Your mother was right. That new-fangled technology is no good.
I mean, let’s think about it. For all the joy and convenience computers, smartphones and the Internet have brought to our lives, they’ve also made them less private, and less secure. We’re now living in a digital panopticon, where everything can and will be observed. The Internet has given us amazing opportunities, but has also given others the ability to financially cripple us, and dismantle our personal lives, both remotely and anonymously.
Perhaps it’s time we looked to the past.
Typewriters, rotary phones, and even one-time pads. These are all really old technologies that can all be employed today to improve security. Here’s what you need to know.
The Mystery of One Time Pads
There used to be a radio station in Akrotiri; one of the last remaining British colonies, situated on the southern tip of the island of Cyprus.
This radio station didn’t broadcast news, or documentaries. It broadcast only one song - the Lincolnshire Poacher - and a string of automated, computerized numbers spoken by an automated, female voice. This relic of the cold war is both haunting and beautiful. Here’s what it sounds like:
Nobody really knows for definite who ran it, but it’s largely assumed it was owned by MI6. It’s called a Numbers Station. These were high-powered, shortwave radio stations that would broadcast a series of numbers or words. These would correspond to a record on what’s known as a ‘one time pad’. So, for example, 68 might correspond with “Moscow”, and 75 might correspond with “Airport”. You get the idea.
The Soviet Union had theirs. The Brits had more than a few. As did the Cubans, and the East Germans. The beauty of them was that they allowed the operator to communicate with their agents without the risk of interception, or identifying the agents in question.
Most of these have shut down. The only ones remaining right now are those operated by the Russian Federation, like UVB-76 - also known as “The Buzzer”.
But that hasn’t diminished the effectiveness of the technology. It simply relies on two parties having a dictionary of codewords, each with a corresponding meaning. One party will broadcast - or at least make publicly available - a list of codewords, and the other party will listen and decode the message by matching each codeword with its corresponding meaning.
The beauty of this system is that if the dictionary of codewords was compromised, you’d simply discard it and create a new one. It’s a great example of a low-tech, NSA-impervious encryption system.
You don’t need your own high-powered radio transmitter to take advantage of One Time Pads. You just need to create your own dictionaries. These can be made with simple pen and paper, and shared with FedEx or something similar.
To communicate messages, you can simply post it online. You could use Twitter, Reddit, Pastebin, or something similar. It’s just as impervious to interception.
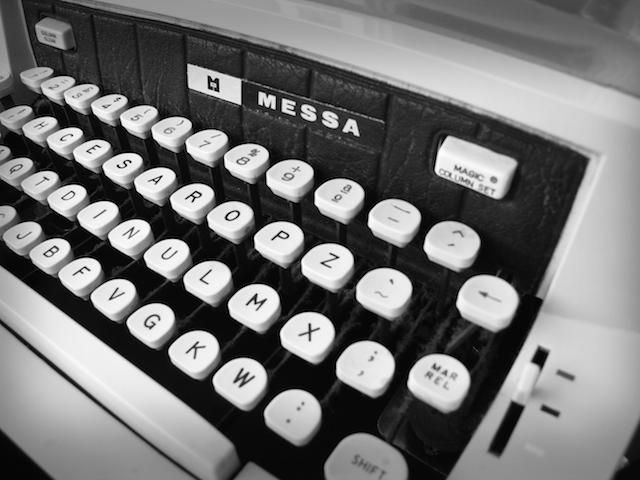
Typewriters - Not Just For Hipsters
Okay, confession time.
Until early last year, I owned a typewriter. It was an Olivetti, first bought some time in the early 1960s. Before it made its way to me it was owned by a chain smoker whose 40 a day addiction had stained the keys a luminous yellow. But I loved it.
It made an almighty noise when you struck each key, and there was something truly delightful about seeing your words materialize on the page in front of you.
But it wasn’t meant to be, and I eventually got rid of it. There were a few reasons. It was bulky and heavy, and finding ink ribbons was almost impossible. Plus, it was hard to get my work onto my computer without using an OCR program, or manually typing it up myself. I ended up donating it to the same charity shop I bought it from.
Hardly anybody uses typewriters any more, with one exception. Not long after Edward Snowden blew open the NSA’s dirty laundry, the Russian government bought about 486,540 roubles worth (about $7400’s) for the Federal Protective Service, or FSO.
For them, the advantage is obvious. It’s impossible to hack a typewriter. If you’re creating a single, paper copy of a document, it becomes much harder to leak it. If it does get leaked, there’s a chain of custody, and you can find the person responsible. Plus, there’s almost no maintenance involved. Secure systems need a lot of administration and management. Typewriters require none.
But you’re not a Russian spy. Or, at least, I don’t think you are.
There are still some pretty compelling advantages to buying a secondhand typewriter. You can work without worrying about keyloggers, or your text being held to ransom by Cryptolocker. And you’ll look cool as hell doing it.
Get A Rotary Phone
A friend of mine was born in the 60s. Until the late 80s, his home phone had a rotary dialer. I asked him what it was like, and he told me “I ended up hating anyone with more than one ‘0’ in their phone number”.
Rotary dial phones were annoying. They were inconvenient. It took ages to dial numbers, and they couldn’t be used with automated helplines, since they didn’t emit DTMF tones.
They’re pretty much all but dead now. They were killed by touch-tone telephones, which in turn have been killed by cell phones. But there are a few good reasons to hang on to your rotary phones if you’ve still got one. Especially if you’ve got an elderly relative you might feel is susceptible to phone scams.
There’s a particularly nefarious one right now that’s especially prevalent in Europe.
It's known as the courier scam.
A simplified version of the scam works a bit like this: a fraudster will phone pretending to be from the bank, and insist that there’s a problem with the victim’s bank or credit card. They’ll ask them to type their four-digit pin code into the phone in order to “verify” your details. This effectively gives them your pin code, as they’re able to transcribe each "beep" to a number.
They’ll then “confirm” there’s a problem with the card, and say they say they’ve sent a courier to pick it up. In reality, it’s an accomplice of the fraudster. With your card and your PIN code, they’re free to drain your bank account, and they will. Some have lost tens of thousands.
This could be averted by simply not owning a phone that produces DTMF tones. Namely, a retro rotary phone.
Other Tech Worth Mentioning
There are other great examples of old technology being repurposed with the aim of increasing personal security.
Recently, Sharp - a popular Japanese electronics manufacturer - released two new landline phones (one with an integrated fax machine - faxes are still used in Japan) with the goal of protecting the elderly from fraud. Whenever an unrecognized number dials the phone, an LED strip glows red, reminding them to be wary.
Both of these devices also allow the user to block numbers simply by pressing a button. Considering that most phone companies and manufacturers still don’t make it easy to block nuisance calls (although it's relatively easy with Android), this is incredibly welcome.
But above all, it reminds us that we don’t need the latest and greatest technology to be secure. Often, older and less sophisticated gear is good enough.
Do you use any old tech, simply because you feel it’s better for your security and privacy? I want to hear about it. Leave me a comment below, and we’ll chat.