You may have heard the phrase "your health is your wealth." It's one of the reasons the US spent over $3.2 trillion on healthcare in 2015 alone.
With so much money floating around, it's only natural that a lot of businesses have entered the healthcare market---including technology companies.
Medical technology sometimes feels dated, but companies are intent on dragging those devices into the 21st century. And while internet connectivity might seem like a great feature to have, there are some real dangers and issues that could surprise you.
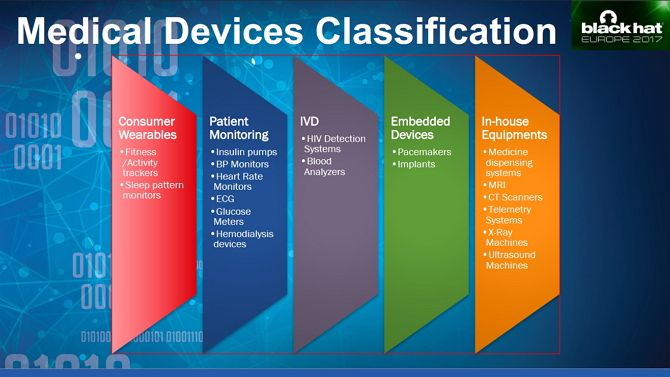
What Are Medical Devices?
The World Health Organization (WHO) defines a medical device as "any instrument, apparatus, implement, machine, appliance, implant, reagent for in vitro use, software, material [...] intended by the manufacturer to be used [...] for human beings, for one or more [...] specific medical purpose".
Although that sounds quite complicated, it just means any device or software that may be used for medical purposes.
The US Food & Drug Administration (FDA) is responsible for regulatory oversight of medical devices and splits them into three categories: Class I, Class II, and Class III. Class 1 devices are lightly regulated, with most controls only placed on how they are manufactured and marketed. Class II adds more specific regulation, and Class III is reserved for devices which support or sustain human life.
However, as is typical around the world, the FDA has struggled to keep up with the pace of innovation. There are few references to how modern, internet-connected devices should be regulated.
What steps should manufacturers be putting in place to ensure the security of such devices? In December 2016, the FDA did release guidance on medical device security, but they aren't legally enforceable. This left manufacturers to decide whether to follow the advice or not.
The Internet of (Medical) Things
This puts internet-connected medical devices in the same boat as those in the broader Internet of Things (IoT) category. There are many benefits to IoT medical devices, but the lack of enforceable regulation means that manufacturers aren't likely to put many resources into securing them.
That's just one of the many reasons why the Internet of Things is a security nightmare. Additionally, we literally place our lives in the hands of medical IoT devices. As such, the stakes are even higher than with regular IoT devices.
Healthcare is an expensive business, not just for patients, but for the providers themselves. Companies charge vast sums of money for new devices and technical support. This means hospitals and other medical practices are a jumble of tools---some new, some old with a range of different operating requirements. Old hardware, legacy software, and proprietary interfaces all come together to make appropriately securing the system a nightmare for the provider's IT department.
Example: Eavesdropping on a Medical Pump
The interface between software and hardware often exposes exploitable vulnerabilities, as Saurabh Harit showed at Black Hat Europe 2017. He obtained an IV infusion pump, which injects medications into a patient's blood, which could be programmed and operated remotely.
After accessing the pump's admin mode with a default password found online, he was able to use the unit's infrared and an old PDA purchased from eBay to import their Wi-Fi credentials to the pump's network settings.
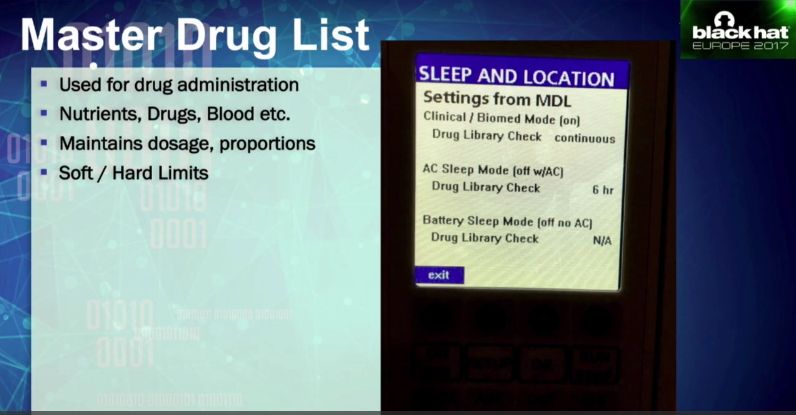
Using Wireshark (one of many open source network security tools) to inspect the packets, Harit viewed patient data like medication dose, caregiver, name, location, and route. Amazingly he was even able to access the Master Drugs List which sets and maintains the prescribed dosage.
The List of Examples Goes On...
If such vulnerabilities were limited to this one pump, it would be shocking enough, but researchers regularly uncover new ones. One team was able to gain access to a CT scanner, a device which gives you a small dose of radiation to create 3D models of inside your body.
In August 2017, the FDA recalled 465,000 pacemakers made by Abbott over hacking concerns. Instead of forcing almost half a million people to undergo invasive surgery, Abbott issued a firmware patch, which medical staff were able to apply to the pacemaker.
Back in 2014, the Department for Homeland Security (DHS) began investigating 24 devices over suspected critical flaws. Devices included an infusion pump from Hospira Inc and implantable heart devices from Medtronic and St Jude Medical.
Legacy Medical Devices and Poor Security
If you've ever worked in an office, you'll know that many businesses rely on legacy software. This invariably requires older operating systems, drivers, and peripherals, making them very insecure. Cost is usually a deciding factor in whether to update, and many decide they can't justify the expense. If it ain't broke, don't fix it, right?
Businesses often struggle to prioritize cybersecurity, with a prevailing attitude that if an attack hasn't happened yet, then it won't. Unfortunately, healthcare providers aren't immune to this line of thinking either. In May 2017 a ransomware attack, dubbed WannaCry, almost simultaneously infected 300,000 computers, many belonging to the UK's National Health Service (NHS).
The ransomware affected over 40 NHS Trusts around the country, reducing patient care, closing surgeries, and even close hospitals. The effects of the attack put patients at risk and potentially undermined the security of their data too. Sadly, Microsoft released a patch one month before the attack, which would have prevented WannaCry from taking hold. Not only was the update not rolled out, but as it turned out many computers were still running Windows XP.
This is despite extended support for the 15-year-old operating system having ended two years before the attack.
The Future of Medical Devices Freaks Me Out
Technology continues to deliver significant advancements in medical treatment, but it isn't the medical sector's saving grace as the UK's NHS discovered. According to the Government's Health Secretary, Jeremy Hunt, up to 270 women may have died after a "computer algorithm error" failed to invite 450,000 women to regular breast cancer screening.
Unlike many other areas affected by the advancement of technology, medical devices can be a matter of life or death. As Moore's law enables more devices to come online in the coming years, manufacturers must prioritize security. After all, it's no good designing a "killer feature" if that turns out to be a devastatingly accurate description.