The wider the internet gets, the more important it is to secure and monitor your children's behavior online—whether it's in school or on your home network. There are out-of-the-box parental controls installed in most devices, as well as a plethora of third-party applications we can use to track and protect them.
But children are smart and naturally tech-savvy; just because the control settings are in place, doesn't mean the kids won't find ways to bypass it. Here are seven ways your children might bypass parental control software.
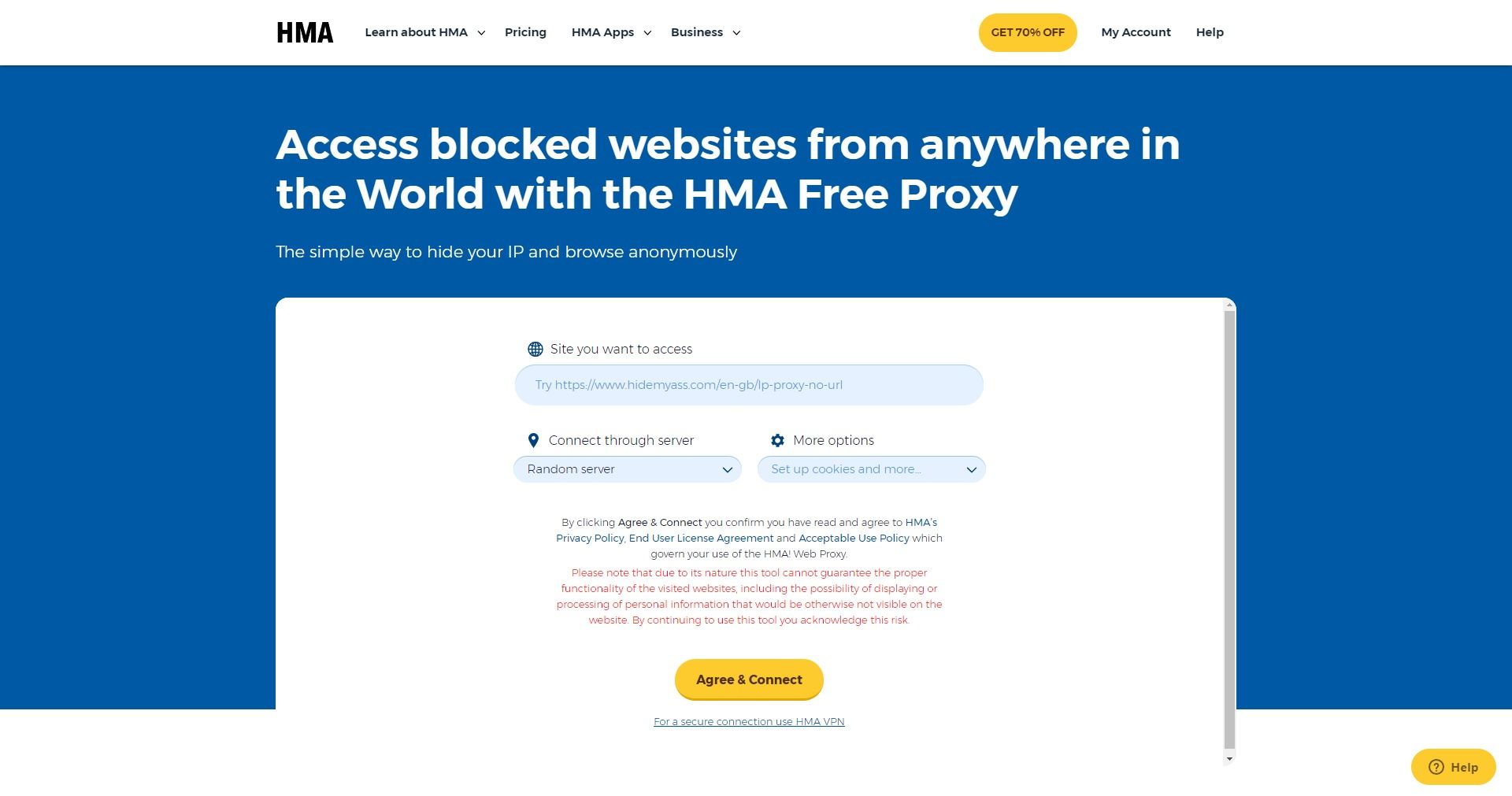
1. Proxy Sites
Proxy sites divert traffic via an innocent address, unobstructed by any filters. This means instead of your child attempting to visit "horrificfilthyNSFWcontent.com" directly, they'll head to a site such as hide.me, and simply tap the restricted address into the site search bar.
The proxy site takes care of business, routing the request to an external server which in turn retrieves the content on the user's behalf.
Most traffic filtering software can't trace the communication between the proxy site and the external server, but the proxy site itself will be listed in a filter. Many filters actually block the most popular proxy sites for exactly this reason. However, this can have other, unintended effects.
There are thousands of free proxy sites online. All it takes is a dedicated child with a free afternoon to go through them one by one to find one they can access. And while the majority of proxy sites are legitimate and offer the free option to promote their paid service, some aren't.
All it takes is a click on the wrong site to lead to a massively irritating cleanup. Or worse, a full-blown malware that infects your device.
2. Changing or Brute-Forcing Passwords
An extremely common method of bypassing parental controls is by simply changing the password. If your children know that you use a specific password on certain accounts, they can alter settings to their own choosing without alerting anyone.
This issue is particularly prevalent among older, tech-savvy kids. There are countless ways they can get their hands on the password. For instance, they can use social engineering to get you to send them the password through a fake security email. Or maybe you leave your primary email open with no password protection, allowing them to reset the password.
Actual phishing schemes are easier to detect because scammers don't know the model of your first car or your great aunt's middle name, but your sure kids do.
It's really unlikely, but your child might also brute force your password. If your child knows about and can make use of the powerful tools used for password cracking, you might have other info-sec issues taking place under your roof too.
3. Different Wi-Fi
How well do you know your next-door neighbors? You must know their names. Maybe their birthdays, names of pets, and a contact number for emergencies. How about their Wi-Fi password?
Okay, so this is becoming increasingly normal, especially if you are indeed friendly with your neighbors. But families living within a reasonable proximity to one another are likely to experience some Wi-Fi broadcast overlap. This means their SSID is viewable from your home. If their network security isn't up to scratch, your child could easily log onto their unsecured network to access whatever content they desire.
It might not even be a case of lackadaisical Internet security, either. If your kids rampage in a cohort with the neighborhood kids, it could be as easy as asking one of the older children what their Wi-Fi password is. If it has been altered from an alphanumeric code to something "easy to remember", it'll be even easier to pass forward.
4. VPNs
It isn't just adults escaping regional Netflix restrictions using a Virtual Private Network (VPN). Just as with proxy sites, you'll find numerous discreet, free VPN solutions prepared to encrypt your children's search entries and the route between their PC and the company servers.
Free VPN solutions usually come with caveats such as speed restrictions, data logging, or a download cap, somewhat limiting the scope of achievable activities. That said, it's feasible they could switch between several VPNs installed on their system to mitigate download caps and speed restrictions. As well as this, it really is quite difficult to spot someone using a VPN with a cursory over-the-shoulder glance.
If they are using a VPN, detecting their bypassing of parental filters will be extremely difficult. Your router will not show a new, alien IP address. Not to mention, your broadband provider will have no access to the content delivered. Some VPNs do log the user data, for law enforcement and marketing purposes, but they are still unlikely to share the details of your children's VPN searches with you.
5. Portable Browsers
The days of people using Internet Explorer by default are long-gone. Many browsers are fast and secure, with several extra features.
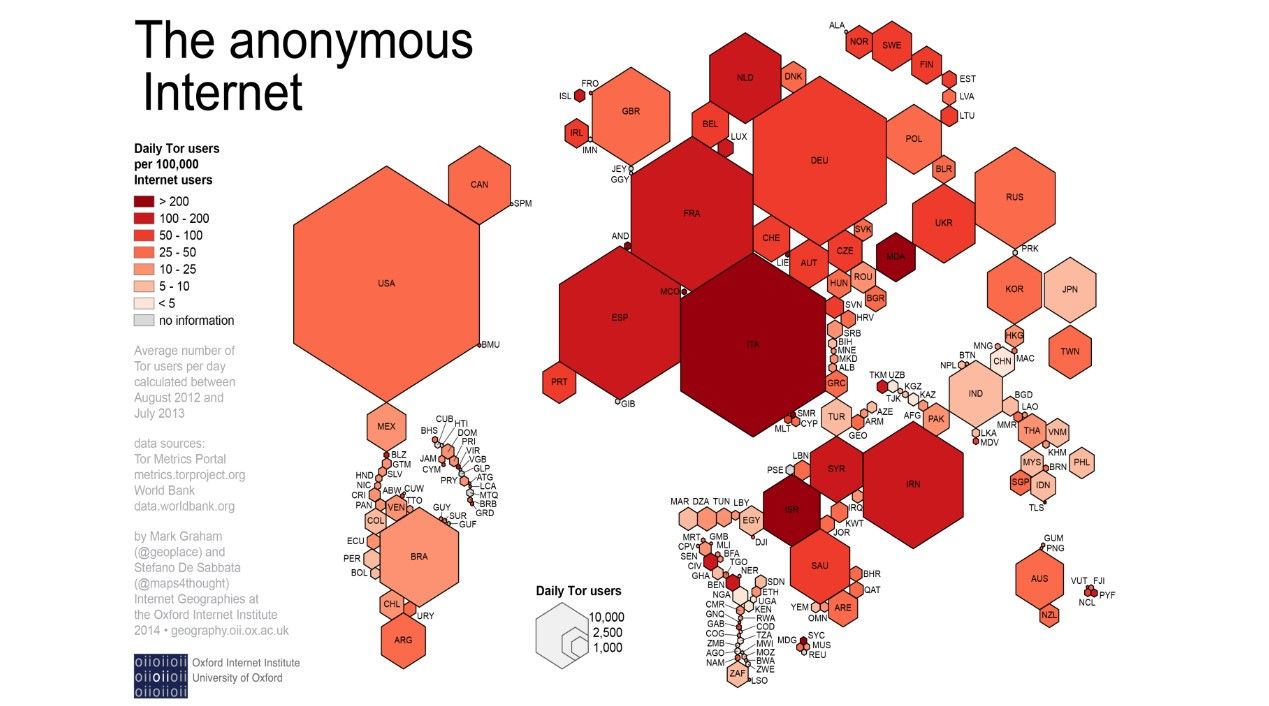
Most people know about browser InPrivate or Incognito modes, including the kids young and old. Safe search filtering tools still catch blacklisted URLs, even when using private mode. Particularly savvy teenagers may have brushed up on their personal security homework, and be aware of the TOR Browser, which can easily be installed and deployed from a USB stick.
The TOR Browser reroutes web traffic through different international locations, consisting of more than 7,000 individual relays. This multi-layered routing makes it nearly impossible to ascertain what content a user is viewing while using the browser. Its inbuilt focus on privacy and anonymity is an excellent prospect for bypassing your filters.
6. "Accidental" Image Viewing
A slightly trivial "bypass" method, but I'm sure many children have stumbled upon this. Incognito and InPrivate mode browsing tabs still adhere to most safe search filters, dutifully blocking content and relaying the details to concerned parents.
While search engines are working on hiding sensitive images from search results, the right combination of search words can sometimes result in a handful of images slipping through if they select the "Image" tab. Major search engine providers host and cache content on their own servers, meaning when the search is entered, there is no specific URL to filter, and numerous related images will be displayed.
7. Google Translate Proxy
This is another bypass method we would expect some children to be aware of. If a URL is blocked, they can use Google Translate as a makeshift proxy. It is as easy as setting a language you do not speak in the text input field, entering the URL you wish to access, and waiting for Google to automatically translate it.
The "translated" URL will become its own link under Google instead of the original website. The site will open in full, albeit within Google Translate. This can be slightly slow, but it is unlikely to be slow enough to discourage a determined mind.
What Can You Do?
It's difficult mitigating against an inquisitive mind with access to all the information the world has, at the click of a button. Simply put, if they are determined, they'll get access to it. And if it isn't on your home Internet, it'll be on a friend's or on an unsecured network somewhere else.
Upgrade Your Toolkit
Built-in settings and simple tools are easy to bypass, so why not use something made to keep up with your kids and their online behavior. Google Family Link allows you to track and view their activity—how much time they're spending on which apps and websites. It also lets you prevent them from installing certain apps altogether.
But instead of going the ban route, Family Link is designed to give your kids healthy alternatives to banned websites and apps. You can even get their teachers and schools involved and have them recommend educational and entertaining apps and websites through Google Family.
Most importantly, limiting kids time on their personal devices is the best way to have them prioritize their online activity. Whether it's a set time per day or an active window that ends at their bedtime, it's best to eliminate the problem from the source; online boredom.
Educate Them and Yourself
Younger children will likely crumble when faced with active filtering; teenagers are much more like to take up arms and engage in battle. If they keep gaining access to restricted content, it's best to keep a direct line of communication with them so they don't find themselves in big trouble.
In this, education is a massive tool. Respectable and acceptable use of the Internet should form a core part of your children's technological development. Past a certain age, there are likely other things you really should be discussing with them too, especially given the glorification of hacking in entertainment, giving rise to the popularity of hacking among kids and teens.
Prohibition has never solved a problem but has certainly created plenty more, and curious minds will remain so—just without the education to go alongside it.
Device usage and access should also be considered. Do young children need the latest iPhone or is a simple tablet enough? Giving them something without a SIM card can stop them from signing up for apps and websites that require a phone number without your direct permission.
Similarly, you could enforce an "Internet use in family areas only" rule, or bar tablets, laptops, and smartphones from the bedroom at night. If your kids do use an iPhone, however, find out how you can use family sharing to monitor their activities.
Don't Make Internet Safety a Prison
It doesn't have to be an awful experience, but by taking an active, engaging, and realistic attitude toward your children's Internet use, they'll be far more likely to understand and respect your wishes. And if you need a little more help with various devices, take a look at how you can use Chromebook parental control apps.


.jpg)