GRUB or the GRand Unified Bootloader is the bootloader commonly installed by Linux distributions on your hard disk. GRUB is responsible for showing you the menu that allows you to choose the operating system you want to boot into and also lets you tweak and control the booting options.
Awesome powers in good hands but as you probably know "with great powers come great responsibilities", so GRUB allows you to lock down some features and boot entries to allow only the intended users to go through.
When talking of security in computer systems one often needs to analyse the situation one is in and choose the appropriate options. If you have hackers getting physical access to your computer system the GRUB security measures won't last a second (pretty much nothing would do). Your best bet in such a situation is to keep the hard drive encrypted, or if your hard drive can be password protected, use that option.
However, the majority of us don't have to worry about hackers with physical access as much as our not-so-computer savvy relatives and friends fiddling around with the system. That is what we have the log in passwords for (they are not secure enough for hackers, trust me!), and that is the situation where you would be wise to make use of GRUB security features.
It is also a good practice to password protect the recovery mode entries as they can be used by any user to gain root access.
GRUB security features allow you to lock down the editing of boot options accessed by pressing the 'e' key and they allow you to password protect selected or all boot entries.
Follow the steps below to see how to password protect GRUB entries:
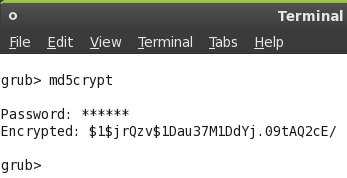
- Fire up the terminal. Type grub and press enter. The prompt would change to something like 'grub>'.
- Enter md5crypt at the GRUB prompt. Type in the password when prompted for and press enter. The command will return you password encrypted as an md5 hash. You will need this so make a note of it or copy to the clipboard.
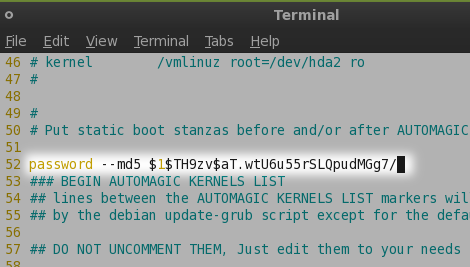
- Now we need to edit the /boot/grub/menu.lst file. You are advised to make a backup of the file before editing it in case something goes wrong.
- Enter the line password --md5 <the copied md5 string from step 3> before the line that reads: "BEGIN AUTOMAGIC KERNEL LIST" (actually it just needs to come before any of the boot menu entries, so you can write it anywhere as long as it is before them).
- If you save the file at this moment without any further edits you would have locked down interactive editing in GRUB. The administrator or in this case you would have to press 'p' key and enter the correct password to access these advanced options.
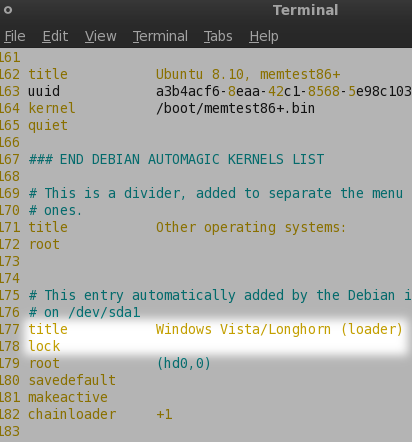
- If in addition you want to lock down specific menu entries so that anyone without the knowledge of the correct password cannot boot into that operating system you should add the word lock all by itself on a separate line just after the title specification for each entry in the menu.
- The next time anyone tries to select the locked menu entry he/she will be required to enter a password before he/she can boot into the corresponding operating system.
- To lock the recovery mode entries it is best to change the line lockalternative=false to lockalternative=true. This will lock down all future recovery mode entries as well even if you update the kernel.
What security features do you use to secure your system? Have you encrypted your hard drive? Or do you use a BIOS password? Let us know in the comments. Also check out how to add a custom background to GRUB menu