<firstimage="https://www.makeuseof.com/wp-content/uploads/2011/08/featured-wallwatcher.png">
If you have access to your router, and it’s able to log activity, it’s relatively easy to watch everything that’s going on to try to find any untoward activity. Today I’d like to show you how to set that up on your DD-WRT router and some Windows-only software called WallWatcher (OSX users - you can still use this network traffic monitor software in a Parallels virtual machine just fine)
Requirements
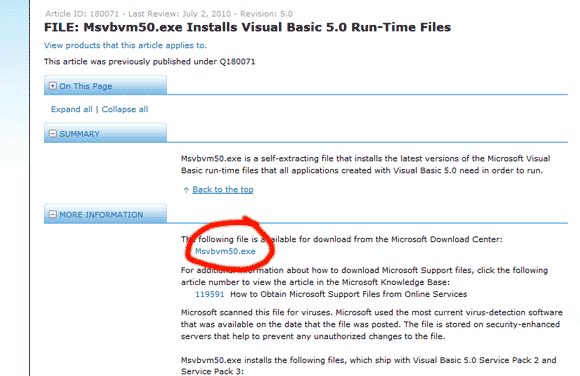
MSVBM50.exe available from Microsoft.
The WallWatcher library files.
The WallWatcher app.
A router with DD-WRT or similar that allows remote logging.
Installing & Configuring
Download and install the VB runtime files from Microsoft first. If you can’t find the download link, check out the following screenshot of the download page.
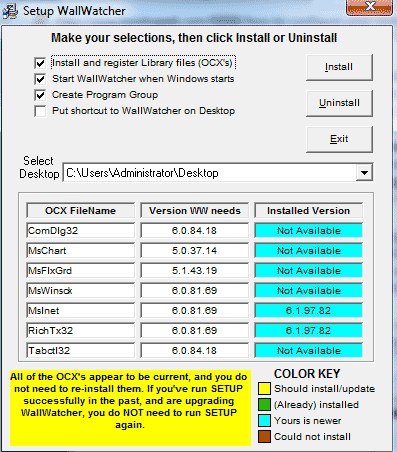
Next, create a new folder called WallWatcher and extract the contents of both of the zip files you downloaded into the root of that folder. Run setup.exe when you’re done. If the coloured boxes on the right at the bottom of the page are all blue, click install to continue. If some have errors, make sure you check the box that says install and register library files (OCX). Windows 7 users should have no issues though.
You now should now find an icon on your desktop.
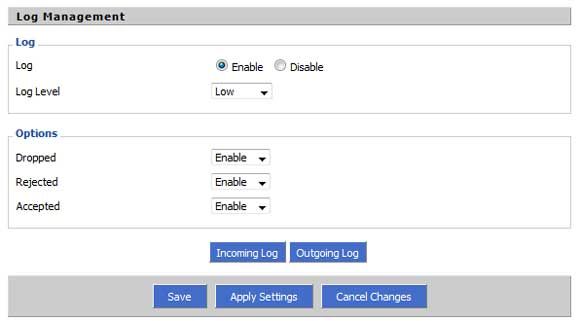
Next up, log in to your router to configure that side of things. On the security tab, find the section labelled Log Management, and enable it at a high level. Under the options section, enable each setting too. Save and apply the settings.
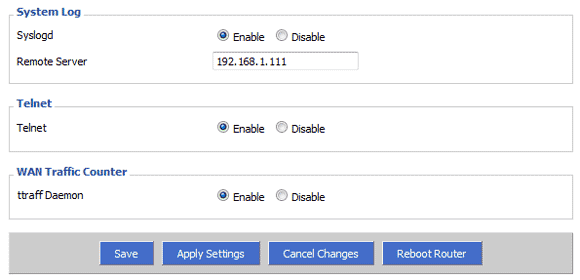
Then, under the Services menu, scroll down to System Log and click to Enable. In the box labelled Remote Server, enter the IP address of your Windows machine.
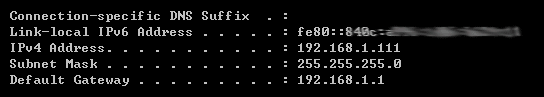
If you don’t know your IP address, the easiest way to find out is to open a command prompt, and type ipconfig. With default DD-WRT addressing, you should see 192.168.1.??? (not 1). Copy and paste that number, then hit Apply.
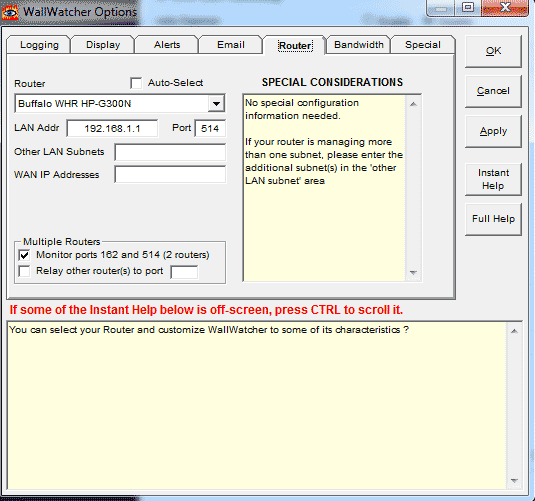
Back to WallWatcher. Open it up and check the box for auto-select. It should be able to figure out what your router is automatically. If you want to enter the details manually, IP Tables is the setting for a generic DD-WRT flashed router, and the LAN address will be your router (192.168.1.1 by default), with 514 as the port number.
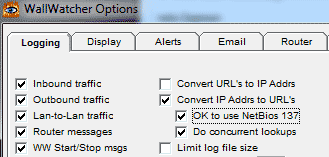
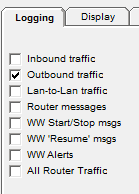
Next, click over to the Logging tab and ensure the Convert IP Addrs to URL’s is enabled, along with OK to use NetBios 137. This will ensure you can at least see some meaningful URLs in the log instead of the actual IP address of the website.
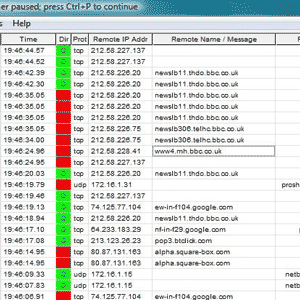
Click OK and you’ll be taken to the log. You should see a bunch of messages coming onscreen right now showing your entire traffic breakdown on the network. Since it can be a bit overwhelming, I found it better to go back to the Options->Logging screen and disabling everything except outbound traffic.
I had problems fully identifying URLs from the IP because I’m running DD-WRT as a sub-router in my network. If you’re having issues too, make sure that port 137 is open and forwarding correctly on your main router, as this is used to look up the URLs.
Conclusion
Using this method to watch everything going on on your network is guaranteed to make you quite paranoid. The fact that so many packets go whizzing in and out from all over the place might seem alarming, but the truth is that by loading just one website you are likely making many requests to many different IPs in order to pull in external resources such as images, javascripts, and advertising banners. It's a good way to see if someone else is on the network as it shows originating IP too.
But now what? Do you want to get your own back and figure out who they actually are? Stay tuned - in a few weeks time I'll be looking at some downright dirty tools that can show you exactly what they're looking at, and even grab some website logins they might be using. We also covered great portable network analysis tools last year.