Apple has a good reputation for security, even on Macs, where you can sideload third-party apps. That's possible because of System Integrity Protection (SIP). Although it is excellent, it does impose restrictions when installing certain apps.
Fortunately, we have the option to turn it off on Macs—on both Intel-based and Apple silicon models. This guide will show you how to disable System Integrity Protection (SIP) on your Mac.
What Is System Integrity Protection (SIP) on a Mac?
System Integrity Protection is one of the important security features built into your Mac. It prevents malicious apps from accessing your Mac's root user files, ensuring no virus, malware, or ransomware can modify your Mac's protected files or folders.
On the contrary, because Apple enables SIP by default on your Mac, you'll face restrictions when installing apps from unknown developers. Even though it's a security feature, you may want to turn it off when installing specific apps you are confident in, but Apple doesn't trust yet.
SIP protects the following locations on your Mac from unauthorized access:
- /System
- /sbin
- /bin
- /usr (but not /usr/local)
- /var
- /tmp
- /etc
While SIP protects these folders from being accessed by applications and administrators with insufficient permissions, it also prevents malicious operations such as code injection, runtime attachment, DTrace, and unsigned kernel extensions. There are various reasons why Macs are more secure than Windows PCs, and SIP is one of the crucial ones.
How to Disable SIP on Your Mac
You'll need to enter macOS Recovery to disable SIP on your Mac, and the steps you need to follow differ based on whether you use an Intel-based or Apple silicon Mac.
If you've got an Apple silicon Mac, shut down your Mac and wait for 20 seconds. Then, hold the power button until you see the "Loading startup options" message under the Apple logo. Then, select Options and click Continue to enter the macOS Recovery screen.
However, if you have an Intel-based Mac, restart your Mac and wait for 30 seconds. Press the power button and immediately hold Command + R keys on the keyboard until you see the Apple logo. Your Mac will boot into macOS Recovery after a while.
Once you've entered macOS Recovery, you can turn off SIP on your Mac by following the steps below, irrespective of the model you have:
-
Select the user that has administrator rights and click Next. Type the password of the account if prompted and select Continue.
-
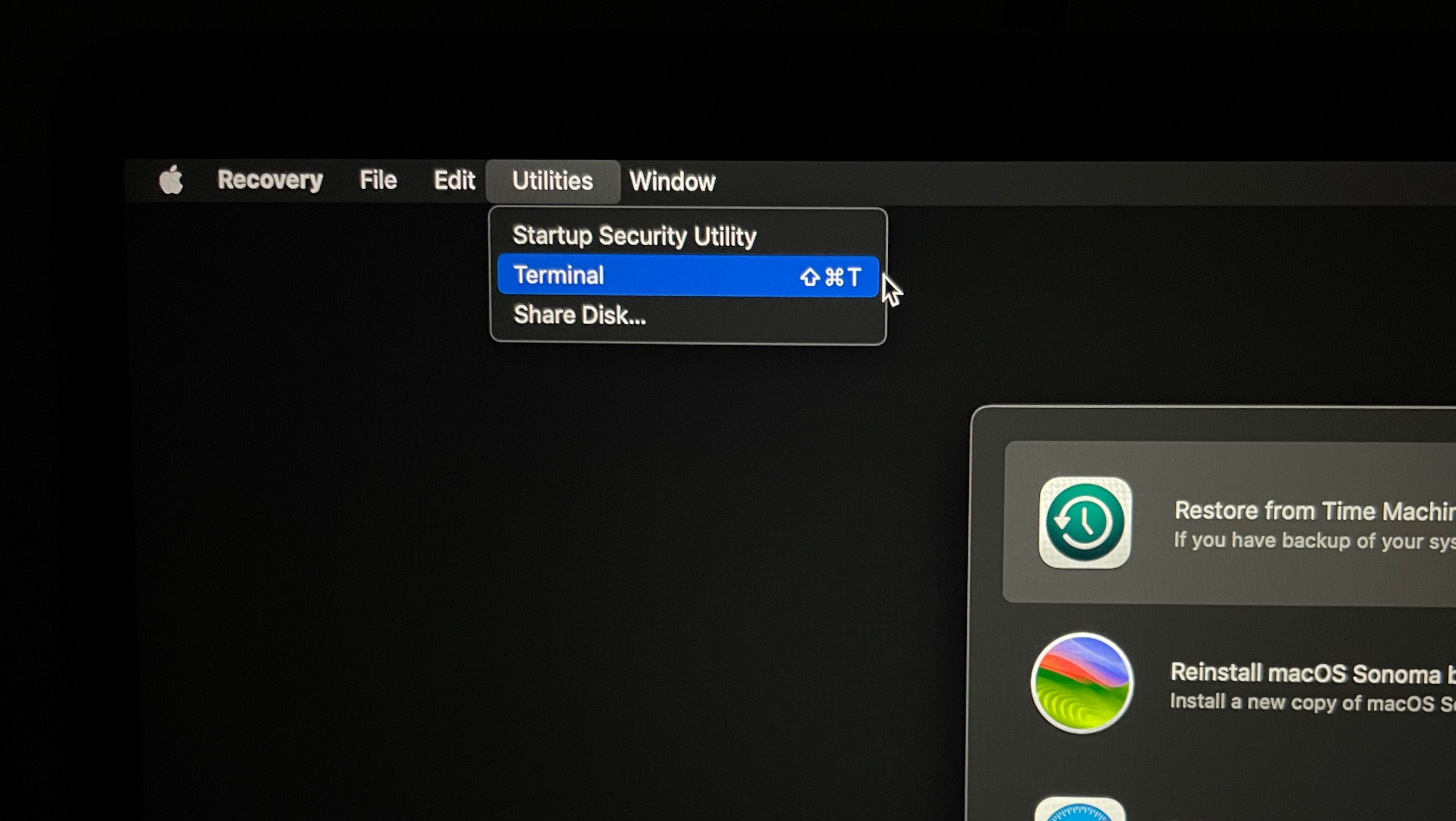
Click Utilities from the menu bar and choose Terminal. Alternatively, you can press the Command + Shift + T on your keyboard to launch the Terminal app.
-
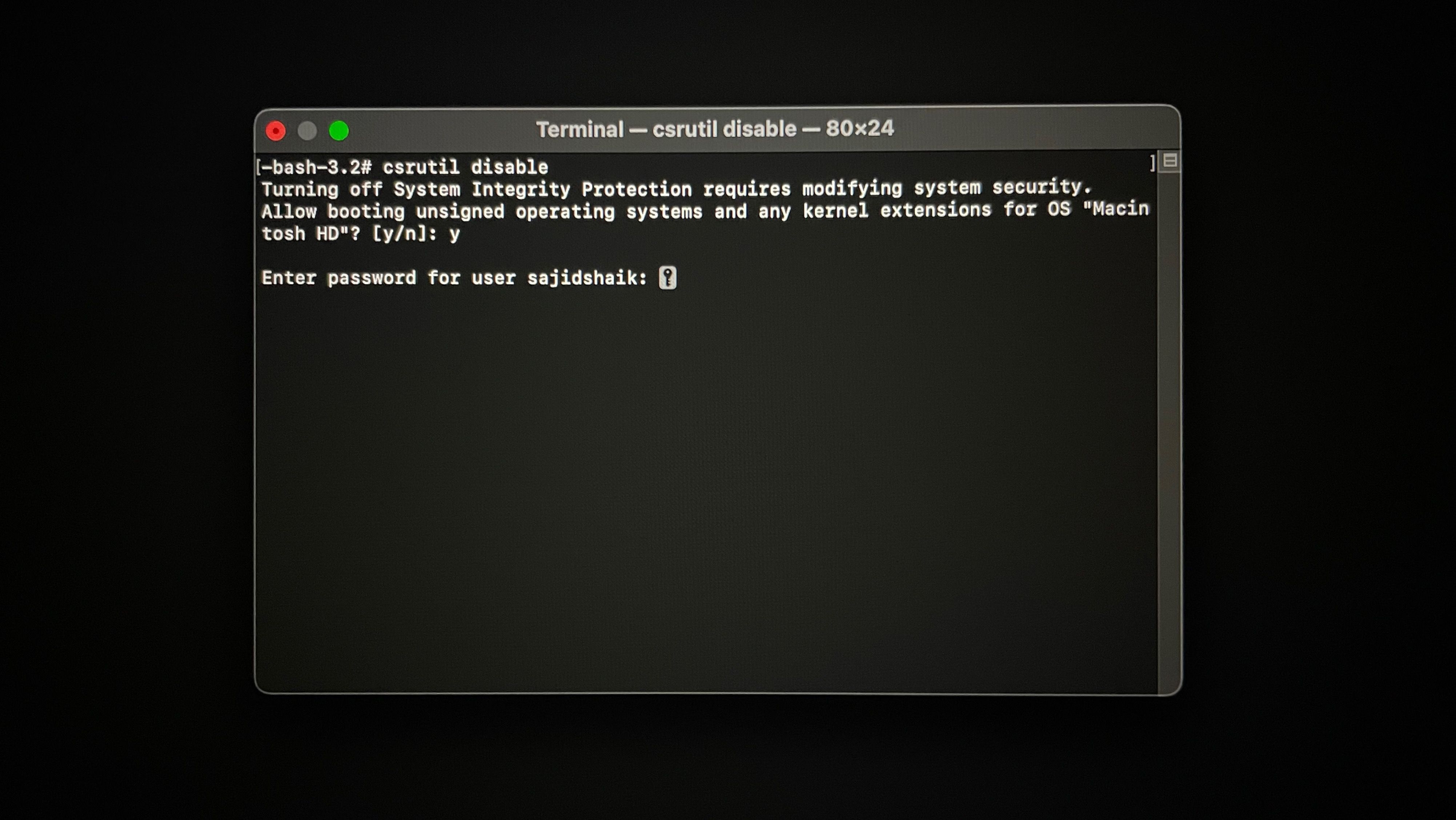
Type the following command and hit the Return key on your keyboard.
csrutil disable - Press Y on your keyboard and hit the Return key.
-
Enter your Mac's admin password if prompted, and press Return on your keyboard.
- Click the Apple logo in the menu bar and choose Restart to reboot your Mac.
Once restarted, System Integrity Protection (SIP) will be disabled, and you can install the app you previously couldn't.
You can always re-enable SIP by following the steps outlined above. But instead of typing csrutil disable, type the following code in Terminal and hit the Return key:
csrutil enable
Why Shouldn't You Disable SIP on Your Mac?
SIP is critical to the core functionality and security of a Mac, and temporarily disabling it is acceptable. We highly do not recommend permanently turning it off because your Mac will become vulnerable to viruses, malware, or ransomware risks.
Therefore, to maintain your Mac's security, disable SIP temporarily when necessary and re-enable it once your task is complete to protect your Mac from malware.
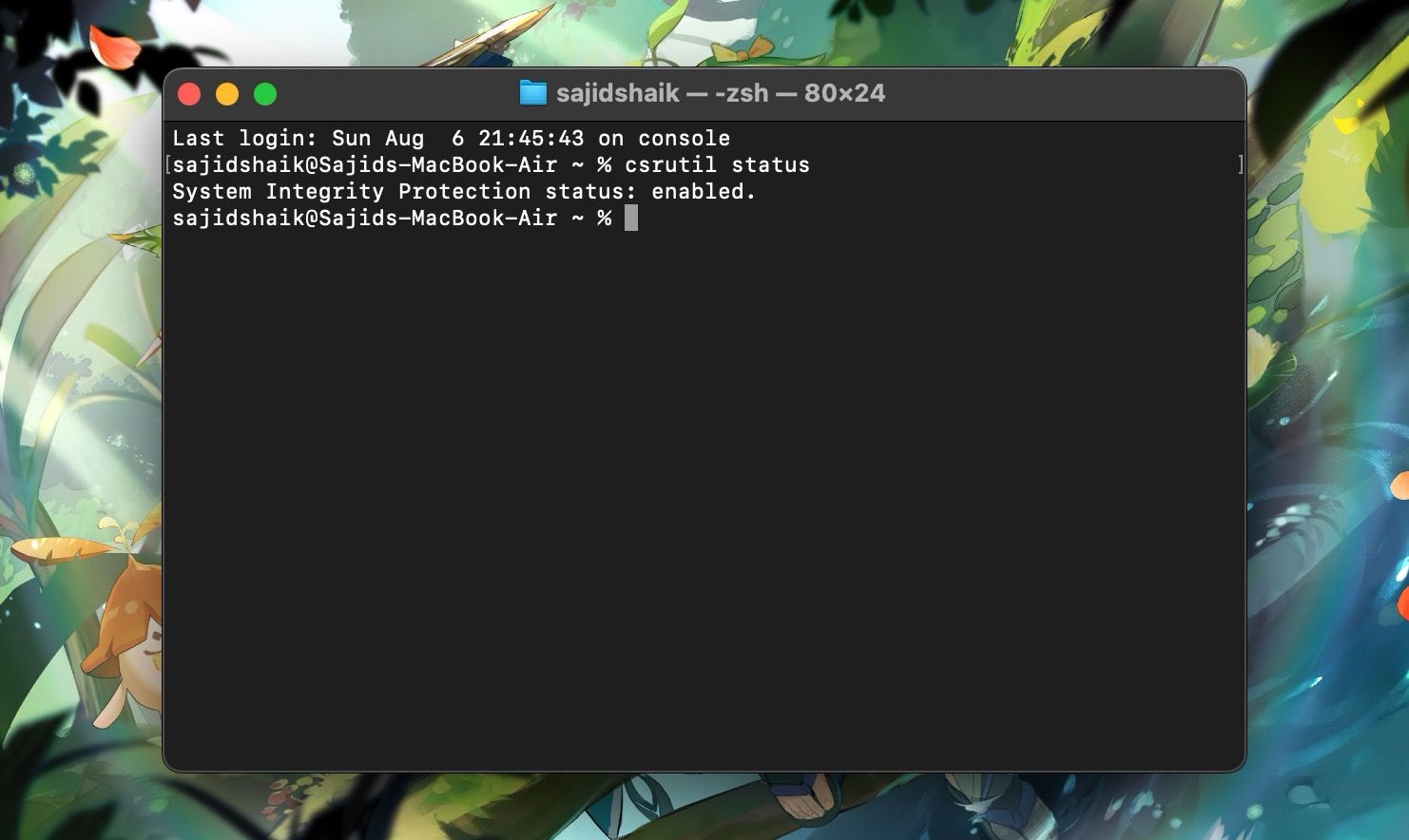
As a precautionary measure, you can check the status of your SIP on your Mac by opening Terminal, typing the following code, and then pressing the Return key.
csrutil status
If it says "enabled" next to System Integrity Protection status, it signifies that SIP is turned on, while "disabled" indicates SIP is turned off on your Mac.
Disabling SIP on Your Mac Is Quick and Easy
Although SIP is one of the essential security features built into macOS, Apple makes it fairly easy to turn it off when needed. And while we appreciate its presence, users may want to temporarily disable it at times to perform tasks like sideloading certain apps, data recovery, and more.