Last week a Chinese team called Pangu released an untethered jailbreak for iOS 7.1.1, much to the dismay of seasoned jailbreakers like Stefan Esser (@i0n1c) whose past work was used in the exploit.
Regardless of how jilted developers feel, a jailbreak is a jailbreak from an end user's point of view – and an untethered one is about as good as it gets. That means the exploit remains active even once you have restarted your device
The tool was initially only available in Chinese for the Windows platform, but now a full translation and Mac OS X version has been added. What's more, the jailbreak works with the freshly released iOS 7.1.2.
The Pangu Jailbreak
Since the iPhone has been gaining in popularity in China, Chinese hackers have been on the jailbreak scene, releasing their own exploits that allow users to install alternative app and tweak store Cydia and generally change the way their iOS devices work. This time round there's some drama surrounding the group's use of Esser's code, which the group reportedly attempted to purchase on a number of occasions prior to the release.
"Stolen" exploits aside, another concern held by many is Pangu's inclusion of an alternative Chinese app store installed along with the initial release. Luckily if you're now downloading the English version of the jailbreak, the option to install the 25pp app store is disabled by default.
Jailbreaking became big money for companies once the notion of bundling access to other app stores was exploited. Many are speculating that the jailbreaking scene's latest trends focus on cash rewards for release groups, rather than putting together releases for the benefit of the tweaking community. That said, a number of prominent members of the jailbreak scene have confirmed the exploit's validity.
Some have suggested that this specific Pangu release "wastes" a number of bugs that the jailbreaking scene could have better used to crack iOS 8 once it arrives in a few months. Regardless of the various reasons behind the release, Pangu has used the exploits in their possession to release a public, untethered jailbreak – which is good news for those of you who enjoy tweaking.
It's probably also worth noting that Stefan Esser sold training to Pangu members who ended up using "his" vulnerability, which formed only a part of the larger initial release. The notion that an exploit could be "owned" or reserved for the user who initially discovered it is especially ironic, particularly given that the exploit's end goal is increased freedom over what Apple's hardware can be used for.
Jailbreaking Your Device
The jailbreak itself is a fairly simple process, though you will want to take a few precautions beforehand to minimise the chances of anything going wrong.
Note: Things can and do go wrong jailbreaking, and we can't be held responsible for anything going wrong with your device as a result of this. This is your device, and your choice – proceed with caution, and ideally use a spare out-of-warranty device rather than your brand new iPad Air or iPhone 5S. Jailbreaking will void your warranty.
You Will Need
- An iOS device (iPhone, iPad or iPod Touch) running iOS 7.1, 7.1.1 or 7.1.2.
- The latest version of iTunes.
- The Pangu jailbreak software.
- Your device connected via USB connection to your Mac or PC.
- Auto-lock disabled (Settings > General > Auto-Lock) and the passcode switched off (Settings > Passcode).
Jailbreak Procedure
1. Disable Wi-Fi on any other (paired) iOS devices that you don't want to jailbreak, as the latest version of the jailbreak app can detect other devices on the same network.
2. Connect your iOS device via USB and create a backup using iTunes. At this point it's a good idea to select your device in iTunes and disable "Sync with this phone over Wi-Fi" as it can cause problems later on.
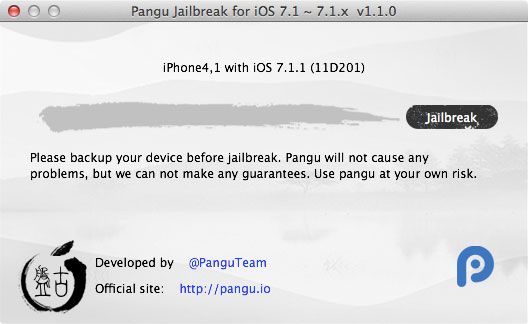
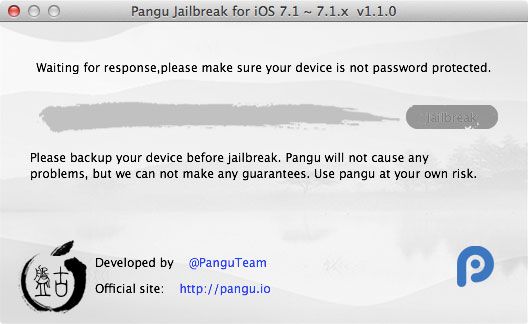
3. Download and launch the Pangu jailbreak app for Mac OS X or Windows, give it a second to detect your device.
4. Click Jailbreak and the procedure will begin, make sure you leave your device connected until the end.
5. When prompted, change the date of your device to June 2 (Settings > General > Date & Time). You might need to uncheck Set Automatically before you can change anything.
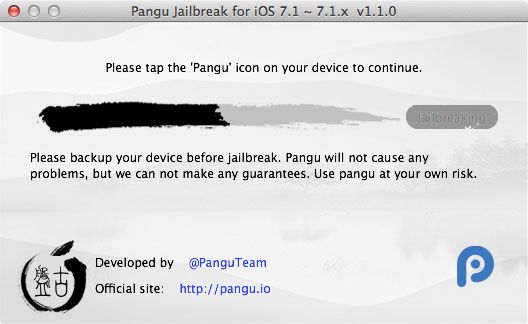
6. Wait for the jailbreak to continue after setting the date. Once prompted, tap the Pangu icon that has now appeared on your device.
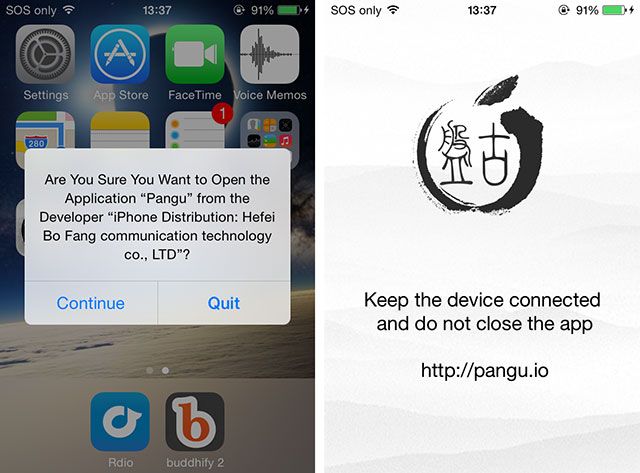
7. Tap Continue when the "Are you sure you want to open application ‘Pangu’ from the developer ‘ iPhone Distribution: Hefei Bo Fang communication technology co., LTD’" message appears.
8. The device will display a white screen with the Pangu logo. Heed the warning and keep both your device connected and the app open on your device until it reboots.
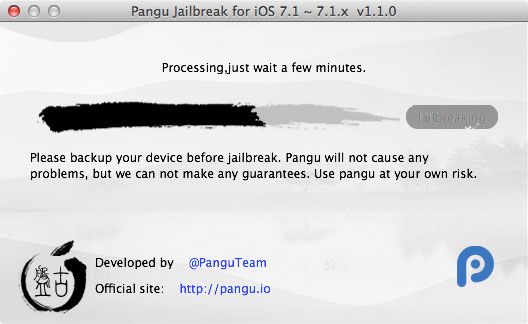
9. Be patient and let the jailbreak complete. Your device will reboot again, and once you see "Done!" on the Mac or Windows app you used, the process is complete.
Note: If you get the "Jailbreak timeout" error after restarting, ensure Wi-Fi syncing is disabled under iTunes. You can also kill iTunes altogether once you have made your backup. This setting caused my jailbreak to consistently fail until I changed it.
What Now?
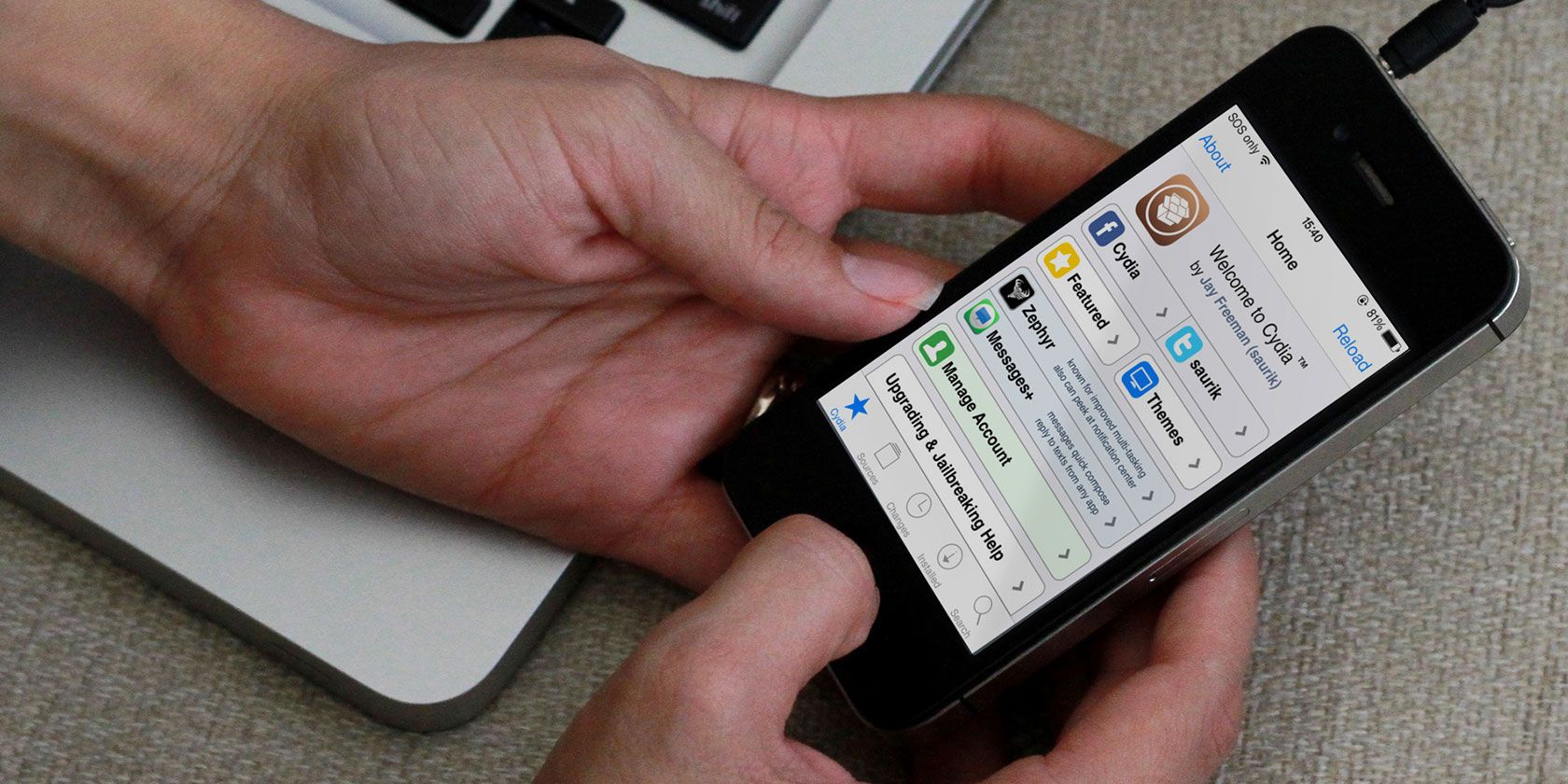
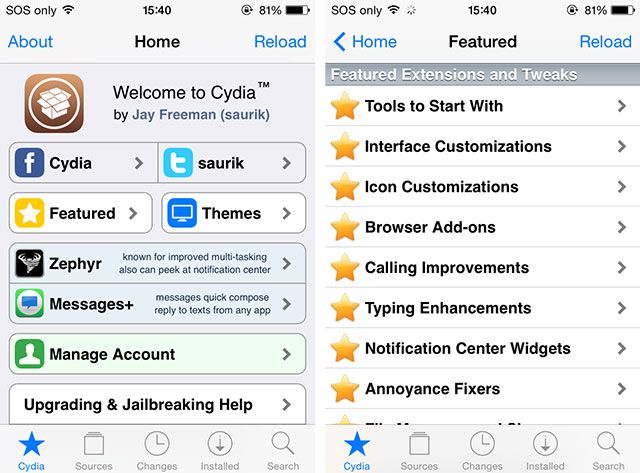
Once your iPhone has restarted for the last time and Pangu says everything has finished, scroll to your right-most home screen where you should find the Cydia icon. This is precisely why you wanted to jailbreak in the first place – Cydia is the app store for tweaks, both free and paid.
Unfortunately not everything in the Cydia store works with the current iOS release, though the majority of tweaks appear operational. In a post about compatible Cydia tweaks, RedmondPie posted a spreadsheet that contains a comprehensive list of current tweaks and their compatibility with the iOS 7.1.x jailbreak – so you should check there before spending any money. Remember that more tweaks will become available as they are updated.
One very important thing to remember is that once your device has received the jailbreak treatment, it's wide-open to attack from a variety of sources. You should be extra vigilant about installing tweaks from unknown repositories and wise-up to the threat of iPhone spy software too.
You've just removed the stabilisers, so anything can go wrong from here on. You've also just unlocked the true potential of your iOS device. Watch out for more jailbreaking tips and coverage on MakeUseOf over the coming months.
Image credit: PlaceIt