They're constantly on the prowl: cold calling scammers claiming to be from "Windows Tech Support", who in reality have the nefarious aim of downloading spyware and/or charging you for their assistance while they are remotely connected (or, worse still, both).
It's one of the biggest cons around, and it still goes on. But how does the Windows tech support scam work? To find out, I waited for the call...
Receiving the Windows Tech Support Call
I actually received two calls from the "Windows Tech Support" scammers.
The first, just after lunch, caught me by surprise. Snowed under with work, I laconically burst out laughing at the news that my computer “could crash at any time.”
The laughing didn't stop until the caller hung up. Sadly, they didn't get the hint.
Six hours later came another call. Perhaps the same lady, I don't know as I didn't take the first caller's name. This one, despite her strong Indian accent, was called Rachel.
Of course, this is part of the tactic, to present a "civilized" veneer of legitimacy for what is, surely at the back of most people's mind, a surprising call.
Because the call itself is incredible. It suggests, through the script that the cold calling scammers stick to very closely, that Microsoft can detect if your computer has an "infection".
They're clear on this too; this isn't a call about viruses, as your computer's antivirus software can handle those. No, this is all about "infections", some loose reference to malware.
Which, incidentally, is what they're peddling.
The Charming Windows Tech Support "Expert"
Now, I just happened to be rolling three computers on the day of the call. My usual Surface Pro, a Raspberry Pi, and my Toshiba laptop which I had just installed Linux Mint on. This scam is designed to be used on Windows computers only, and as you may well know, Linux security issues and viruses are rare.
You can probably see where this is going…
With Linux Mint booted up right in front of me, I couldn't help myself but make an example of these people. So I explained to "Rachel" how I was unable to follow her instruction to make the Run box appear. Pressing the Windows key and R had no effect.
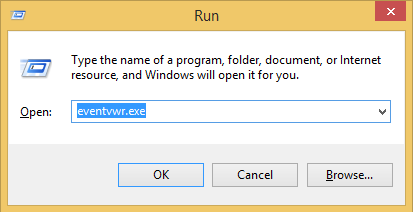
Opening the Run box is a key strategy of the scam. It is intended to show you "errors" in the Security view log in Windows Event Viewer, a useful troubleshooting tool in Windows.
As with any scam, there is a believable aspect to this. Opening Event Viewer > Custom Views > Administrative Events does indeed reveal some serious-looking warnings. The red circles, exclamation marks, and “Error” labels--not to mention yellow “Warning” triangles--look serious.
The scammers present these as infections, but of course, they’re simply log entries.
They want to charge you for removing log entries.
Variations of the Windows Tech Support Scam
Other versions of the scam target different Windows features that may cause alarm to anyone without in-depth knowledge.
- Unusually system files are opened in Notepad to demonstrate “corruption”
- System services disabled by default on Windows described as a problem
- Command prompt trickery resulting in a malware-related “error message” (programmed by the scammer)
- Claiming Windows Registry keys are dangerous
- Windows product keys or other licenses are claimed to be out of date
- System files regularly subverted or replaced by malware are “shown” to be malicious by referring the victim to legitimate computer security sites describing the vulnerability
Payment for “solving” these “issues” is typically through untraceable gift cards. Refuse to pay, and they lock or otherwise disable your computer.
My Chat With the Windows Tech Support Scammer
Being unable to open Run and enter the eventvwr.exe command (neither are Linux features), I was passed onto "Jonathan"…
As you can hear in this recording, the "expert" I was passed to continues the script with more authority.
Presumably, the initial caller's pleasant voice is intended to "soften up" the victims.
Windows Tech Support Scam Victims
Yes, victims, because that is what we are. Whether we're scammed or successfully spot this nonsense before it escalates, anyone subjected to the scam is a targeted victim.
Eventually, after the Run box failed to open "Jonathan" asked me to visit a website, support24.6te.net.
For obvious reasons we're not linking to it, but checking the WhoIs result reveals it resides on a free web host. Inspection of the webpage reveals an unsophisticated single HTML file with embedded CSS.
Not exactly a professional outfit; rather the classic signs of a scam.
The next step, whether the Run box can be opened or not, is to install software called AMMYY (who claim to be aware that their software is being misused in this way, and show up in many places as an untrusted service). This is a TeamViewer-style remote desktop app, favored by this sort of scam, which allows them access to your computer.
What Do the Windows Tech Support Scammers Want?
At this point, the scam comes alive, as "infections" are found, and you're charged for their removal. Meanwhile, keyloggers and spyware can be installed by the scammers.
The results of this can be devastating. Information relating to personal online accounts (banks, shopping, email, etc.) can be recorded with keyloggers. Spyware can activate cameras, microphones, and record your desktop.
These scammers are organized and dangerous. Hundreds, if not thousands of calls are made every minute in what can only be described as an industrial-level fraud, operating mostly out of Indian call centers.
One expert (using the pseudonym “Jim Browning”) traced scammers back to their base of operations.
Now, I took "Jonathan" as far as I could before ultimately getting bored. I'd wasted around 25 minutes of their time before making my Linux reveal at the end.
But you shouldn’t do that. The moment you hear that someone calling you out of the blue is attempting to repair your PC, hang-up. Even if you *have* requested some telephone support from your PC vendor or work IT, verify their identity before proceeding.
What You Should Do If Caught Out By the Scam
If you've landed here having been taken in by this scam, then you need to act quickly.
- Disconnect your computer from the internet
- Run an anti-malware scan (Windows Defender should be adequate)
- Cancel/lock your credit cards
- If money has been taken, this is fraud, so report it for a refund
- Once you’re back online (and the malware removed) all email and website passwords
- Let people know that the scam is targeting your region (scammers tend to focus on telephone area codes)
- Inform the FTC of the telephone scam
The scam is indiscriminate, targeting homes and businesses alike.
Beware Windows Tech Support Scam Calls
This scam has been operating for over a decade. Law enforcement agencies are aware of it; Microsoft and Google have taken action on it (particularly to remove ads for the web-only variation) but it still occurs.
If you suspect any caller is a scammer, hang up. In most cases they will move onto the next number on your list. Don’t do what I did and waste their time; these operations are industrial in scope. While you might save one person from being scammed, thousands of others are potentially being fooled.
Instead, report the call to the FTC. The bases of these scams are raided from time to time, but the evidence you provide is required.