<firstimage="https://www.makeuseof.com/wp-content/uploads/2011/05/RestoreDropbox01.png" />
Dropbox is arguably one of the best online file sync tools around. In fact, I do not have any geek friends that don't use Dropbox, but instead use it heavily. However, if you've been skimming through the tech news lately, you'll see that Dropbox is having some privacy issues as of late (here's one out of many).
Aside from the never-diminishing threat of a break-in by hackers, Dropbox has also said that it will turn over your data to the government if requested. This implies that, even if the data on their servers is encrypted (and not just the connection), they have a way to decrypt it and see what you're storing. Although I'm sure most of you don't have anything to hide, we feel more comfortable with some privacy. Therefore, encrypting the files before they are sent to the Dropbox servers is the way to go in order to keep eyes away.
There are a couple different ways of achieving this, as of late. My favorite method in the past has been to use Truecrypt, but having to create containers that store the encrypted information isn't the best for Dropbox, which constantly syncs changes. If I have to make 50MB+ containers, and changing anything in one of them means that I have to re-upload 50MB of encrypted info, then that is a little waste of time and resources. Instead, I need to encrypt files individually, and in a serious, not-cheesy way. ENCFS is the perfect solution for this kind of problem.
The Idea
The technologies behind ENCFS are a pretty tricky to explain, so I'll let you do that on your own time if you are interested. However, the principle of what it does is easy enough, so we'll dive right into that. The idea is that ENCFS creates two folders. One is for unencrypted data, and the other is for encrypted data. You'll want to have the unencrypted folder somewhere in your Home folder, while the encrypted folder should obviously be inside your Dropbox folder. Whenever you put something into the unencrypted folder, ENCFS goes to work and spews out the encrypted version into the encrypted folder, which Dropbox then syncs. If you do the same on a different computer, ENCFS will take the encrypted file and decrypt it, sending it to your unencrypted folder. It's simpler than it sounds.
Installing
To get started, you'll first need to install ENCFS. You'll need to look around in your package manager for the exact package name, but for Fedora it's fuse-encfs and in Ubuntu it's simply called encfs. Next, you'll need to head over to this site, download the contents, unzip, and copy the "gnome-encfs" file to an easy to access location. Then, switch to root if needed, and use (sudo)
install /path/to/gnome-encfs /usr/local/bin
. This program will help with automatically mounting this setup each time you boot up your computer. Alright, everything is now installed.
Create your Encryption Setup
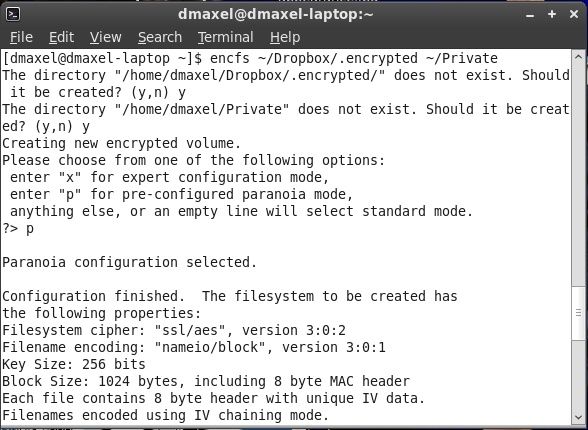
Next, we'll need to actually create the setup. To do this, you'll need to run
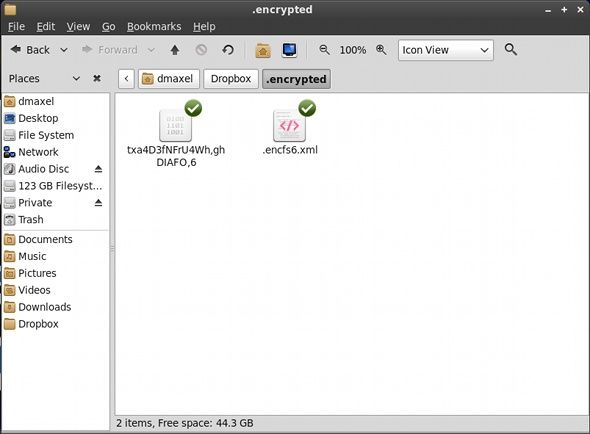
encfs ~/Dropbox/.encrypted ~/Private
. You can change the actual paths if you like. Just know that the path represented by ~/Dropbox/.encrypted is the folder where the encrypted data goes, and ~/Private is the folder where you put your unencrypted files into. The tilda represents your home folder and the period in front of folder names sets the folders to hidden (Hit CTRL+H in Nautilus to see hidden folders).
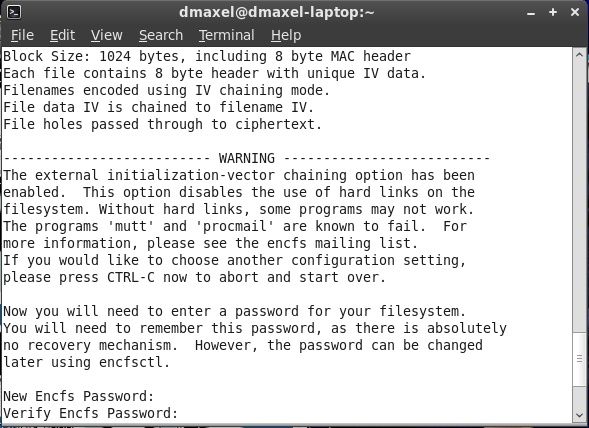
ENCFS will ask you a couple questions about your setup, such as whether to create the folders you specified if they don't already exist, what kind of encryption you would like (if you want an easy and very secure setup, hit p), and the password for your setup.
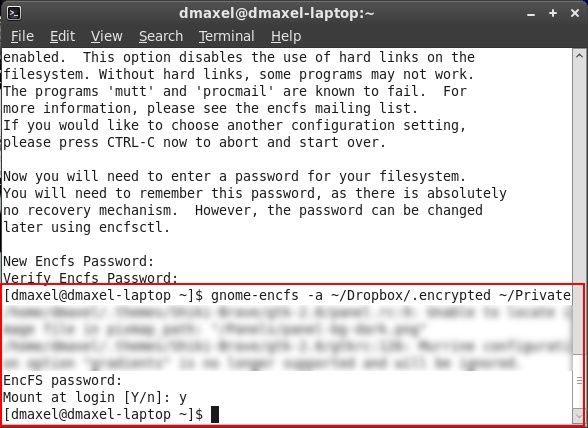
Next we need to automatically mount this setup. Type in
gnome-encfs -a ~/Dropbox/.encrypted ~/Private
and hit enter. You'll be asked for the password that you set earlier, and then whether to automatically mount the setup. Say yes, and you're done!
Conclusion
Congratulations! You're ready to go! You can start copying files into the Private (or unencrypted folder if you chose a different name/location), and see that encrypted files are being made in your specified Dropbox folder.
You'll also notice that there is an .xml file, which contains some information about the key. No, it isn't the key itself, so you're still safe if you sync that with Dropbox. However, if you feel extra paranoid, you can copy the .xml file to a different location, type
dropbox exclude add ~/Dropbox/.encrypted/.encfs6.xml
into your Terminal, and then delete the file (and make sure it's also purged via the Dropbox website). Note that, as far as I know of, it may be possible to use this setup with Macs as well, but Windows is currently not in the game. Therefore, this setup is most effective for people who use only Linux and want to encrypt files they know they only need between computers, and not on the go where Windows may appear.
Is encrypting your Dropbox data a high priority for you? Are you starting to think more about encryption now that some very good consumer options exist? Let us know in the comments!