A Virtual Private Network is a really useful tool for protecting your privacy and staying anonymous online. VPNs work by passing your Internet connection through another computer (called an "endpoint), using an encrypted tunnel. This means that anyone situated between your computer and the endpoint is unable to see what you're doing. It also means that you're disguised as the endpoint to any computers your machine connects to. Put simply, it hides your IP address.
But a vulnerability in many VPN providers recent discovered by Perfect Privacy puts that last point in doubt. This security flaw could potentially see people lose their anonymity whilst using VPNs. Here's how.
The Vulnerability
So, how does the attack (which has been dubbed "Port Fail") work? Well, first, a few conditions need to be met.
Firstly, the VPN provider and the attacker have to have port-forwarding enabled. This is where the IP address and port number changes while the packet is traversing the network. For some background reading on this, check out our piece on Network Address Translation (NAT). The attack still works if the victim doesn't have port forwarding enabled.
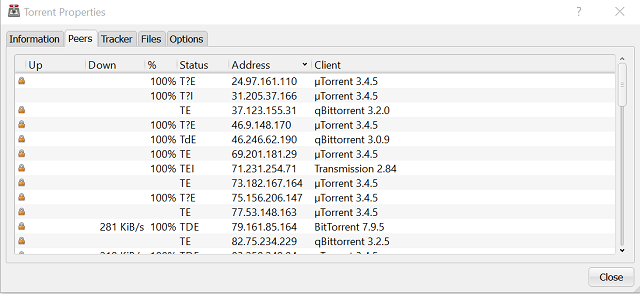
The attacker has to also have an account with the VPN they're targeting, and know the IP address of the VPN endpoint the user is using. This can be found by watching a BitTorrent swarm (all the peers connected to a single torrent), or by monitoring an IRC.
Then, the attacker connects to the same VPN endpoint as the victim, and waits for them to visit a malicious webpage that's under the control of the attacker. This can often be accomplished by embedding the webpage in a legitimate site, either as an image hosted on the webserver or as an iFrame. From this, it becomes possible to deduce the real IP address of the person being targeted.
Who Was Affected
Some of the biggest names in VPNs were affected by this vulnerability. This included Ovpn.to, nVPN, and Private Internet Access (PIA). All of whom were informed about the vulnerability before it was disclosed, and were able to issue a fix before it became public knowledge. Speaking to TorrentFreak, Private Internet Access said:
"We implemented firewall rules at the VPN server level to block access to forwarded ports from clients’ real IP addresses. The fix was deployed on all our servers within 12 hours of the initial report".
PIA also gave Perfect Privacy a $5,000 bug bounty in recognition of their efforts, and the fact they disclosed the vulnerability in a responsible manner. In the past, we've written extensively about the ethics of vulnerability disclosure, and how it's almost always better to inform the vendor before releasing the vulnerability to the wild.
Of course, there are thousands of VPN providers. Whilst some have issued fixes, it's likely many more have not.
Why This Matters
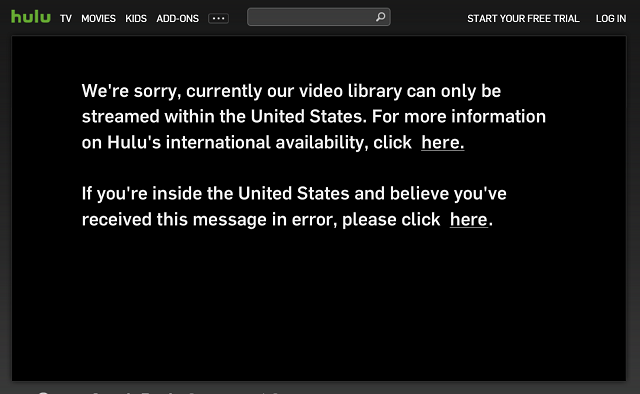
People use VPNs for a variety of reasons. Many people use them to defeat georestrictions on Internet TV sites. Some use them to secure their communications while using a public Wi-Fi hotspot. Others use them to defeat government censorship and surveillance, or to download movies and music illegally without getting sued.
For those in the latter category, the discovery of this vulnerability will be of real concern. As always, your only real option is to vote with your wallet, and subscribe to a VPN provider that's been confirmed to have patched this vulnerability.
Personally speaking, I'm a huge fan of Private Internet Access, and would recommend them any day of the week. For a more detailed look at the market, check out our list of the best VPN services. There are also some free VPN services, too.
Stay Secure
When using a VPN, there's few things you can do to improve your privacy. Firstly, you can configure your computer to protect against DNS leaks, which can utterly undermine your anonymity. Furthermore, consider turning off JavaScript (what is JavaScript?) in order to defend against Canvas Fingerprinting attacks. It's worth pointing out that this can have an adverse effect on your browsing experience, and many (including James Bruce; our Chief Web Officer) advise against of it.
Have you got any other strategies for improving your privacy when using a VPN? Tell me about them in the comments below.
Image Credit: Server racks by Oleksiy Mark via Shutterstock