Mark has previously described how you can use TrueCrypt to encrypt your sensitive data. While that is a great encryption software, it requires you to pre-allocate a fixed size to the container before you can store confidential data to it. If you are using only 10% of the allocated space, the remaining 90% of the space goes to waste. If you are looking for a more dynamic solution to encrypt files in Linux, eCryptfs might be the solution for you.
eCryptfs is a stacked cryptographic filesystem embedded within the Linux kernel (versions 2.6.19 and later). Being a stacked filesystem, it can easily encrypt and decrypt the files on your Linux PC as they are written to or read from the hard disk.
The greatest advantage of eCryptfs is that all encryption is made at the single-file level. This means that you don't have to create a fixed size container to hold your files.
There are several benefits of single-file level encryption:
- Since each file is treated differently, on a shared platform/server/directory, you can have different files encrypted by different users and each user can access only his/her files.
- All the cryptographic metadata is stored in the header of the file. This means that the encrypted file can be copied/moved from one location to another without losing its confidentality.
- It requires no special on-disk storage allocation effort. You don't have to pre-allocate 1GB (or more) of your hard disk space to store your sensitive data that maybe only few megabytes.
Installing eCryptfs
The installation method might differ in different distros. In Ubuntu 8.04 and above, you can install eCryptfs using the following command:
sudo aptitude install ecryptfs-utils
For Ubuntu 8.10
As eCryptfs is implemented in Ubuntu 8.10, you can easily set it up using the following command:
ecryptfs-setup-private
Once you have set it up Ubuntu 8.10, you will find a Private folder in your Home directory. To access to the folder, you need to mount it with this command:
mount.ecryptfs_private
You can now add your sensitive files into the Private folder. Encryption will be done as the file is added to the folder.
To unmount the folder, use the command:
umount.ecryptfs_private
For Ubuntu 8.04 or other Ubuntu-based distro
First create a folder in your Home directory and name it secret
mkdir ~/secret
Change the file permission so only you can access
chmod 700 ~/secret
Mount the eCryptfs to the secret folder
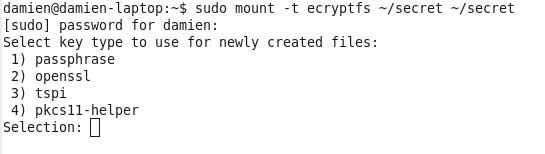
sudo mount -t ecryptfs ~/secret ~/secret
It will prompts you to answer a few questions:
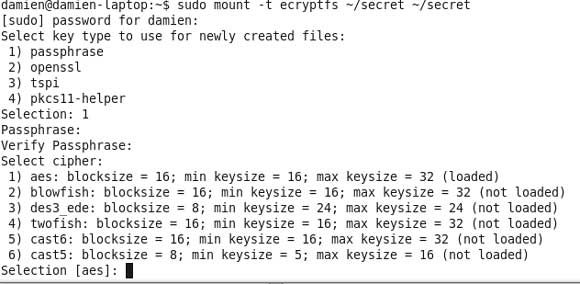
1) Selecting your key type for newly created files
Press '1' to select passphrase
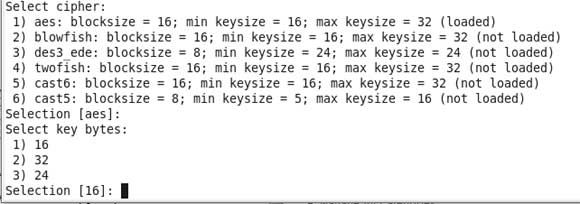
2) Selecting your encryption cipher
Press Enter to select the default option [AES]
3) Select key bytes
Press Enter to select the default option [16]
4) Enable plaintext passthrough
Type 'N' to select No.
That's it. You can now add files into the secret folder.
To test the reliability of eCryptfs, unmount the secret folder and see if you can open the files inside the folder.
sudo umount ~/secret
If all is good, you should not be able to open any files inside the folder.
What other encryption methods you use to protect your files?