If news reports are to be believed, hackers are a demographic all in their own. Well, they could be because security breaches of our personal accounts are a real and present danger. Just this February, 250,000 Twitter accounts were hacked. Wall Street Journal and New York Times were among the marquee names. Maybe you were among the numbers too. The good part of it was that Twitter reacted with alacrity and plugged the hole before it gaped open.
Sites like Twitter are not soft targets. They are protected by firewalls and other safeguards. Twitter has even implemented security protocols like DMARC for stronger phishing protection. But even as I write this, news has come in of a hijacked Associated Press Twitter account being used to broadcast false update of an attack on the White House. The Stock Market nosedived. Twitter will beef up its defenses. We, the users are part of those fortifications. Usually, we are its weakest link too.
The Ground Covered So Far…
My friend Chris gave us the absolute basics you need to know to secure your Twitter account. Let’s rehash them again quickly:
- Beware Phishing
- Don’t Reuse Passwords
- Manage Third-Party Apps
- Improve Your Browser & Computer Security
- Restrict Password Resets
- Use a URL Expander
- Lend a Helping Hand
I strongly urge you to read his popular article to grasp the first things you need to do. Here are a few more Twitter tips that should be useful to protect yourself against hackers.
Deal With Spam
An attack could come disguised in the form of a spam message on Twitter. Spam attacks take many different forms. Twitter recognizes aggressive following; exploiting @reply or @mention to post unwanted messages; and even creating multiple accounts as spam behavior. It could also be something as innocuous as posting unrelated links. The trick is to recognize spam early and take action to report it. Here’s how…
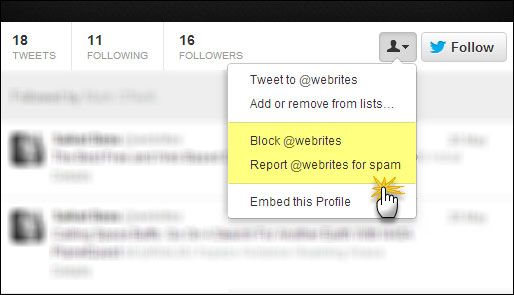
- Click through to the spam account’s profile page.
- Click the little silhouette icon next to the follow button to reveal the dropdown.
- You can use the options (see screenshot) to report an offending account for spam. Alternatively, you can also block the account.
Twitter does not automatically suspend the suspected spam account. Though it prevents the user from following you or replying to you. You can also file a more direct violation report. Twitter has a support page which tells you all about how to report violations and any other suspicious activity.
Benefits of Protected Twitter Accounts
A Twitter timeline is public by default. You can exercise the option to set your tweets as ‘protected’. Protected Tweets are visible to your approved Twitter followers. A protected Twitter account gives you more hands-on control over who follows you. Each follow request will need your express approval. Your tweets will only be visible to your followers. Your protected tweets will also not show up on Google results.
Protecting your Twitter account is a more secure strategy, but it may come at the cost of open interaction. The Twitter support page goes into the nitty-gritty of protecting and unprotecting your tweets.
Do Not Share Your Location
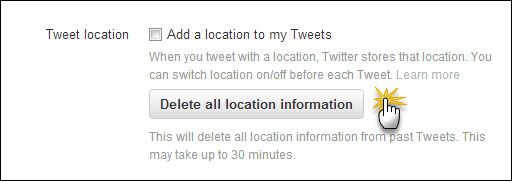
Though sharing your location information may not lead to your account being hacked, no one can promise that it won’t happen to your home…which is even worse. PleaseRobMe is an interesting website that tries to highlight this danger of over-sharing information on social media. For instance, sharing your location information could lead a burglar to your house when you are somewhere else.
The Settings page on Twitter takes you to the option of turning off your location information and also deleting all past references to it with a single click. You can also go into the location settings of your smartphone and disable the sharing.
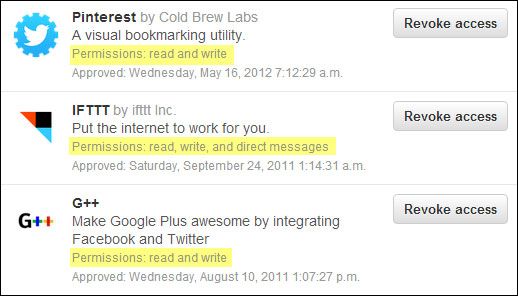
Do Not Blindly Allow Third Party Apps
Third-party apps connected via your Twitter account have two levels of authorizations - read-only, or read-and-write. In effect, an app can access all the information in your Twitter account. An app with read and write permission can also post updates on your behalf. Also, your tweets may be protected, but images accessible through services like Instagram may not be. This represents a potential risk if an app in question is not legitimate. This brings us back to the moot point of carefully vetting each third-party app we grant access to, and periodically revoking access to apps we no longer need.
Be Cautious With 'Out of The Blue' Direct Messages
I just have to reiterate this again. There have been spates of direct message and email malware attacks. Direct Messages (DM) are supposed to be one-to-one interactions between two parties and is supposed to be private. In reality, DMs may be tapped by third-party apps which have access to your Twitter account. Phishing scams and backdoor Trojans also rely on links within messages sent to an unsuspecting account. Twitter advices against following ‘hundreds or thousands of accounts without having a look first.’
It is actually easy to detect phishing attacks with a bit of care. For instance: check the text and substance of the message. Also, be extra careful on mobile devices because smaller screens may make it that much more difficult to decipher a fraudulent screen. So, wait to check it out on a larger screen before you click it.
Here’s an excellent read on phishing at Fraud.org.
Sign Out Of Public Computers
This precaution sounds so obvious, but you would be surprised how many forget to do it. If you are on a shared computer, remember to sign-out of Twitter to prevent someone from getting access to your open account. In a similar vein, always use a passcode to lock your smartphone and prevent snooping eyes.
Disable Java
Java is unsafe say security experts. The U.S. Department of Homeland Security has actually issued a public advisory on disabling Java if not needed in your browser. It is always a good idea to continually update Java, though disabling it could be a cautionary tale in closing the backdoor before someone sneaks their way in.
A final note: If your Twitter account has been breached, you can reset your password. Follow this Twitter support page to secure your account and stop further unusual behaviors
The ease of tweeting sometimes lulls us into a false sense of security. We forget that Twitter is arguably the most open of all social sharing sites. That’s the fruit as well as the peel we can slip on. If you spend a better part of the day on social media, you will appreciate that Twitter’s security settings are far easier to understand and set than those of Facebook. Now, we just have to give it some thought and a few minutes so that we don’t fall prey to hackers. What other Twitter security tips would you like to suggest? Did you learn it from bitter experience or are you among the wise ‘n cautious folks who play safe rather than be sorry?
Image Credit: Shutterstock