Encryption is a boon to anyone using a digital device. The internet would be a dangerous place without encryption, as would Wi-Fi access points and password-protected devices like iPhones.
However, the iPhone is no longer the bastion of security it once was. US law enforcement agencies are using a cheap tool to bypass iPhone encryption, drastically reducing privacy while damaging security.
Here's a deeper look at the new GrayKey tool, what it does, why it's dangerous, and why Apple is worried about it.
Apple vs. The FBI
Before we examine GrayKey, a little background context for iPhone encryption and attempts to crack it.
Remember the San Bernardino iPhone? After a terrorist attack in San Bernardino, the FBI took Apple to court. The FBI wanted Apple to create an encryption backdoor that would let them skirt the iPhone security of one of the deceased terrorists. Naturally, Apple refused, correctly asserting that once the backdoor was created, it would never be closed.
The Israeli-based security firm, Cellebrite, eventually found a way through the Apple security mechanisms using a previously unknown vulnerability. And there was nothing of note on the phone. Also note that at the time, the Cellebrite service cost $5,000 per device and the phone had to be sent to their secure facility.
Flash forward to 2017. A company known as Grayshift appears on the market, selling their new product: GrayKey. The purpose of GrayKey was unclear until Thomas Fox-Brewster revealed the device in a Forbes Exclusive, including several pictures as well as an overview of exactly what the GrayKey iPhone unlocker does.
The GrayKey iPhone Unlocker
Here's what is known about the GrayKey iPhone unlocker so far.
The GrayKey device itself is a small, gray box measuring four inches deep by two inches tall. The box comes with two Lightning cables sticking out the front for connecting two iPhones at a time.
An iPhone connects to the GrayKey device for about two minutes, after which they are disconnected but not yet cracked. The actual cracking process time varies depending on the password strength.
An easy passcode takes around two hours to crack via brute-force, while more difficult passcodes (six digits) can take three days or longer. The GrayKey documentation, also seen by Malwarebytes, doesn't mention cracking times for longer combinations.
When the crack finds the device passcode, the phone will display a black screen showing the code with other device information. (Tips for creating a strong and memorable password.)
GrayKey Downloads the Entire iPhone
The unlocker displays the device passcode, but it also downloads the entire iPhone file system to the GrayKey device. The GrayKey then connects to a web-based interface where it is available for analysis.
The image below shows the results of a cracked iPhone X. Note the "Found passcode," the very recent "Software Version," and the "iTunes Backup" and "Full Filesystem" available for download (including their SHA256 hash).
GrayKey Costs a Lot of Money
The GrayKey iPhone unlocker has two different versions.
The first model costs $15,000 and requires internet connectivity to work. In that, the device is geofenced to its initial setup network to make sure the GrayKey isn't easily transferred. Other reports claim the persistent internet connection model also only allows 300 unlocks, working out at $50 per iPhone.
The second model costs $30,000 and works offline, with no apparent limit on the number of uses of the GrayKey device. The device will presumably work until Apple finally figures out the vulnerability and patches it.
Which Law Enforcement Agencies Have a GrayKey?
While these are undoubtedly huge sums of money, law enforcement agency budgets will easily (or miraculously, depending on the agency) stretch for a tool that creates an entirely new avenue of information. Especially one previously unobtainable for many agencies, at least in such an apparently easy capacity.
An ongoing Motherboard investigation found several different agency types had already bought a GrayKey:
- Local police: The Miami-Dade County Police indicated that they might have purchased a GrayKey device.
- Regional police: The Maryland State Police and Indiana State Police have issued procurement forms for GrayKey devices.
- City police: Documents also indicate that the Indianapolis Metropolitan Police Department received a quote from Grayshift regarding GrayKey devices.
- Secret Service: Emails show agency plans to purchase six GrayKey devices.
- State Department: The Department of State's Bureau of Diplomatic Security bought a $15,000 item from Grayshift in March 2018, according to public procurement records.
- DEA: The Drug Enforcement Agency issued a Sources Sought document for an offline GrayKey device.
- FBI: Online public procurement records show the FBI looking to buy six GrayKey devices.
If Grayshift's GrayKey continues to provide authorities with previously unobtainable iPhone data, you are likely to see more agency procurement forms too.
What Is Apple Doing to Stop GrayKey?
As you might imagine, Apple is not best pleased with the iPhone's security being so publicly breached. And not just old iPhone's---we're talking top of the range devices running some of the latest versions of iOS. Apple isn't going to sit and wait for Grayshift to keep the vulnerability open.
Instead, in the current iOS 12 public beta, there is a new feature that drastically limits access to the Lightning port of a locked iPhone. (More features coming to your iPhone with iOS 12!)
"We're constantly strengthening the security protections in every Apple product to help customers defend against hackers, identity thieves, and intrusions into their personal data," an Apple spokesperson told Reuters. "We have the greatest respect for law enforcement, and we don't design our security improvements to frustrate their efforts to do their jobs."
iOS 12 will render Lightning port brute-force attacks useless by disabling access via that route after just one hour. The new USB Restricted Mode will stop any data communication from a newly connected device after that 60-minute period, effectively rendering the GrayKey useless. The current USB Restricted Mode settings have a time limit of one week, giving authorities a lengthy period to hopefully brute-force the password.
How Can You Protect Yourself Against GrayKey?
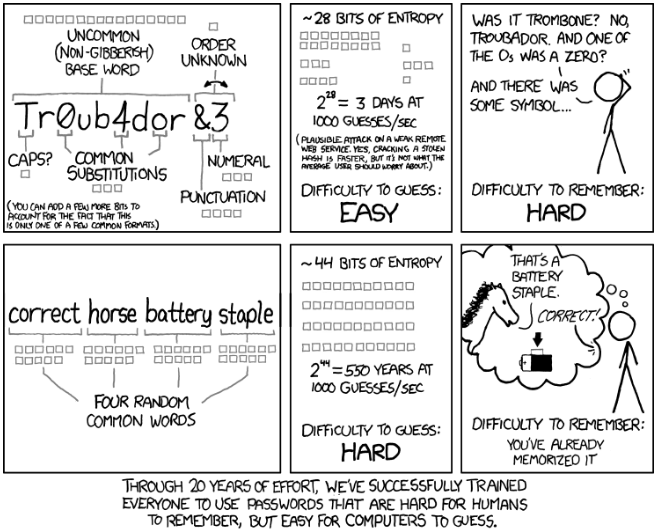
Given the incoming update to iOS 12 and the introduction of restrictions to USB Restricted Mode, there is only one thing you can do right now: update your passcodes. You should always use a minimum of eight digits to keep your phone secure. Alternatively, to truly bulk out your iPhone security, switch to a lengthier passphrase.
iOS supports custom numeric and custom alphanumeric codes of any length. A passphrase uses multiple words to create much stronger lock than your regular PIN or password. Check out the extremely relevant XKCD comic for more information:
The Ongoing Gray Area of GrayKey
Right now, law enforcement agencies hold the cards. In a sense, at least. An iPhone with poor security is vulnerable. However, this situation might not last long, unless Grayshift keeps finding vulnerabilities and workarounds for Apple's iPhone security patches. Furthermore, the GrayKey isn't unprecedented.
The IP-Box was a similar device that could access the information of locked iPhones running older iOS versions. Its functionality ceased with the iOS 8.2 update but gave rise to the IP-Box 2. The IP-Box 2 is still widely available but requires knowledge of how to remove integrated circuit chips to place in the device.
There are other implications, too. Is the iPhone permanently vulnerable after the password cracking completes? Can the iPhone owner use their phone as normal again, or will it need to be replaced?
And finally, how should authorities decide when to use their GrayKey device? I mean, is there a defined protocol that governs device password cracking using a third-party tool? Do they need an affidavit, reasonable suspicion, and so on?
The ongoing implications and debate surrounding iPhone password cracking using a GrayKey device will continue. I'm sure the majority of readers expect law enforcement to do as much as they can to protect victims. If password cracking becomes a core tenet of civic security, do you trust the authorities to exercise that power at the right time?
And would you just increase the amount of encryption on your device to counteract their efforts?