You've got anti-virus software on your PC, anti-malware scanner, a live scanner for picking up worms and other active intrusions, and a firewall. Your computer and its data are secure… right?
As we've seen more and more recently, having a secure PC setup is only one part of keeping your data secure. Connect to an unsecure router and all of your hard work is in vain.
Routers rarely arrive in a secure state, but even if you have taken the time to configure your wireless (or wired) router correctly, it can still prove to be the weak link in your computer security.
It's Like a Default: Securing Your New Router
Default options for routers are perhaps the biggest weakness. Like home security cameras that are streamed online, people tend to install-and-forget, overlooking the fact that virtually every model has the same username and password.
Brian Krebs reported recently that email spam has been used to hack routers by spoofing emails from telecoms providers, requesting the target click on a link and sending them to a page with hidden code that attempts to:
"…execute what’s known as a cross-site request forgery attack on known vulnerabilities in two types of routers, UT Starcom and TP-Link. The malicious page would then invoke hidden inline frames (also known as “iframes”) that try to log in to the administration page of the victim’s router using a list of known default credentials built into these devices."
A successful attack re-writes the router's DNS settings , sending the victim to spoof versions of sites that harvest logins.
Anyone installing a new router on their home network needs to take the time to clear all default usernames and passwords and replace them with their own, preferably secure and memorable passwords/pass-strings that are then changed on a regular basis.
The NAT-PMP Vulnerability
In late 2014 Matt Hughes reported that the NAT-PMP vulnerability affected something in the region of 1.2 million routers, with US security firm Rapid7 finding that "2.5% [of routers] vulnerable to an attacker intercepting internal traffic, 88% to an attacker intercepting outbound traffic, and 88% to a denial of service attack as a result of this vulnerability."
While the NAT gateway on routers should not accept internal data that is not destined to an internal address, devices that have incorrectly configured firmware unwittingly allow external computers to create rules, potentially leading to data leaks and identity theft.
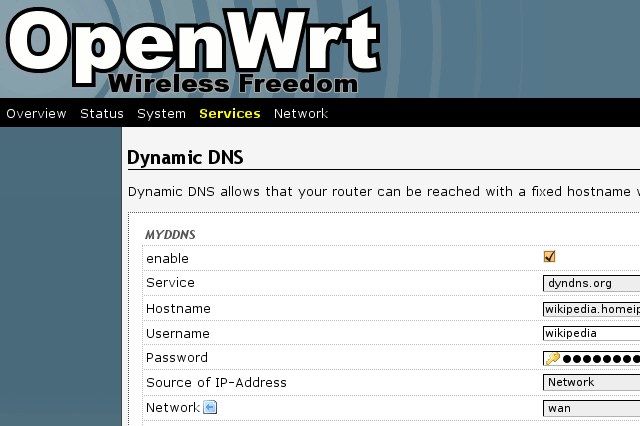
Fixing this issue requires that router manufacturers release patches. Alternatively, you might install a secure open source firmware, such as DD-WRT or Open-WRT.
Is Your WPA Router as Secure as You Think?
Anyone using WPA to secure their router would be forgiven for thinking that with the passcode entered (and regularly changed) that they were making a secure connection to the Internet.
Most modern Wi-Fi routers feature the WPS technology which bypasses WPA, and makes connecting to the router by means of a button or 8-digit PIN far easier.
Unfortunately with ease comes vulnerability. As reported by James Bruce, with a strong connection and a susceptible router, the WPS PIN can be brute forced in just 2 hours, and obtaining this PIN will reveal the WPA passcode to the attacker.
On some routers disabling the WPS PIN is an option, but this doesn't always do what it claims, instead disabling a user-defined PIN instead of the default option. Hardly ideal. The best solution in this case would be to disable wireless networking on your router, and wait for an update from your ISP or router manufacturer (check their website).
Is Your ISP To Blame?
Earlier in 2015 we learned that a particular model of Pirelli router was shipped to customers with a bug that is so easy to exploit your granny could do it.
As I reported:
"All you need to do is enter the web-facing IP address of a router, suffix it with wifisetup.html (so something like 1.2.3.4/wifisetup.html) and you can start playing around with the router configuration. Expert hackers would then be able to start setting up routes into the network, start sniffing Internet traffic, potentially even attack a computer with no firewall installed."
So far, this problem has been limited to that single Pirelli P.DGA4001N model, but it raises worrying questions about just how routers are being configured by the manufacturers.
Have you encountered problems with default settings on your router? Perhaps you have been affected by one or more of the problems highlighted here. What should router manufacturers and ISPs do to mitigate these issues? Tell us your thoughts in the comments.