As tablets become more popular, they’re serving as stand-ins for computers for some users. Although most people still own a PC, tablets are particularly nice for web browsing and online video, making them common couch-side companions.
This, however, could introduce some issues. If tablets are being used like computers, they could be exposed to the same threats. Which begs the question - how can you deal with Internet security on your Android tablet?
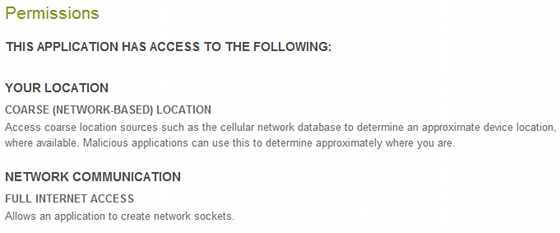
Permissions - Like The Phones
The entry to understanding Android on any device is permissions, and in this respect Android tablets work much like the phones. Heck, this same system isn’t even Android exclusive - Google has already adapted the same idea to Chrome extensions and web apps.
Permissions are very simple. Before you download an app, you are given a list of permissions that app requests of your device. These are not optional - if you download the app, you are agreeing to the permissions. Once permission is given, it can’t be revoked unless you uninstall the app.
You therefore need to be very careful about what you download. Reading permissions can seem annoying - but do it anyway. An app that is malicious can easily get up to mischief without you knowing, and while such instances in the real world remain limited, they do exist.
Downloading An Antivirus App Is A Good Idea
As I point out in virtually every Android Internet security article, antivirus apps for the platform remain a bit of an open question. Comprehensive, objective tests of their ability to defend again threats remain rare.
However, a recent A/V Comparatives study did show that most security apps were able to protect against a test selection of malware threats, and the study goes so far as to recommend that all Android users install antivirus software.
Which one should you download? I’m a fan of Kaspersky’s Tablet Security, and recommend it as a first choice, but does require a pricey $20/year subscription. That may seem like a lot, and if you want free, Lookout Mobile Security can work well - but keep in mind that the app’s $2.99/month premium option totals to almost $36/year.
Treat It Like A Laptop
When it comes to network security, tablets are much like laptops. They almost always connect to the Internet via Wi-Fi, and are subject to all the security risks that results from that. Fortunately, your Android tablet supports secured wireless connections, and that’s a feature you should always use whenever possible. The issue which is of concern is the chance that a hacker will be able to obtain your browsing data if you use an unsecure connection, and it applies to tablets just as with laptops.
One useful feature is Android’s built-in VPN support, which you’ll find in your tablet’s settings. Just enter the VPN address and your username/password for it, and you’re off! You can use this with many VPN services to provide yourself with secure browsing over unsecured networks.
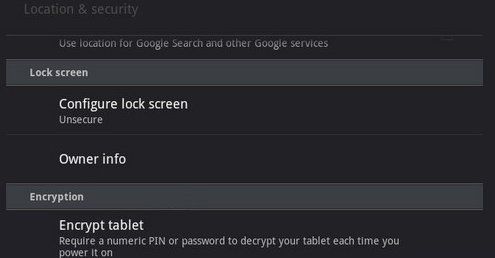
Use Honeycomb’s Encryption
Android has not been particularly popular with enterprise users because of a general lack of focus on enterprise security, but there has been some inroads made in that direction, one of which is the encryption feature on Honeycomb tablets.
The feature is found in the Location & Security section of Honeycomb’s settings, and can encrypt the contents of your tablet’s memory. Doing this does not make it unhackable, nor does it mean that someone couldn’t intercept your Wi-Fi transmissions, but it does means it will be difficult for anyone to steal your data if the tablet is lost or stolen.
If you do encrypt your tablet, remember that you also won’t be able to access the tablet’s data if you are locked out of your tablet. Backing up important files is, as always, a good idea.
Conclusion
Security for tablets is far from mature, just as the threats that may exploit a tablet are far from mature. There is some degree of security via obscurity available as of now, as many website exploits and viruses simply won’t work against tablets. That’s not going to last forever though. Security threats will become more and more common as the devices themselves become more and more popular. This process will take many years, but hey - it certainly doesn’t hurt to have a head start.