Google just banned the privacy app Disconnect from the Play Store, again. Disconnect can shield users against invisible tracking tools, while increasing consumer awareness on surreptitious data-collection methods. It also functions to some extent as an anti-malware tool.
The Tor Browser's developers thought enough of Disconnect to make it their default search engine. It's as secure and private as anyone can expect. And it explains why they got banned. Google – or any large data companies – commoditize search data by analyzing, repacking, and then selling targeted ads to interested parties. Encryption and other privacy and security tools damage this revenue stream.
Why We Should All Be Concerned
The main question extending from Disconnect's banning: How can users protect themselves against secret data sharing?
The banning also brings up important questions on security and the ethical treatment of customer data. Given the broader picture of illegal government surveillance, and Google's attempts to drive its competition out of business, can we trust Google?
Google's Reason for the Banning
After the first banning in 2014, Disconnect posted in its blog Google's statement: No app can interfere with the function of another app. Disconnect then redesigned the Android version of its service, to meet the requirement. At present, the Android version only informs users as to which services track them online. Even so, Google banned them again, this time without issuing a statement.
So why would Google ban an app which doesn't violate the terms of the Play Store agreement?
How Does Disconnect Threaten Google?
Disconnect shields users from multiple forms of invisible tracking methods. In its free version of the Android app, its efforts center on three fronts.
First, it allows users to search the web using their favorite search engine, but without turning over user data to search-engine giants. Second, it aids in eliminating websites from tracking user website history.
Unlike most ad-blockers, it does not require root access (what's root access?), and--rather than blocking ads—Disconnect identifies tracking methods that offer potential routes for malware delivery. It also can block potentially dangerous tracking elements. It by no means blocks advertisements. Disconnect specifically designed the Android version of their app to skirt around the restrictions of the Play Store, which specifically bans ad-blocking apps, such as Ad-Away and Ad-Block Plus. Third, the app informs users on how their information is used by corporations.
The paid version throws in a Virtual Proxy Network (VPN) service, which anonymizes users' Internet Protocol (IP) addresses. VPN works by encrypting (what is encryption?) user traffic and routing it through a proxy tunnel. This, in effect, allows users to hide unique identifying information from potentially unwanted surveillance. However, whether or not Disconnect's service stands up to the WebRTC bug remains unknown. Those interested in analyzing their browser's security can check the Browserleaks site for results. To my knowledge, the WebRTC bug affects the Chrome - but not Firefox - browser.
Google's failure to supply Disconnect with a rationale means the app's creators can't redesign their software. In effect, there's no way to get Disconnect published in the Play Store, reducing its potential userbase. Disconnect's story isn't an outlier, either. A growing chorus of developer voices joined in protesting Google's oftentimes opaque decision-making process. For example, Grooveshark's banning seemed to come under nebulous condition - although it briefly returned before Grooveshark itself succumbed to legal blows. The Amazon Store's banning stems from its direct competition to the Play Store. The list goes on, and on. However, with Disconnect the developers followed Google's rules—and it got banned anyway. The takeaway from the removal: Apps threatening Google's revenue stream won't inhabit the Play Store for long.
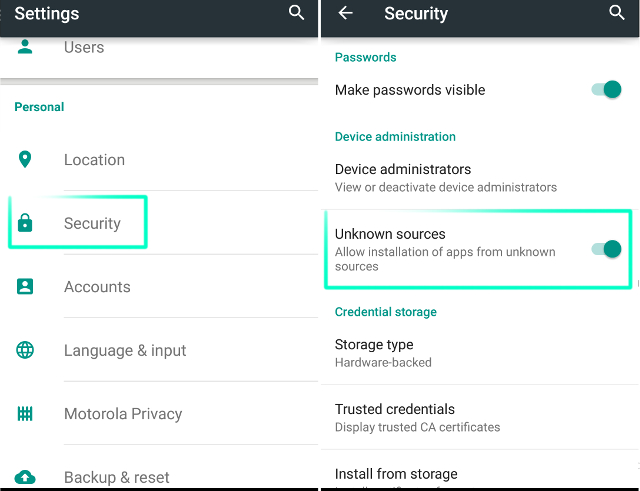
Installing Disconnect
Because Disconnect hails from outside the Play Store, users must first enable third party apps in Android. To enable a third party app, go to Settings > Security and check Unknown Sources. On your phone, download Disconnect from disconnect.me. You will receive a prompt on where you want to download the file. Most of the time it goes to the Download directory in Android, which is located on either your SD card or in internal memory.
You will then need a file explorer (such as Solid Explorer) to locate the file in your Downloads directory. Use the file explorer to select the file. Then choose to open it with the Package Installer, if prompted.
Using the Free Version of Disconnect
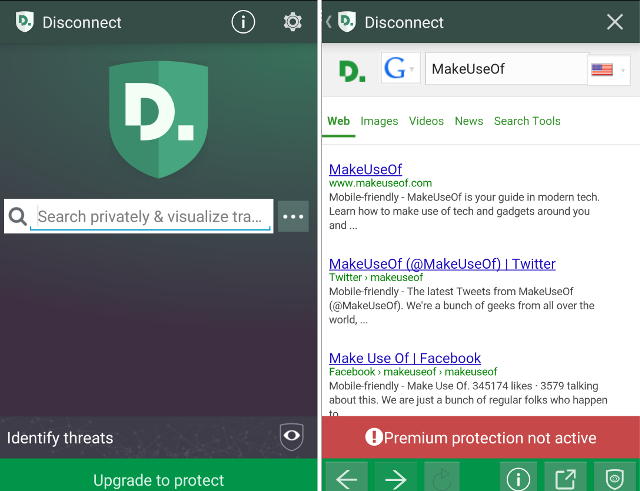
On Android systems, the free version of Disconnect offers two main functions: Shielded searches, and information on surreptitious tracking elements.
Shielded Searches and Malware Protection
Disconnect's free version performs web searches using any major search engine. Disconnect claims to encrypt your searches – even they don't know what you've searched for. Also as a sign of its pedigree, Disconnect just got transplanted into the Tor Project, which is the premiere privacy tool on today's Internet--and here's how to use Tor.
To use it, just open the app and type in any search term.
Scan Website for Nonsecure, Secret Tracking Elements
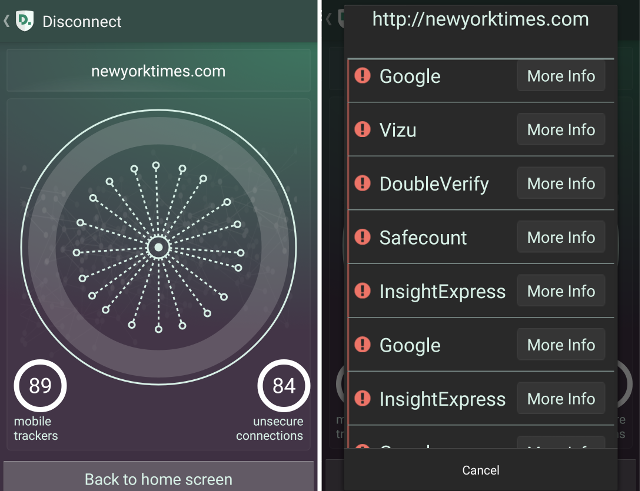
To scan a website for nonsecure elements, start the app and then select Identify Threats from the bottom of the screen. You can do the same scans from within the Disconnect browser.
Next, type in the name of a website that you'd like to scan for nonsecure elements. After completing the scan, Disconnect presents a graphical depiction - like spokes on a wheel - of the various information sharing sites which get unencrypted access to your data. Below you'll see screenshots of an offender with more nonsecure tracking elements than any pornography or gambling website.
Other Platforms
Disconnect also makes itself available on Chrome (although it hasn't been banned there) and iOS. You can download them here:
Why We Need More Privacy Apps
In 2015, Marcus Robertson, faced 20-years of imprisonment on charges of supporting terrorism. Prosecutors alleged that 20 books, of his more than 10,000 deep eBook collection, contained "terrorist" passages. Apps like Disconnect play a key role in molding a future in which reading habits don't form the basis for imprisonment or prosecution. In the larger scheme of illegal domestic surveillance, and the NSA's impressive technology, everyone should consider using encryption and proxy technology--and here's how to protect against illegal spying.
While Google can block privacy apps, it cannot destroy them. Because of Android's flexibility as an operating system, privacy-seeking users can simply download and install the applications direct from the developer's website.
Does anyone else have a privacy app suggestion? Let us know in the comments.