The Universal Serial Bus (USB) is the double-edged sword that revolutionized the way we interface with our devices. Its plug and play nature has made transferring data between devices simple. USB sticks are not without their faults though. They quickly became the medium for infecting entire networks with viruses and malware.
Enter the USB Kill device, which can completely fry your USB port or destroy your motherboard. It achieves this by charging its capacitors from the USB port and surging the brutal voltage back to the port. This happens several times until unplugged, or the host dies.
Let's take a look at how your can try and mitigate the risks from such devices.
The Basics
Before we get into the finer details there are some simple rules of thumb you can follow:
- Don't insert USB drives you found abandoned on the floor.
- Don't insert USB drives given to you by a random individual.
- Ask trusted people to send you files via the cloud.
- Don't insert USB drives that aren't from well-known suppliers like Samsung, SanDisk, etc.
- Don't leave your computer unattended.
This list should cover most cases. However, USB device security can still be improved.
Protect Your BIOS
In the event you have a machine that must be left unattended, gaining access to said machine is relatively simple. All someone has to do is create a bootable USB drive and boot from the drive into a live environment. This will give them access to all unencrypted files. In the case of Windows, you can even blank out users' passwords. Password-protecting your Basic Input Output System (BIOS) means a password must be entered even before the boot options appear.
Consult your hardware manufacturers documentation on how to enter the BIOS. Generally it's done by repeatedly tapping the Delete key as your computer is booting, but this varies between manufactures. The password setting should be under the Security section in your BIOS.
USBGuard Has Your Back
Do you need to leave a PC or server unattended? If so, you can prevent attacks with an aptly named utility, USBGuard. This is designed to protect against malicious USB devices also known as BadUSB. Examples include USB devices that can emulate a keyboard and issue commands of a logged in user. These devices can also spoof network cards and change a computer's DNS settings to redirect traffic.
USBGuard essentially stops unauthorized USB devices by implementing basic blacklisting and whitelisting capabilities. Ideally you would not allow any USB devices except a select few that you trust. When you plug in a USB device or hub, USBGuard will scan the device first. It then looks sequentially at it's configuration file to check if that device is allowed or rejected. The great thing about USBGuard is that it uses a feature that is implemented directly in the Linux kernel.
If you're running Ubuntu 16.10 or later you can install USBGuard by typing:
sudo apt install usbguard
If you're on one of the older *buntus, you can follow the instructions on GitHub [No Longer Available]. Our example will follow a simple allow which will demonstrate how to authorize a device with a specific id. To get up and running use:
usbguard generate-policy > rules.conf
nano rules.conf
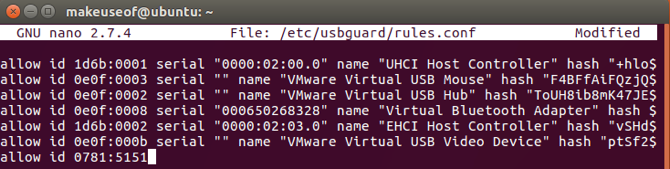
Take a moment to review the policy that's about to be added. This step will add and authorize everything that's currently plugged into your machine. You can remove or comment out the lines for the devices you do not want to authorize.
sudo install -m 0600 -o root -g root rules.conf /etc/usbguard/rules.conf
sudo systemctl restart usbguard
Put It to the Test
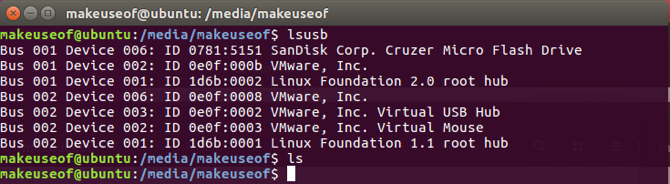
By now, any device you connect to your machine will not function, even though it seems to have been detected. IPlug in a USB drive to verify this by running lsusb to list all USB devices connected to the system. Take note of the SanDisk id, we'll need this later.
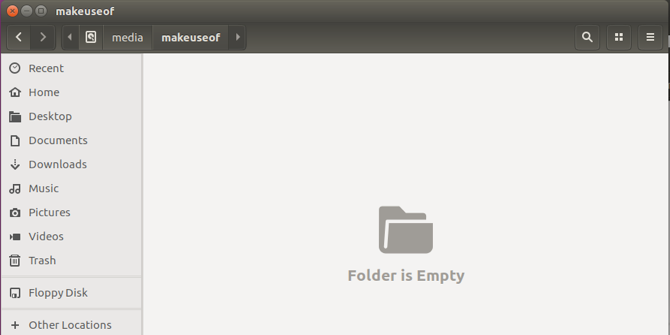
Although the device has been detected in Ubuntu, there is no sign of it being mounted!
To add this device to the list of authorised devices, run the following:
sudo nano /etc/usbguard/rules.conf
Now add the SanDisk id to the rules.conf file to set it as one of the authorized devices.
All it takes now is a quick restart of the USBGuard service:
sudo systemctl restart usbguard
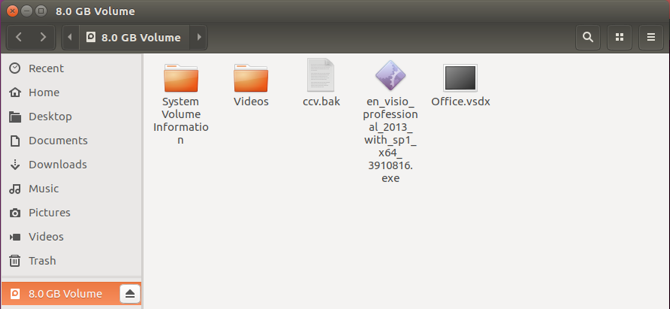
Now unplug, then reconnect the USB drive. USBGuard will check rules.conf, recognize the id as a permitted device, and allow it to be used.
Immediately your device becomes available for regular use. This was a simple method of just allowing the device by its id. To get really specific you might add a rule to rules.conf along these lines:
allow 0781:5151 name "SanDisk Corp. Cruzer Micro Flash Drive" serial "0001234567" via-port "1-2"
reject via-port "1-2"
The above rules will allow only a device matching that id, name, serial only on a specific port. The reject rule will not allow any other device plugged in to that port. The options are pretty much endless, but can be referred to online.
Physical Prophylactics
USBGuard probably isn't going to protect you against the infamous USB Killer. So what can you do? If you do have control over your USB ports and still need to plug in some questionable USB drives some solutions are available. The price of a USB hub relative to a new laptop is microscopic. One of the huge advantages of using such a seasoned technology is that it's accessories are widely available and cheap. You could grab a good branded one and instead of plugging sketchy devices directly into your machine, plug it in via the USB hub. Should the USB drive be a USB Killer, it will fry the USB hub and your machine will be safe.
Another solution to your use case may be the USG. The device is a hardware firewall that sits between a suspect USB device and your machine. It is compatible with mice, keyboards and USB flash drives. It will protect you against BadUSB by filtering the malicious activity, and passing through the data you need.
Isn't This Overkill?
Depending on the environment you work in, this may be the case. If you can afford not to plug in any device that you don't have full control over and you are the only person with access to your machine, then this would be the best case. The silver lining is that in addition to the people trying to find ways of doing harm, there are people also thinking about ways to prevent that harm.
Have ever had any bad experiences with dodgy USB devices? How do you ensure you or your company have safe USB measures? Let us know in the comments below!
Image Credits: Frantisek Keclik/Shutterstock