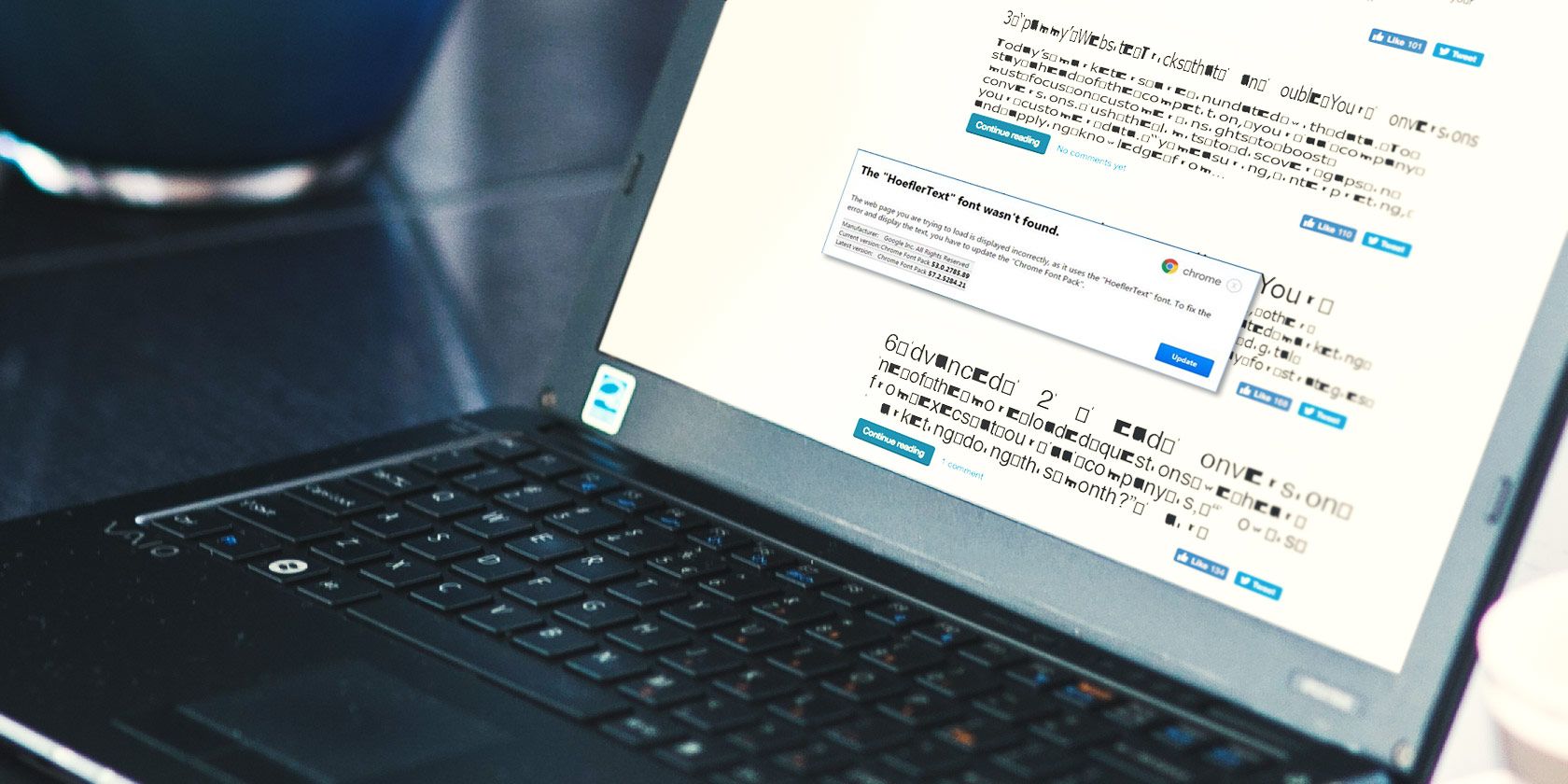
A number of websites have been compromised with a hack that alters the visual appearance of the text. The attack uses JavaScript to change the text rendering, causing it to display a garbled mix of symbols in place of the site content. The user is then prompted to update the "Chrome language pack" in an effort to fix the problem.
The infection process is quite straightforward. If a potential victim meets a set of criteria, including target country and language, and User-Agent (confirmed as Chrome running on Windows), the JavaScript is inserted into the page. Next, one of two potential dialogue boxes then appear, explaining that "The 'HoeflerText' font wasn't found," along with a single option: Update.
The dialogue boxes are carefully constructed lures, but I'll elaborate on that in a moment.
Selecting Update automatically downloads the infected file. Of course, if the user doesn't execute the file, the computer remains free of infection. However, the script creates a fake issue, luring the user into interacting with the dialogue box. It is a classic social engineering ploy, guaranteed to ensnare numerous users.
What Is the File Hiding?
This exploit has been on the radar since December 2016, when security researcher @Kafeine was made aware of a compromised website. The website in question was delivering the infected payload to users. "Next-generation cybersecurity company" ProofPoint shared a detailed teardown and analysis of the hack and potential exploit.
Their analysis details an extensive and dynamic threat ecosystem that targets multiple countries. The payload delivers a type of advertising fraud malware, known as Fleercivet. Ad-fraud malware is used to redirect users to websites, then automatically click on the adverts displayed there. Once installed, the infected system begins to browse the internet of its own accord, in the background.
Why Is This Different?
Social engineering hacks are increasing in frequency. This hack is notable for its specific targeting of Chrome users in combination with detailed lures.
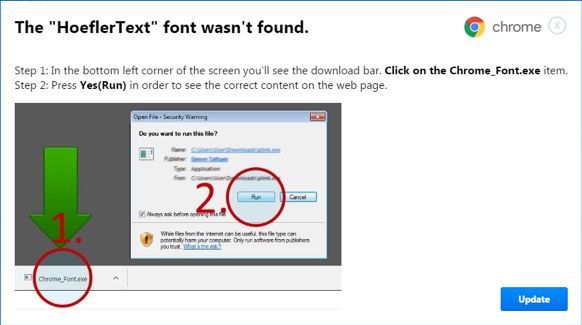
The first dialogue box lure informed the user that "The 'HoeflerText' font wasn't found." To add authenticity to the lure, a box adds details of the supposed current Chrome font pack. Of course, your version will appear outdated, encouraging the user to hit the Update button.
The second dialogue box lure contains almost the same text, but uses different formatting, including an image to "assist" the user toward the malicious file.
Threat actors are finding it more difficult to infect the number of systems required to remain profitable. Therefore, they are turning to the weakest link in the security chain: humans.
Other Hacks Are Available
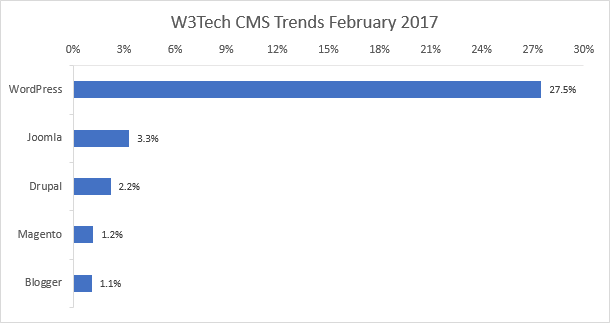
There are billions of websites. In February 2017, WordPress powered around 27.5 percent of the web. Joomla, Drupal, Magento, and Blogger combine to power a further 8.9 percent. The sheer number of sites powered by these content management systems makes them a massive target. (If we round the total number of sites on the web to one billion, 364 million of those are powered by one of the above CMS. This is a gross simplification.)
Similarly, the number of sites run by unskilled and amateur webmasters present easy targets for skilled hackers. That said, a large number of professional sites are equally vulnerable.
Why Did My Blog Get Hacked?
Has your blog been hacked at some point? There are several common reasons why.
- Security -- Your computer was compromised, and you lost login details to an attacker. This could have come from any number of attack vectors.
- Third-Party Application -- Third-party addons, extensions, and widgets can easily become a vulnerability. The sheer number of them make it hard to police security, though exploits are usually patched rapidly.
- Server Compromised -- To save money on resources, millions of websites are hosted on "shared" servers. It has enabled ultra-low cost web hosting, but also creates a chance for hackers to compromise multiple sites.
- Phishing -- Phishing emails are still one of the most popular methods for malware delivery, due to their continued effectiveness. A very popular blog might receive targeted spear phishing emails, tailored to the site owner or contributors.
- Did You Update? -- An outdated CMS, or outdated extension, addon, or widget is an excellent entry point for an attacker.
- Website Security -- Smaller blogs will likely rely upon strong password generation and simply being careful. Larger sites should have additional security protocols to mitigate potential cybersecurity attacks.
Is "ElTest" Coming My Way?
Honestly, who knows? The Chrome font replacement hack has been directly linked to the "ElTest" infection chain. The infection chain is commonly linked to ransomware and exploit kits, and has been active since 2014. There is no clear path for the chain, only to find vulnerable sites and expose their users.
With this in mind, it is always worth considering your site security. Dealing with the points we covered in the last section will go some way to keeping you safe. As we have seen, humans are often the weakest link the security chain. Be that because we forgot to update our CMS or antivirus, or because we were duped by a social engineering attack, we have to take the responsibility of our cybersecurity seriously.
Have you experienced a blog or website hack? What happened to your website? Did you have enough security in place or were you compromised elsewhere? Let us know your experience below!