There are times when I'm in a public place and there are actually a multitude of Wi-Fi networks freely available. If you've ever been in that situation, and if you're like most people, you just quickly grab the first network you see available.
The problem is that sometimes, even though the signal strength looks okay, the network quality isn't actually that good at all. You end up dropping the connection and being forced to try a few others until you find one that really works.
Here at MUO, we've offered a number of good tools to analyze Wi-Fi networks. Jack wrote up a good description of HeatMapper, an app that shows you the Wi-Fi strength in different areas of your home. Guy showed you how to use Xirrus to troubleshoot network issues.
These are both valuable tools, but I recently discovered another amazing Wi-Fi analysis tool that just blew me away and I knew I had to share it with MUO readers. The tool has been reviewed at a number of other tech blogs, so many of you might have heard of it. For those of you that haven't, I'd like to introduce you to inSSIDer 2.0.
Analyze WiFi networks With inSSIDer
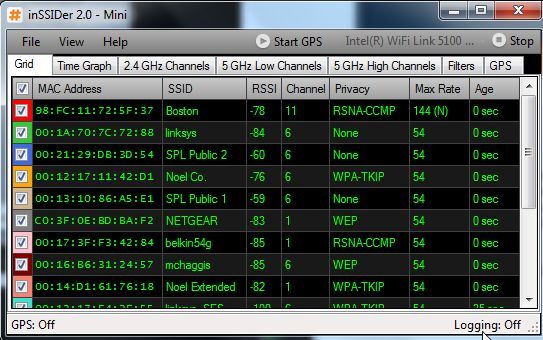
I have to admit that I'm not a huge fan of network analysis tools. I only recently became interested in Wi-Fi tools when I found myself spending a lot more time at public hotspots and struggling to locate a strong Internet access point. inSSIDer provides one of the clearest pictures of every Wi-Fi network within your range. It gives an amazing list of detailed information about each network. Best of all, it works with your regular Wi-Fi adapter, no special hardware required.
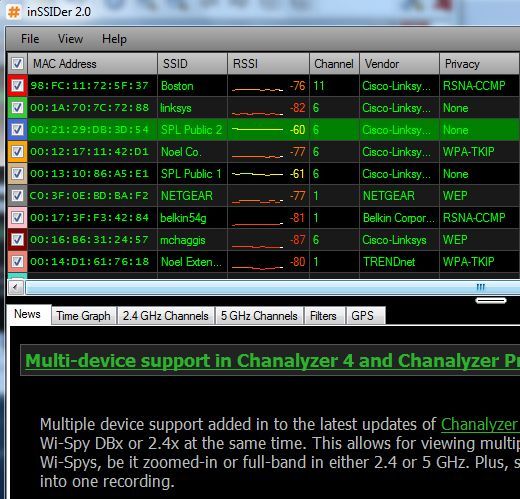
As you can see above, you get the Mac address of the device, the network name of the router, the signal strength, channel, the router manufacturer and privacy settings (if any). Beyond that, it'll also show you the latest network activity, and even the GPS coordinates of the router if you've configured a GPS device on your PC.
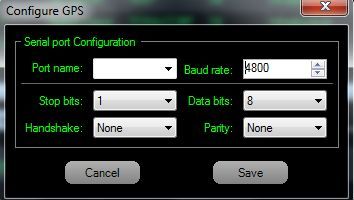
Configuring the device to talk to the software is as simple as plugging in your PC-compatible GPS unit and configuring the serial port settings in inSSIDer to match the device.
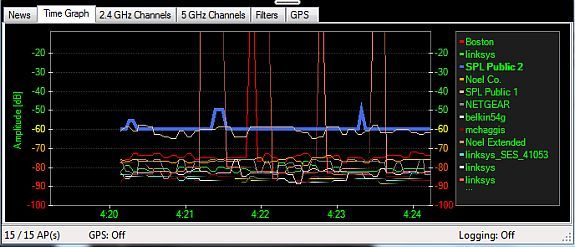
A lot of other Wi-Fi analysis tools offer realtime graphs of signal strength over time, but the one offered by inSSIDer really does appear to be pretty accurate compared to others. You can view these for all channels or for select channels.
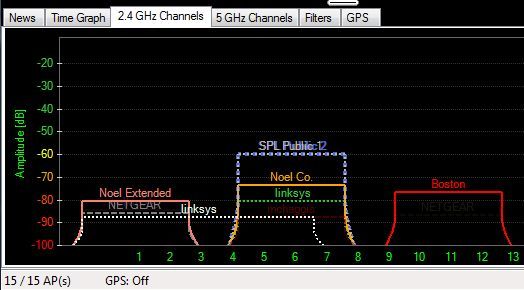
You can also see a graphical representation of current signal strength per device. This is a useful way to quickly get a glimpse of which device offers the strongest signal at your location. If you're using a laptop, you could theoretically walk around and probably locate the device using this screen.
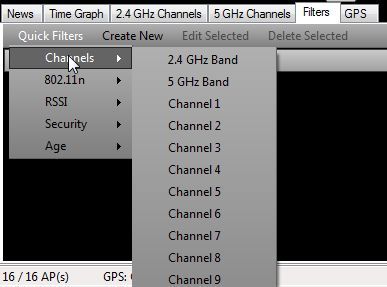
Another nice feature is the ability to filter out displayed devices by certain characteristics, like security type, vendor or a number of other parameters.
If you really don't want to go through the process of creating a filter statement from scratch, there's also the option to use the "Quick Filters" which let you select from a list of pre-programmed filters. This is the fastest approach if there's only one parameter that you want use to filter.
If you are using inSSIDer as a quick method to constantly monitor local networks, and you don't want to to take over the whole screen, you can click on "View" and switch into "mini" mode. This collapses the window to a much smaller form and combines the display and the tabs into a quick-access window that you can move to the corner of your screen.
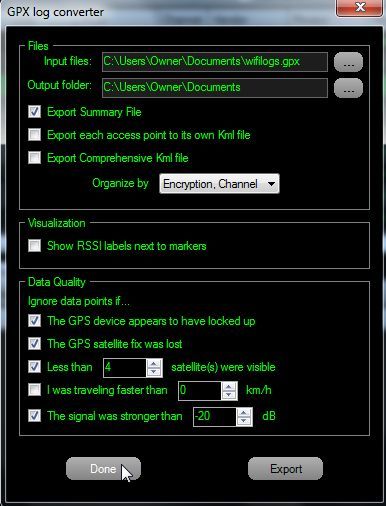
You'll notice, at the top of the screen there's a link to "Start GPS." Again, you'll need a GPS device enabled on your PC or laptop, but if you do, you can actually log network activity and export the data out to a GPX file which shows the locations of all access points on any GPS device that can import GPX data. Or if you prefer to export the access point GPS coordinates to Google Earth or other tools that can read KML files, use the built-in GPX to KML converter.
There really is no easier way to map out multiple Wi-Fi networks or a mix of access points. Instead of using heat mapping software and manually trying to trace out the location of access points based on those maps, just enable GPS in inSSIDer and let the software do all of the mapping for you automatically.
Have you ever tried inSSIDer yourself? Please let us know what you think of the software or other ways to use it, or any features that we might have missed in the comments section below.