Ever heard that quote about trying to explain how a television works to an ant? I'm not calling you an ant, even though you are hard-working and enjoy the occasional sip of aphid milk. What I am saying is that I'm going to explain how Windows BitLocker works, without you having to have a degree in computer science and cryptography experience.
BitLocker is a feature of Windows 7 and 8 that is extremely useful, included in the operating system, and not nearly as many people know about it as they should. If you're curious about what other cool stuff your Windows operating system might have, check out Christian Cawley's, "The Top 5 Cool Hidden Features In Windows 8" and Yaara Lancet's article, "8 Hidden Tools In Windows 7 You Still Might Not Know About". Here, though, I'll be focusing on Windows' military-grade privacy tool called BitLocker.
What Is BitLocker?
Not all Windows' operating systems have BitLocker bundled with them. At this point, it is just in the Ultimate and Enterprise editions of Vista, and Windows 7, and with Pro and Enterprise editions of Windows 8. You can also find it in Windows Server 2008, Windows Server 2008 R2, and Windows Server 2012. What BitLocker is, it's a drive encryption tool. A drive encryption tool is something that takes all your data on any particular drive and make it completely unreadable to anyone but you. If you don't have one of these operating systems, I suggest you take a look at TrueCrypt and our TrueCrypt User's Guide: Secure Your Private Files.
There are two meanings for 'drive' in this case. One is any volume or partition on a single hard drive. You need at least two volumes on the drive to use BitLocker - a main volume that you probably will do your day to day work in, and another volume that is at least 100MB in size that will be your system's volume. Your computer will boot from this volume. This volume can NOT be encrypted. That would make booting your computer very difficult.
The other 'drive' is any removable drive like your USB drive. This type of drive does NOT require a boot volume. Which is really cool, because if you encrypt your USB flash drive and you have sensitive information on it, you don't really have to worry about anyone getting that information if you lose the drive.
How Does It Encrypt My Drive?
BitLocker drive encryption takes all the data on your drive and applies a bunch of fancy math to that data. Remember, all data can be boiled down to just numbers so it can be manipulated with math. Officially, this math comes in the form of algorithms, or sets of instructions, such as AES - 128-bit or 256-bit encryption, and Diffuser.
Let's go through a very simplified process of encrypting the word 'USE'.
Diffuser takes those three letters and scrambles them. It could come out as ESU, SUE, SEU and so on. Then BitLocker creates the key, which is the way to unscramble that word, and holds on to it for you.
Now BitLocker applies AES. AES is the Advanced Encryption Standard adopted by the US Government as a standard in 2001 - hence the military-grade designation in the title. 128-bit or 256-bit encryption defines how many bits a single bit of your original data may be represented by. Now, a bit is just one piece of data, like a letter or a number. Then, the math makes that particular bit into a 'combination' or key that is either 128 or 256 bits long. It's like slapping a combination lock with a 256-numbers-long combination on a locker holding the letter 'U'. Think about that.
Let's go back to encrypting the word 'USE'. You have to open three different lockers with three different combination locks, each with a combination that is 256 numbers long. Now, you can see how this would be a pain to anybody but the most dedicated cracker.
This is where it gets military-grade, I mean tank tough! Remember AES? Well that application puts each combination lock through the math 14 times for 256-bit encryption! Now, you have to know 14 different 256-bit-long combinations to get at your letter 'U'. Forget it. Go home, cracker. Of course, BitLocker creates a key that will unlock, or decrypt that word for you.
At the end of it, there are two keys now needed to start the process of decrypting your data. If someone doesn't have access to both of those keys, they are going to have to be very patient, very smart, and very dedicated to get at your information.
These keys aren't physical keys of course, and they don't resemble passwords either. By themselves, they would look like gobledy-gook to ordinary folk like you and me. But what Windows does is allow BitLocker to use those two keys to get at your data, as long as you can prove to the computer that you are who you say you are. These keys are held by the Trusted Platform Module.
What is a Trusted Platform Module?
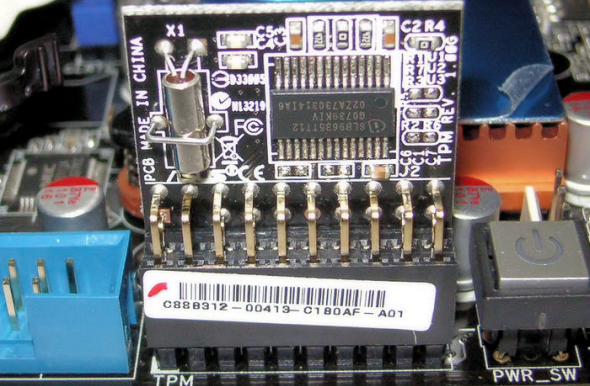
The Trusted Platform Module is another key piece in the BitLocker set of tools to protect you. This is a bit of hardware that can be found on most computers.
What it does is check out your computer each time it boots to make sure no one has been trying to mess with the start-up procedures to get around your encryption. What it also does is prevent someone from just slipping the hard drive out of your computer and popping it into their computer to get at the files.
Depending how you set up your BitLocker, your TPM may just let you log on to your computer. Or, you might set it up so that it requires a PIN number to continue to logging in. Or, you can create a USB key that has to be plugged into your computer when you boot, to get you to the login stage. Or you can go hardcore and set it up to require that you have a PIN AND a USB key. The TPM applies only to volumes that are physically on your computer. USB drives don't need a TPM, but they may need a PIN or USB key for verification.
There are computers without TPM's, but for most computers manufactured after 2006, the TPM module is already on the motherboard.
Is BitLocker Totally Safe?
Well, no, nothing really is. But it's as safe as you're going to get without having the budget of the CIA or MI-5. Speaking of government spying, the UK's Home Office has asked Microsoft to put a backdoor in BitLocker to allow them to have easy access to your data. Microsoft has flat out refused to do so. Score one for Microsoft.
So, How Do I Use BitLocker?
It's surprisingly easy to use if you are just going to encrypt your main volume on the hard drive in your computer. Check out this short video on how easy it is.
If you want to get into the guts of BitLocker and use it on external drives or set up the different TPM validation methods, it can get a bit more complicated. Microsoft does have a Step-By-Step Guide for BitLocker on Windows 7. I haven't seen any real documentation on Windows 8 yet. If you have, let us know in the comments, please.
Should I Use BitLocker Drive Encrypting?
BitLocker is the best protection for your data that you are going to get just by buying a Windows computer. If you are concerned about data theft and the security of your information, why wouldn't you make this military-grade tool a part of your computer security arsenal? It just makes sense. BitLocker is a serious tool developed for you by a company so many people think of as being evil at different times. I think this application is a redeeming quality for Microsoft and makes me feel less disgruntled about the cost of getting Windows.
What do you think? Do you currently use BitLocker drive encryption? I'd like to hear about your experiences with it. Do you feel safer knowing BitLocker is out there and may be a part of your Windows computer? Let's hear about it in the comments. No encrypting please.