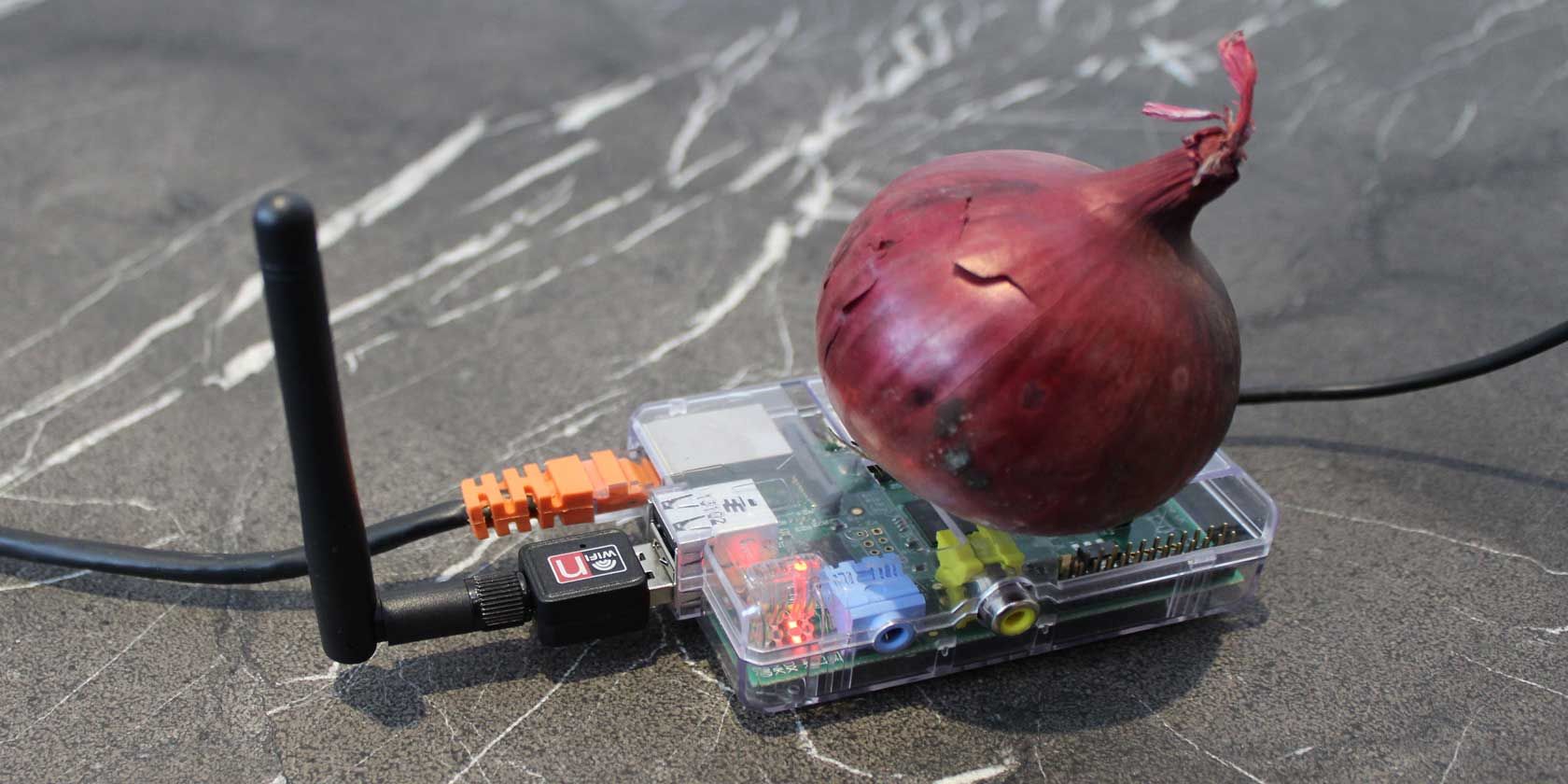
Safeplug is a special router that creates an anonymous Internet connection via Tor network (what is Tor?); it costs $50 - but you can make your own with a Raspberry Pi and USB WiFi dongle.
In truth, you won't be saving much: the cost of the Pi plus a suitable WiFi dongle will cost you about $50 or more. But DIY is fun, we'll learn lots in the process, and you probably already have a Pi sitting around collecting dust.
Shopping List
- Raspberry Pi (model B)
- SD Card of at least 4 gigabytes
- Ethernet cable
- Compatible USB Wifi adapter - this means able to work in structure mode with hostapd package (such as this one based on RT5370 chipset)
- Micro USB power adapter
The Theory
We'll adapt Raspberry Pi to act as a router: it'll plug into an Ethernet port on your existing Internet router just like any other device, but it'll also connect to the Tor anonymising network. You can read our complete guide to Tor to find out more, but essentially, it works by sending your Internet requests through multiple computers - bouncing it around the globe - making you virtually untraceable. The Pi will broadcast a WiFi network just like your router probably does, such that any traffic on the WiFi will be sent out to the Internet, via Tor. In fact, if you don't already have a WiFi-enabled router and want one - just follow the first half of this tutorial.
There is, of course, a reduction in speed to doing this, both through the routing element and the actual Tor network.
Be warned though: browsing through Tor alone won't completely anonymise your session. Your browser is full of cached files and cookies which can be used to identify your presence on a website (what is a cookie?). Make sure these are disabled, and blocked (use incognito mode) - and obviously don't start logging onto websites.
Getting Started
Burn a fresh copy of the latest Raspian Wheezy image to your SD card; plug in the power, Ethernet, USB WiFi adapter, and boot up. You don't need a monitor or keyboard plugged in - we'll be doing this all from the command line.
Use an IP scanner to figure out the IP address of your Raspberry Pi (IP Scanner for OS X works well for me), then SSH into it from a command prompt (how to use SSH in Windows) with the command:
ssh pi@x.x.x.x
where x.x.x.x is the IP address of your Pi. The default password is "raspberry"
Type:
sudo raspi-config
to run the graphical setup utility. Expand the filesystem, then exit the setup utility and restart. You should still have the same IP address - go ahead and SSH back in again.
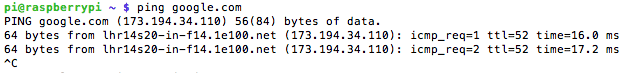
Check if the Pi can access the Internet by typing
ping google.com
from within your SSH session (not on your local machine). You should see something like this:
Hit CTRL-C to stop it. Now check your WiFi adapter is recognised by typing:
ifconfig -a
If you see wlan0 listed, all is good. If not, your wireless adapter isn't even recognised, let alone capable of structure/AP mode.
Let's update the system, and install some software. Run the following one by one, walking through prompts as needed. In the second step, we're removing the wolfram-engine to fix a math kernel bug - we also save 450 megabytes in the process.
sudo apt-get update
sudo apt-get remove wolfram-engine
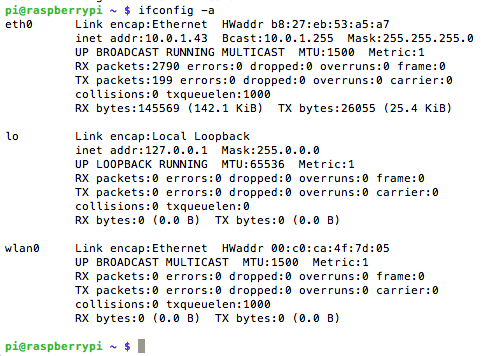
sudo apt-get install hostapd isc-dhcp-server
Here, we've installed a DHCP server so WiFi clients can automatically get an IP address. Ignore the error - this just means we haven't actually set it up yet.
sudo nano /etc/dhcp/dhcpd.conf
Comment out (add a # to start of them) the following lines:
option domain-name "example.org";
option domain-name-servers ns1.example.org, ns2.example.org;
Uncomment (remove the #) the word authoritative from these lines:
# If this DHCP server is the official DHCP server for the local
# network, the authoritative directive should be uncommented.
authoritative;
Now scroll right down the bottom and paste in:
subnet 192.168.42.0 netmask 255.255.255.0 {
range 192.168.42.10 192.168.42.50;
option broadcast-address 192.168.42.255;
option routers 192.168.42.1;
default-lease-time 600;
max-lease-time 7200;
option domain-name "local";
option domain-name-servers 8.8.8.8, 8.8.4.4;
}
Save with CTRL-X -> Y -> enter.
Next, type:
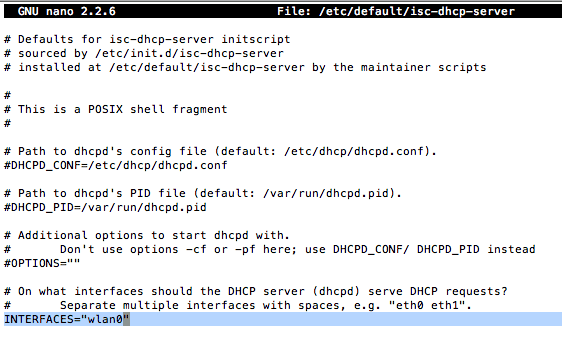
sudo nano /etc/default/isc-dhcp-server
Change the last line so it reads:
INTERFACES="wlan0"
Which means our DHCP server should listen on the wireless interface in order to give out IP addresses. Lastly:
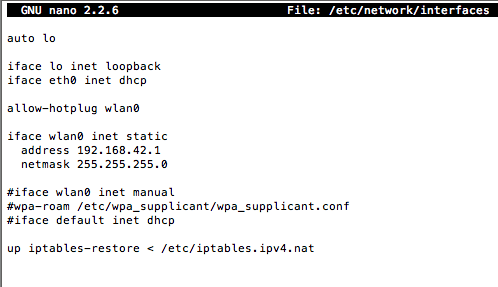
sudo nano /etc/network/interfaces
Replace everything after (leaving this line in):
allow-hotplug wlan0
With this:
iface wlan0 inet static
address 192.168.42.1
netmask 255.255.255.0
#iface wlan0 inet manual
#wpa-roam /etc/wpa_supplicant/wpa_supplicant.conf
#iface default inet dhcp
Exit and save (CTRL-X, Y, enter - remember that, I won't say it again!). We've now defined a static IP address for the wireless network, and we've told DHCP server to assign IP addresses to clients. Awesome. Next, type:
sudo ifconfig wlan0 192.168.42.1
To define our hotspot, edit the HostAP config file as follows.
sudo nano /etc/hostapd/hostapd.conf
Add the following lines, editing the ssid (WiFi network name) and wpa_passphrase if you wish.
interface=wlan0
driver=nl80211
ssid=PiTest
hw_mode=g
channel=6
macaddr_acl=0
auth_algs=1
ignore_broadcast_ssid=0
wpa=2
wpa_passphrase=raspberry
wpa_key_mgmt=WPA-PSK
wpa_pairwise=TKIP
rsn_pairwise=CCMP
Now we need to tell the Pi where our config file is.
sudo nano /etc/default/hostapd
Replace this line:
#DAEMON_CONF=""
with:
DAEMON_CONF="/etc/hostapd/hostapd.conf"
Finally, we need to configure NAT. NAT, or Network Address Translation, is the process of changing internal network IP addresses into a single external IP, and routing things around appropriately.
sudo nano /etc/sysctl.conf
At the very bottom, add:
net.ipv4.ip_forward=1
Save. Run all the following commands - feel free to paste them all at once. Here we're establishing routing tables that basically just connect our ethernet and WiFi adapter.
sudo sh -c "echo 1 > /proc/sys/net/ipv4/ip_forward"
sudo iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE
sudo iptables -A FORWARD -i eth0 -o wlan0 -m state --state RELATED,ESTABLISHED -j ACCEPT
sudo iptables -A FORWARD -i wlan0 -o eth0 -j ACCEPT
sudo sh -c "iptables-save > /etc/iptables.ipv4.nat"
Finally, run:
sudo nano /etc/network/interfaces
and add:
up iptables-restore < /etc/iptables.ipv4.nat
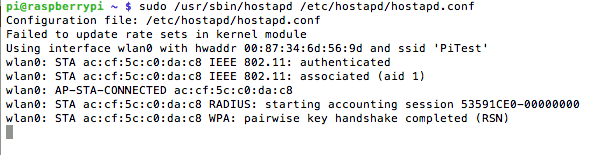
to the very end. To test, we run:
sudo /usr/sbin/hostapd /etc/hostapd/hostapd.conf
Your PiTest network should be broadcasting now, assuming you didn't change the name. Try to connect from another machine or mobile device and you should see some debug information displayed on the screen, like this:
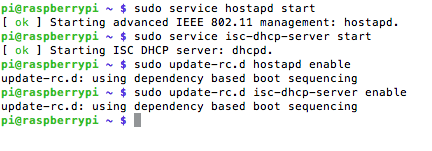
Now, hit CTRL-C to cancel the program, and let's make sure this runs as a service on restart. Run these commands:
sudo service hostapd start
sudo service isc-dhcp-server start
sudo update-rc.d hostapd enable
sudo update-rc.d isc-dhcp-server enable
Now we've got the routing part setup, but we still need to add Tor to the equation - right now, we've literally just made a router.
Install Tor
sudo apt-get install tor
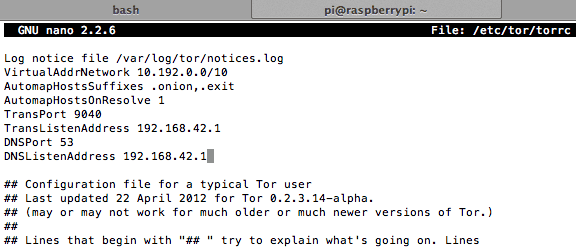
sudo nano /etc/tor/torrc
Copy and paste this right at the top. Ignore everything else, and save:
Log notice file /var/log/tor/notices.log
VirtualAddrNetwork 10.192.0.0/10
AutomapHostsSuffixes .onion,.exit
AutomapHostsOnResolve 1
TransPort 9040
TransListenAddress 192.168.42.1
DNSPort 53
DNSListenAddress 192.168.42.1
Get rid of our old routing tables and add an exception for SSH so we can still log back in. We're adding a passthrough for DNS lookups; and directing all TCP traffic (control signals) to 9040.
sudo iptables -F
sudo iptables -t nat -F
sudo iptables -t nat -A PREROUTING -i wlan0 -p tcp --dport 22 -j REDIRECT --to-ports 22
sudo iptables -t nat -A PREROUTING -i wlan0 -p udp --dport 53 -j REDIRECT --to-ports 53
sudo iptables -t nat -A PREROUTING -i wlan0 -p tcp --syn -j REDIRECT --to-ports 9040
You can check the entries like so:
sudo iptables -t nat -L
Save the file so it's loaded on reboot.
sudo sh -c "iptables-save > /etc/iptables.ipv4.nat"
Enable it to start at boot, then restart so we can test it.
sudo update-rc.d tor enable
sudo shutdown -r now
You can create a log file and tail it using the following (these aren't necessary, but may be useful for debugging if you're having issues).
sudo touch /var/log/tor/notices.log
sudo chown debian-tor /var/log/tor/notices.log
sudo chmod 644 /var/log/tor/notices.log
tail -f /var/log/tor/notices.log
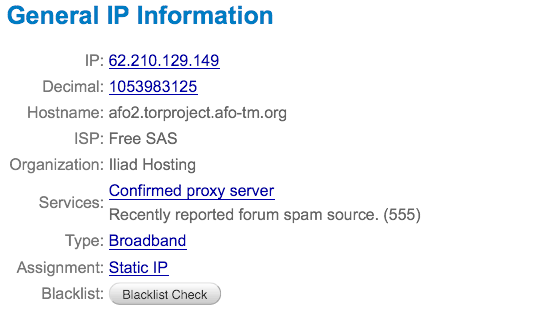
Head over to whatismyipaddress.com to verify your IP isn't from your own ISP:
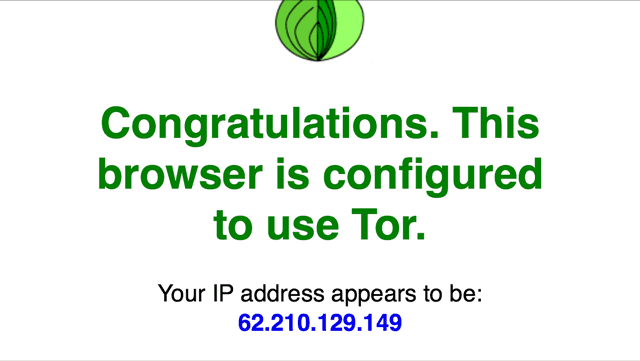
Or use check.torproject.org:
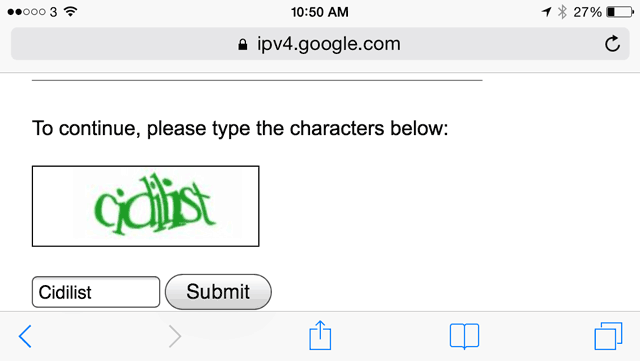
You may find Google is asking to verify with a Captcha quite often - this is because Tor is often used by spammers, and there's not much you can do about it.
Congratulations, you are anonymised and can now access hidden Tor websites with the .onion domain (How to find active Onion sites?). Just don't do anything silly, like start a website selling drugs for Bitcoins, or use your real name anywhere, and you should be fine. Let us know if you have problems and I'll try to help.