Windows Defender is the antivirus included with Windows 10, and it's actually worth using now. Thanks to a lack of nag screens and integration into the operating system, it offers fine protection with no extra configuration needed.
The antivirus is always getting better, and Microsoft introduced new enhanced functions for Windows Defender in the Creators Update. If you want to beef up the protection it offers, follow these steps to enable enhanced blocking.
In Windows 10 Pro, you can use the Group Policy editor to enable the tweaks. Type gpedit.msc into the Start Menu to open the editor, then browse to the following location (MAPS stands for Microsoft Active Protection Service and is the network Microsoft uses to help identify threats):
Computer Configuration > Administrative Templates > Windows Components > Windows Defender Antivirus > MAPS
Once here, double-click on the Join Microsoft MAPS entry and switch it to Enabled. In the bottom-left box, switch it to Basic Maps or Advanced MAPS -- they perform the same function as Basic MAPS isn't supported anymore. Then click OK. This will send information to Microsoft about detected software, and is required for the advanced options to work.
Still inside the MAPS folder, you may want to configure the other three settings. Enabling Configure the "Block at First Sight" feature will perform real-time checks with Microsoft protective services on potentially infected content. You can choose how to send file samples (never send, always prompt, send safe samples automatically, send all samples automatically) with the Send file samples when further analysis is required entry. You must choose one of the latter two options if you have Block at First Sight enabled.
With MAPS enabled, switch to the MpEngine folder on the left sidebar. Click the Select cloud protection level entry and set it to Enabled, then in the bottom-left options box choose High blocking level. Microsoft notes that this makes "Windows Defender . . . more aggressive when identifying suspicious files to block and scan." Thus, you might see more false positives pop up when using it.
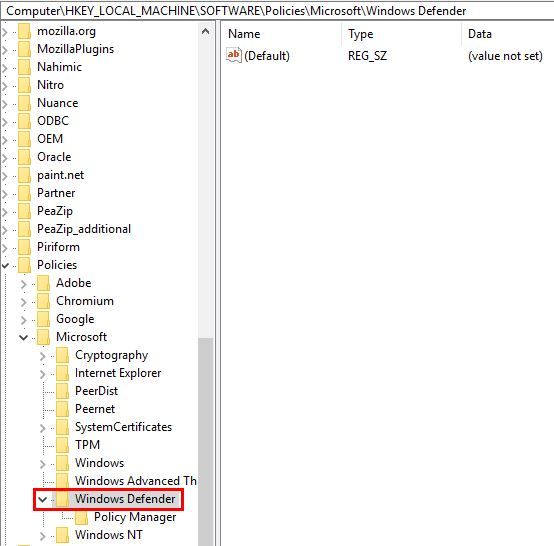
If you're using Windows 10 Home, you can either use a workaround to access the Group Policy editor or do it via the Registry. For the latter, type regedit into the Start Menu to access the editor. Head to this location:
HKEY_LOCAL_MACHINE\Software\Policies\Microsoft\Windows Defender
Right-click on Windows Defender, then choose New > Key and name it Spynet (another name for MAPS). Then right-click on Spynet, and choose New > DWORD (32-bit) Value. Name this one SpynetReporting, and double-click it to open its properties and set it to 2.
Again, right-click on the Windows Defender entry and use New > Key to name another key MpEngine. Right-click MpEngine and create a New > DWORD (32-bit) Value with the name MpCloudBlockLevel. Double-click this and set its value to 2 as well.
Making these changes in the Group Policy editor does the Registry tweaks for you, making it a bit simpler. But either way, this will make Windows Defender more resistant to threats. For more, check out our overview on Windows Defender, including how to tweak its other settings.
Do you use Windows Defender or another antivirus in Windows 10? Will you use these settings to make it more aggressive? Let us know if you found this useful in the comments!
Image Credit: Sasun Bughdaryan via Shutterstock