In late 2017, Edward Snowden, The Guardian Project, and Freedom Of The Press announced the product of a collaborative effort: the Haven app. It can transform any Android phone into the ultimate mobile security system. But is Haven as powerful as some claim it to be?
How Haven Works
Haven's primary purpose is that it can protect your laptop or desktop computer from tampering. It uses every sensor on your phone to monitor the environment and alert you to any changes. With just a little bit of imagination you'll come up with many more interesting security uses for this app beyond monitoring your computer hardware.
While there are countless other Android apps out there that will do the same thing, the one thing that stands out about Haven is that both the alert message feature and remote access to the device is encrypted and anonymous.
The intent of Haven is that you use it on a burner Android. This is basically a cheap, spare Android you can wipe clean or destroy at any time without really caring. This could be a prepaid phone or a used one from eBay. People sell their old phones there all the time for next to nothing.
The idea is that you'll place it somewhere in a room where all of the phone's sensors can fully monitor the environment there.
The app uses all of the following smartphone sensor technologies:
- Camera: It'll catch any motion either from the front or the back camera.
- Accelerometer: If the phone moves or vibrates, the app will capture the event.
- Microphone: Any noise will trigger an alert.
- Light: The app also monitors lighting levels from the camera.
- Power: If your burner phone gets unplugged, you'll receive an alert.
If you place the phone in an ideal location in any room, all of these sensors work together to provide a pretty impressive security monitor.
Setting Up Haven
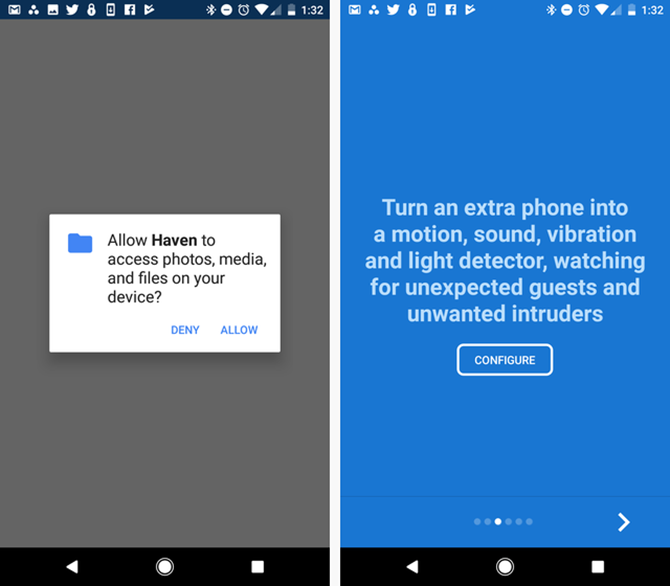
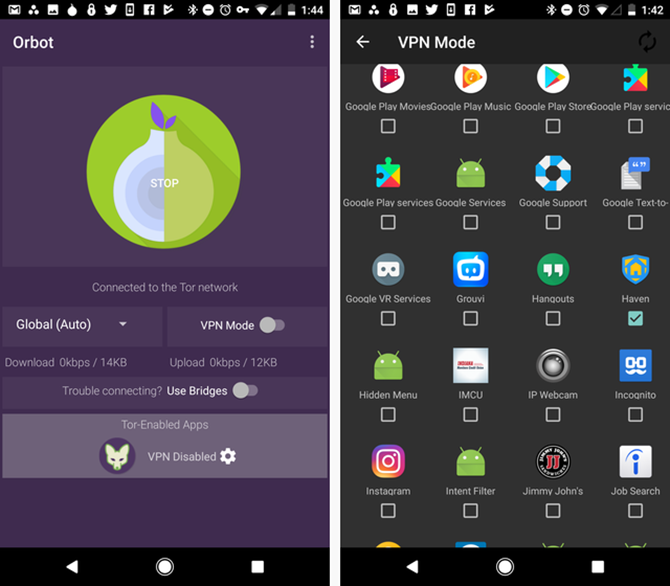
The Haven app is very easy to intall and set up. Just download it from Google Play; you'll need to download and install Orbot as well. Haven uses Orbot for anonymous remote access to the phone.
You'll need to provide Haven with access to a lot on your burner phone... this is why it's best used on a junk phone you never use. It gets full access to not only all sensors, but also all files stored on the device. As much as I like Edward Snowden and trust the Guardian Project, I would never advise installing this app on your primary phone.
Once you've installed the app, you'll walk through a quick wizard. One of those steps is to configure the sensors on the Android device.
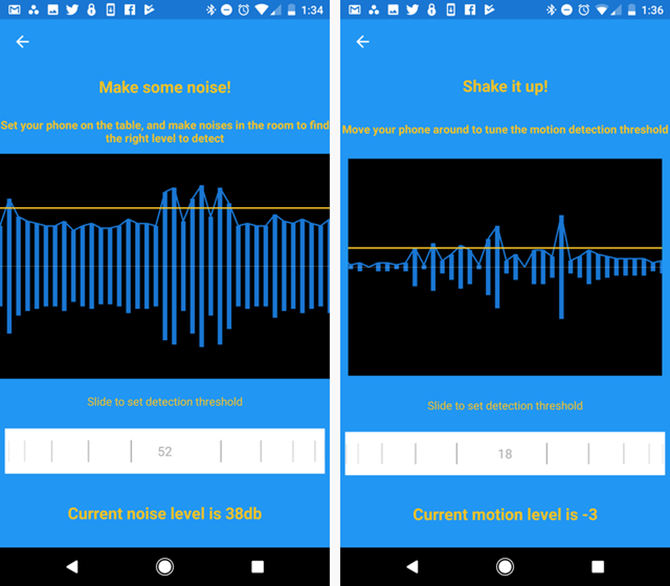
Setting Up Haven's Sensor Sensitivity
The next few screens guide you through setting up the appropriate sensitivity for the camera, the accelerometer, and the microphone.
Your settings here will vary depending on how you want to use the application.
- Monitoring a hotel room: Placing the phone propped up on a night stand so it has full view of the room (including your laptop) is the best option. You may need to adjust microphone sensitivity to a level just above the sound of the air conditioning or traffic. You can set motion sensitivity very high, since nothing should move in the room while you're gone.
- Monitoring your laptop bag: Sliding the burner Android into a pocket of your laptop bag, you can adjust the accelerometer threshold to very sensitive. Be wary of any natural vibrations nearby (like construction work outside or a nearby subway train) which could set off the sensor. In this use case the camera sensor or sound detection isn't really useful.
- Monitoring your office: Sound, camera motion, and the accelerometer could all come in handy to monitor your office, but if you have a home office you may need to reduce the camera motion sensitivity to ignore any pets you have roaming around.
- Monitoring a safe: The most important sensor here will be the accelerometer. Place your laptop in a hotel safe with the burner phone on top of it, and set for maximum sensitivity. Even someone just opening the safe door will provide enough movement to trigger an SMS alert to your phone.
You can always reconfigure the sensitivity settings in the apps Settings area.
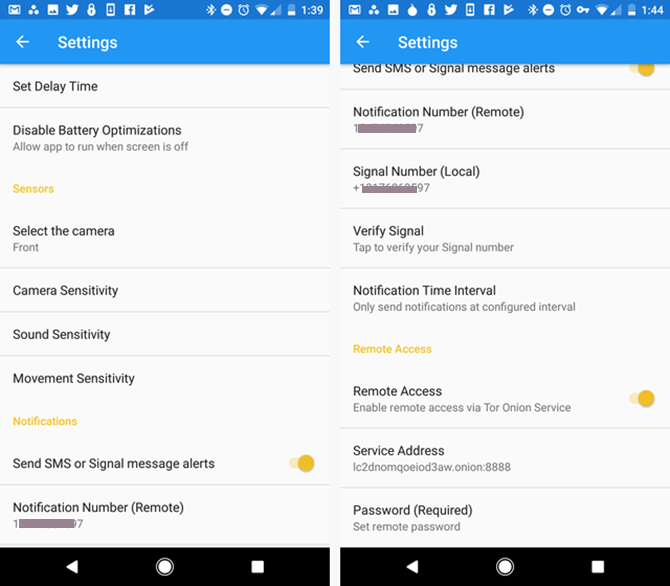
Configure SMS and Tor Onion Service
This is also where you can:
- Configure SMS alerts or your Signal messaging account
- Select which camera on your phone to monitor
- Configure remote access to the phone via the Tor browser
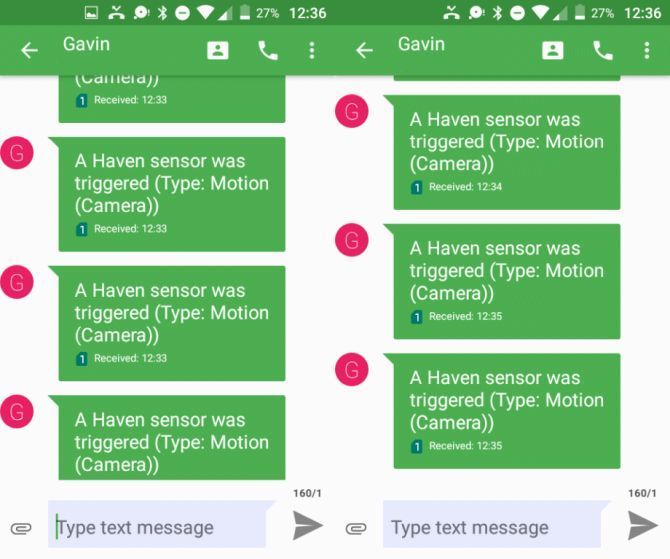
Adding SMS (or even Signal messaging) works, but be careful. If you set the app to message every time there's an alert, you could get an influx of many incoming messages every few minutes.
Luckily, the app lets you adjust how often alerts go out, so you can reduce the flow if the sensors ever do get triggered.
Setting up and configuring Orbot for Tor browser access to your phone is quick and easy. You just install the app, and then under Tor-Enabled Apps, tap to add the Haven app.
At this point, you're ready to start using the burner phone as a personal security device.
Using Haven
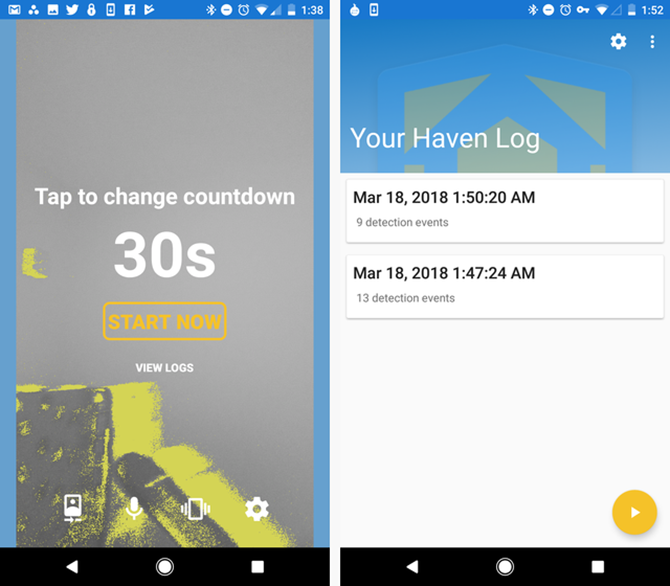
When you press the yellow play icon on any screen in Haven, it'll start monitoring. It's set to do a default countdown by 30 seconds before activating. Presumably this is to give you time to leave the room.
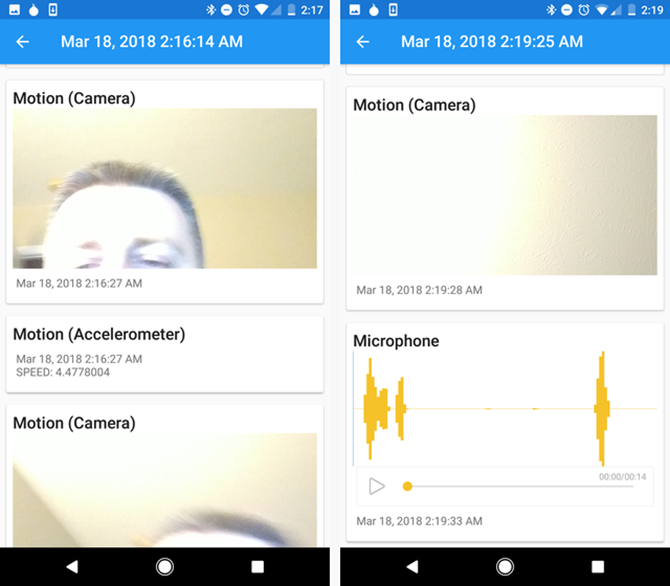
As alerts occur, the app logs all of the motion and sound from the room to its local storage. Later, when you return to the room, you can review the log and scroll through all of the alerts that occurred while you were gone.
You can configure the frequency of alerts that the app will send via SMS---either periodically or on every alert.
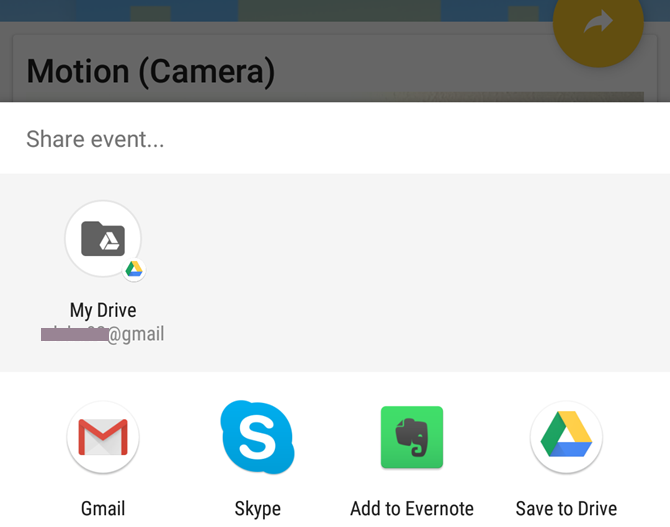
When reviewing all of the images and sounds you've captured, you can click the share button on any one of the logs to export it to any other app or cloud service the phone has access to.
It's quite stunning just how much data the app captures. During testing, any time I entered the room, the phone immediately started snapping a picture every second, and recording any noise I made.
A carefully placed burner Android could easily capture a theft in progress, including clear snapshots of the thieves, and recording everything that was said in the process as well.
Remotely Accessing Logs With Haven
In my opinion, the coolest feature of Haven is that it lets you access all recently captured logfiles via a secure and anonymous Tor connection. We've covered how to convert your Android phones into a home security system, but that solution doesn't have encrypted and anonymous remote access via a Tor browser.
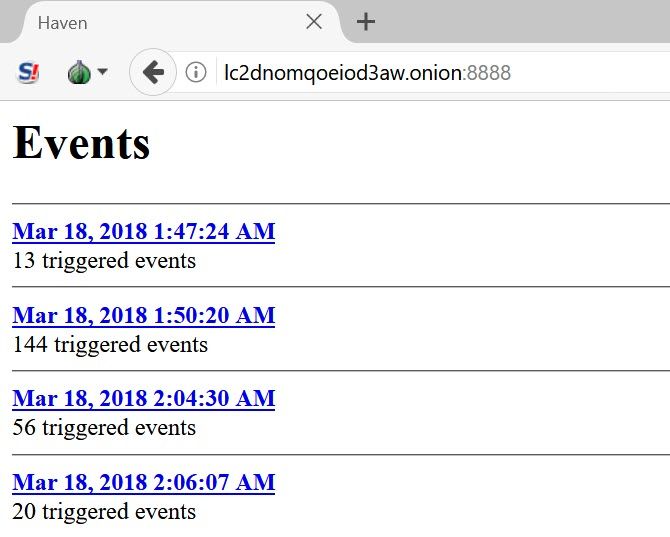
Once you have the Haven app configured to use Orbot, your phone will host its own onion site. The address of this site is displayed in the settings. All you have to do while your burner phone is actively monitoring the room, is access the onion page from your computer, using the Tor browser, and you can see all events that occured.
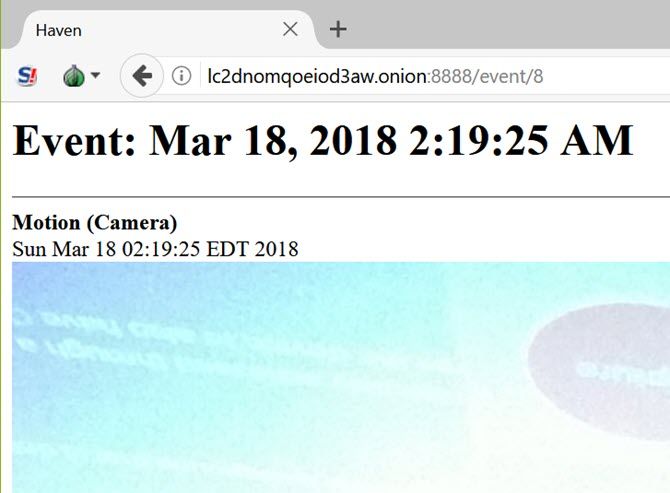
Then, just click on any of the logfiles to view individual alerts.
You'll have access to all of the full-resolution photos captured by your phone. As you scroll down you'll also have access to all of the motion alerts and sound recordings.
Downloading any of the media pulls it directly off the phone and onto your device, where you can do whatever you like with it.
Pros and Cons: Some Final Words on Haven
The ability to access the Haven app remotely and anonymously is a nice feature, but keep in mind that the phone has to be turned on and working in order to access these files. Should a would-be thief realize the phone is monitoring them, all they have to do is turn it off and you've lost all access to the alerts.
With that said, you just need to be smart with where, and how, you place the burner phone for your specific situation. But that also raises other questions.
Snowden, the Guardian Project, and Freedom Of The Press advertise this app as a way to "protect personal spaces and possessions". It definitely accomplishes that purpose. However, it is also converts any mobile device into one of the most effective and inconspicuous spy devices.
With a burner Android installed with this app, you could place it in any room and then leave the room. The phone will continue recording every single movement and sound of every person there. It may not be an app that will invade your privacy, but it's an app that'll let people invade other peoples' privacy without very much effort.
As with all things, with great power comes great responsibility. Using Haven, you'll have assurance that your space hasn't been invaded by uninvited guests. At the same time, you'll need to accept the responsibility that comes with using such a powerful surveillance application.
If you travel a lot, you'll want to make sure to read list of gadgets to keep your home secure while traveling. Also, if you haven't yet, you should definitely perform a personal security audit.
Image Credit: logoff/Depositphotos