We've made it through another year in security... and what a year it has been. From global ransomware attacks to leaks containing billions of records, it has had it all. Cybersecurity is a constant news feature. Not a month goes by without a major leak, attack, or similar.
Did you notice everything that went on? It is difficult to keep up -- even for me, and I watch and read security news every day. With that in mind, I've collated and reviewed the year in cybersecurity so you can sit back and marvel at everything that went spectacularly wrong.
The Big Events
Security in 2017 was punctuated by a series of savage, extremely memorable events. Many of the events were so large they affected almost everyone on the planet. Some took down major institutions while others concerned truly astonishing data leaks from previously trusted institutions. Let's check out the major events that shaped the year.
The Shadow Brokers
In April 2016, a shadowy (get it?!) group known as the Shadow Brokers announced that they had breached a server belonging to an elite NSA-linked operation known as the Equation Group. At the time, The Shadow Brokers offered a small sample of supposed NSA hacking tools and data. Halloween and Black Friday 2016 saw The Shadow Brokers attempt to auction their ill-gotten gains, without much success.
They were looking for 750 BTC -- worth around $750,000 in January 2017 but over $9,000,000 at an all-time high in December 2017. Instead, they received around $18,000 worth of Bitcoin and released the entire dump of NSA hacking tools, online for free. The identity of The Shadow Brokers remains unknown. There is, however, wide speculation that it was an elite Russian government hack group looking to one-up their counterparts and illustrate that attributing nation-state hacks is a dangerous business.
What happened next? Read on, friend.
WannaCry
In amongst The Shadow Brokers hack tool trove was an exploit known as ETERNALBLUE (also stylized EternalBlue). EternalBlue exploits a known (now patched) vulnerability in the Microsoft Server Message Block (SMB) protocol, allowing attackers to insert specially crafted packets to execute malicious code on a target machine.
The NSA warned Microsoft that hackers had compromised the EternalBlue exploit. Microsoft responded by canceling February 2017 security updates, patching the exploit, and rolling it all out in March 2017. Roll forward to May 2017 and the WannaCry ransomware attack hits, exploiting -- you guessed it -- EternalBlue and the SMB protocol vulnerability.
WannaCry ripped through a reported 250,000 computers within the first 24-hours, encrypting machine after machine, demanding payment in Bitcoin for the private encryption key required to unlock each device. The U.K.'s NHS was hit badly, forcing some areas to run on emergency-only services. Telefonica, FedEx, Deutsche Bank, Nissan, Renault, the Russian rail service, Chinese universities, and more were directly affected by WannaCry.
Marcus Hutchins, aka MalwareTech, curtailed the global ransomware epidemic by registering a domain name found in the ransomware source code. The domain name acted link a sinkhole for new infections. Rather than encrypting the device, the ransomware lay dormant. Later in the same month, the huge Mirai botnet attempted to DDoS the WannaCry kill-switch domain site to bring the ransomware back to life (but ultimately failed). Others launched WannaCry variants designed to exploit the same vulnerability.
Microsoft directly accused the NSA of causing the incident by stockpiling critical exploits for a number of operating systems and other critical software.
Voter Records
Data breaches have become dime-a-dozen. They're everywhere, affecting everything, and mean you have to change your passwords. But in June 2017, security researcher Chris Vickery uncovered a publicly accessible database containing voter registration details for 198 million U.S. voters. This equates to almost every voter going back some ten years or more.
The data, collected and aggregated by conservative data firm Deep Root Analytics, was hosted on a misconfigured Amazon S3 server. Luckily for Deep Root Analytics, the majority of the data was publicly accessible, meaning it containing names, address, party affiliations, and so on. But a hacker could certainly find a use for that quantity of pre-aggregated personal information.
Vickery said, "It's definitely the biggest find I've ever had. We're starting to head in the right direction with securing this stuff, but it's going to get worse before it gets better. This is not rock bottom." Worrying times, indeed.
Equifax
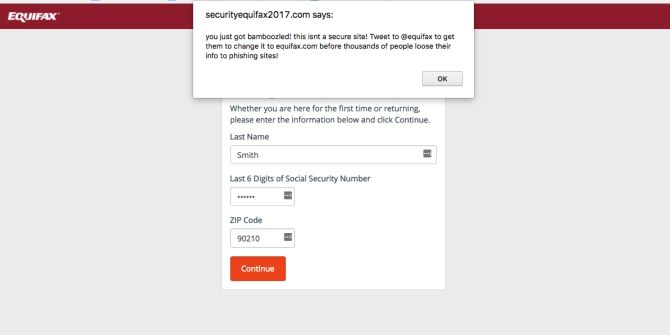
Rollup, rollup, the next enormous breach is here. The staggering Equifax data breach caught the attention of almost every American citizen. Why? Because the credit reporting agency suffered a major breach, failed to disclose the information, let board members sell stock before announcing the breach, and exposed the detailed credit history of almost every American citizen to whoever gets their hands on the data.
Sounds bad, right? It was and is bad. Not content with exposing the credit history of hundreds of millions of citizens, Equifax repeatedly fumbled the cleanup operation. So, what happened?
In December 2016, a security researcher told Motherboard, under anonymity, that they had stumbled upon an online portal meant for Equifax employees only. The researcher exploited a "forced browsing" bug and immediately gained access to the records of millions of U.S. citizens. The researcher informed Equifax of the vulnerability as a responsible disclosure. Keep this breach in mind.
In September 2017, reports emerged that Equifax was victim to a major cybersecurity breach -- but the breach had taken place in March 2017. The breach appeared to come from the same vulnerability as previously detailed to the credit agency. At the same time (still in September), Equifax announced data theft impacting 145 million U.S. consumers, as well as between 400,000 to 44 million U.K. residents and 8,000 Canadians.
The hackers recovered personal information including full names, birth dates, addresses, Social Security numbers, and several other vital information types, such as driver licenses. Simply put, it is one of the worst data leaks ever seen.
It Got Worse
But it gets worse. In the days following the announcement, the Equifax account recovery and assistance site was marked as spam by OpenDNS and taken offline, presumed to be a phishing site. Oh, and to check their account status, users were required to enter the last six digits of their Social Security numbers -- the irony wasn't lost. Then the site started returning false information. Numerous reports of users entering completely false information returned positive results, informing the user that their data was lost. And then a phishing site popped up, further clouding the already murky waters.
Adding insult to injury, Congressman Barry Loudermilk introduced a bill to the U.S. House of Representatives that essentially stripped consumer protections directly in relation to business conducted by U.S. credit agencies. The bill also attempted to quash all punitive damages. Loudermilk previously received $2,000 during the 2016 election cycle from Equifax.
No hacking group has come forward with data as yet. When they do, however, you can be sure the data will carry a hefty price tag.
Vault 7
It wouldn't be a year in cybersecurity without an entry from WikiLeaks. In March 2017, WikiLeaks released a trove of CIA documents consisting of 7,818 web pages, with a further 943 attachments. When pressed on their authenticity, Former Director of the CIA Michael Hayden stated that the CIA does "not comment on the authenticity or content or purported intelligence documents."
Other officials, both current and former, confirmed the authenticity of the documents. Other likened the CIA Vault 7 leak to the NSAs leaked hacking tools via The Shadow Brokers. What did Vault 7 contain?
The documents are essentially a highly detailed catalog of powerful hacking tools and exploits. In amongst the trove are instructions on compromising Skype, Wi-Fi networks, PDF documents, commercial antivirus programs, password theft, and much more.
Cybersecurity firm Symantec analyzed the tools and found several descriptions matching tools "used in cyberattacks against at least 40 different targets in 16 different countries" by a group known as Longhorn. The Symantec analysis of development timelines for certain tools and their use against specific targets further corroborated the authenticity of the Vault 7 contents -- and their direct link to the CIA.
Data Breaches
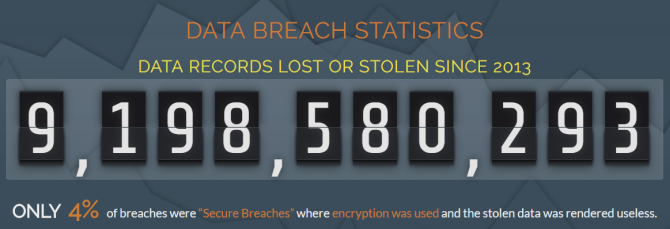
Those five events were probably the biggest, most shocking revelations of the year. But they weren't the only major events. There were several data breaches involving mind-boggling numbers; the River City Media dump alone contained 1.4 billion email accounts, IP addresses, full names, and more (and that is without considering that RCM themselves are a shadowy group of spam purveyors).
The figure below is simply staggering, but represents a 56 percent in recorded lost or stolen records since I wrote the last end of year report.
Or how about the U.K.'s NHS? The creaking National Health Service suffered its worst data breach event in March 2017. An accidental disclosure exposed the private medical data of 26 million records, accounting for 2,600 health practices around the country. Or the so-called Big Asian Leak, a hacker's database containing more than 1 billion records pilfered from several major Chinese technology companies? That one barely even made the news outside of Asia and cybersecurity circles.
If you'd like to understand more about the heft numbers behind each breach, I suggest browsing through Breach Level Index. Alternatively, this Identity Force list is also comprehensive.
Malware and Ransomware
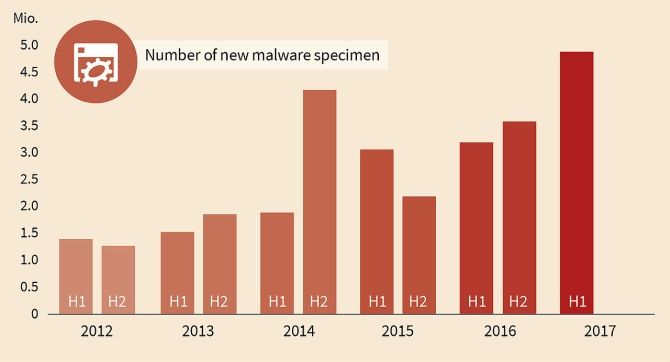
The cold hard numerical facts are as follows: malware and ransomware attacks are consistently rising. Globally, there are more malware and ransomware variants, too. The G-DATA Security Blog estimates that there are more than 27,000 new malware specimens every day -- that's every 3.2 seconds. Their half-year study found that one in every five malware specimens were created in 2017. (Read our guide on how to remove the majority of them!)
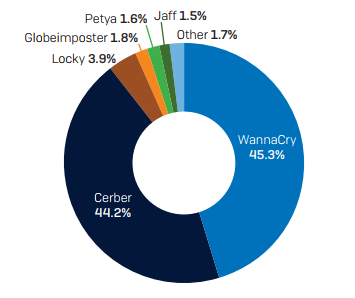
This year, the WannaCry ransom-worm detailed earlier has entirely skewed the infection landscape. A recent Sophos report [PDF] elaborated that while "Cerber has been the most prolific ransomware family . . . its power was overshadowed for a few months . . . when WannaCry stormed the planet on the back of a worm." Other attack vectors, like malvertising, phishing, and spam with malicious attachments, have also seen considerable rises.
Other extremely virulent strains, such as Petya/NotPetya/GoldenEye upped the ransomware attack level by encrypting the Master Boot Record, forcing a reboot to enable the encryption process, running a fake CHKDSK Command Prompt to disguise the process, and demanding a substantial ransom to decrypt the system.
Cryptojacking
For instance, a common malvertising tactic (known as cryptojacking) is redirecting the user to a site running a cryptocurrency miner in the background. In some cases, even after closing the offending tab, the cryptocurrency mining script carries on running. Other instances simply lock a web page down and issue a ransom to unsuspecting users, or force-download malicious exploit kits to the device.
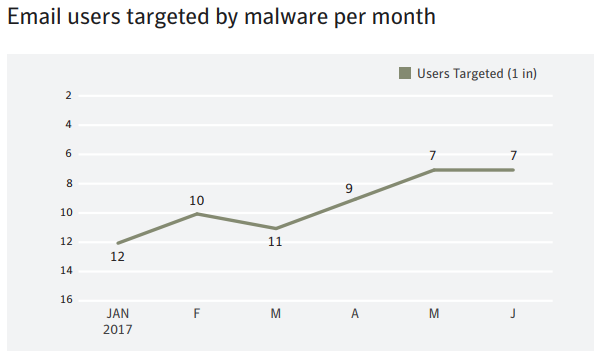
In Q3 2017, Kaspersky Lab found that 59.56 percent of global email traffic was spam -- up 1.05 percent from the previous quarter. Of that spam, Symantec estimated one in every 359 carries a malicious attachment, while email, in general, remains the #1 delivery mechanism for malware.
"No other distribution channel comes close: not compromised websites containing exploit kits, not network file sharing technologies like SMB, not malicious advertising campaigns that entice users to click on banner ads. In fact, a user is almost twice as likely to encounter malware through email than come across a malicious website."
Privacy and Surveillance
Not only has the amount of malware, ransomware, spam and similar increased, but our general privacy is decreasing at a time of increasing surveillance. At the turn of the year, we were still coming to terms with the colossal Yahoo! data breach. I've not included it in this yearly review because the majority of information arrived in December 2016 -- after I wrote last year's review, but importantly, before 2017.
The long and the short of it is this: Yahoo! suffered multiple data breaches throughout 2016 resulting in the leak of billions of individual records. It was so bad it almost destroyed the enormous Yahoo/Verizon merger. However, the following stats are post-Yahoo, but pre-Equifax and Voter Registration leak, so bear that in mind.
In January 2017, Pew Research reported that "a majority of Americans (64 percent) have personally experienced a major data breach and relatively large shares of the public lack trust in key institutions -- especially the federal government and social media sites -- to protect their personal information." Given the Equifax leak exposed 145 million citizens, and the Voter Registration leak exposed 198 million records, I'm willing to bet that percentage has significantly increased.
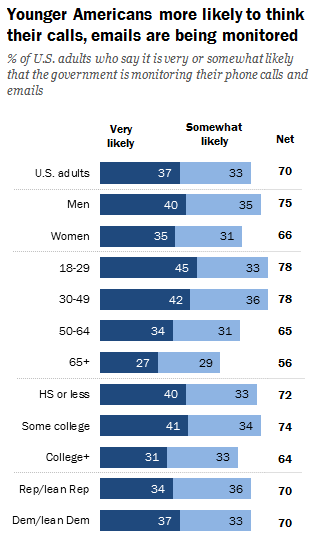
Regarding surveillance, just 13 percent of the U.S. public say it is "not at all likely" that the government is monitoring their communications. This, after the significant reduction in NSA metadata capture-reach, is telling. Nearly 80 percent of U.S. adults under the age of 50 believe their communications are tracked. However, in the over-50 bracket, this figure drops to around 60 percent.
Phishing
Here it is, the good news you await. The overall number of phishing sites has dropped from a high of over 450,000 in Q2 2016 to around 145,000 in Q2 2017. Celebration time!
Not so fast! The overall number of phishing sites has significantly decreased, but the variety of phishing methods has increased. Instead of simply using baited emails, malefactors are spreading their malicious arms throughout instant messengers and other communication platforms.
Fake airline tickets, supermarket voucher scams, free coffees, furniture, cinema tickets, and more have featured on WhatsApp, SnapChat, and other instant messengers.
Looking Forward to 2018
At this point, you're probably thinking "Please, just let it end." Well, you're in luck! You've reached the end of this thorough-but-entirely-bleak 2017 cybersecurity review. To summarize: as threats increase, their damage is worse, costs more, and have wider implications.
Staying safe online isn't entirely easy. But it doesn't have to be a chore, either. There is a single interlinking factor between every attack. Guessed it? That's right: it is the human factor. Education toward basic cybersecurity skills mitigates a phenomenal amount of potential problems.
Privacy and security is a notion slowly drifting away as we move into 2018. Technology is creating unfathomable convenience, but the cost is difficult to recoup once lost. Citizens are increasingly looking for new solutions to protecting their privacy. Or, at the very least, managing the data they relinquish. Data leveraging solutions are gaining traction, aiming to return power to users as the data creators. Several blockchain startups will make bold attempts throughout 2018 and onward to achieve this goal. (As well as those set to alter our relationship with credit agencies, too.)
Education, Education, Education
But in reality, we have to accept that privacy as we once knew it is long gone. Every internet user sits atop a mountain of aggregated data. The internet (and with it, big data) developed faster than other world-changing technologies. Unfortunately, users get caught in the mire.
As encryption guru Bruce Schneier says, "People don't test their food for pathogens or their airlines for safety. The government does it. But the government has failed in protecting consumers from internet companies and social media giants. But this will come around. The only effective way to control big corporations is through big government."
It isn't too late to educate yourself and those around you. It will almost certainly make a difference. And you don't have to spend thousands of dollars to be secure, but it might save you that further down the line. A great place to start is with our guide to improving your online security.
Were you hit by a security breach in 2017? Tell us in the comments.