Thankfully, the celebrity photo leaks of the past few months seem to have passed. This event — referred to as The Fappening, Celebgate, and a variety of other names — saw some 500 indecent photos of celebrities, including Jennifer Lawrence, Mary Elizabeth Winstead, and Kaley Cuoco, leaked to the public online.
This form of invasion could have happened to anybody, and it probably has at some point — you just don't hear it reported when only a few commoners are affected. Hopefully you'll never have to experience such an embarrassing event; if you follow these tips, you won't.
Watch What You Save In The First Place
There's been a lot of debate about this, and the intention here is not to blame victims. However, it's important to remember that if there are no nude pictures (or any other sorts of incriminating files) on your phone in the first place, they can't be stolen by others. Even with a secure messaging app, you have no guarantee of protection. When using Snapchat, the disposable picture messenger, for example, all the recipient of an illicit photo has to do is take a screenshot; then who knows where it will spread?
To that end, be careful what's on your devices. If you must keep anything potentially embarrassing, be sure to encrypt them on your phone; Chris has given four reasons why encryption is a good idea should you need more convincing.
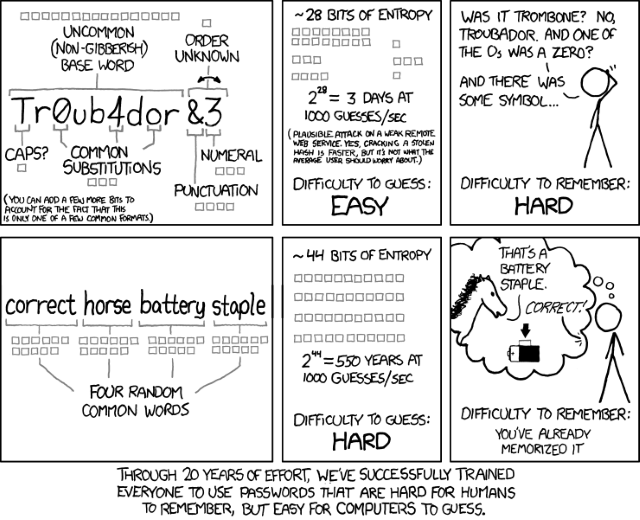
Keep Strong Passwords And Tight Access
Initially, iCloud was blamed for the photo leaks, but it was later decided that the attack was targeted on usernames, passwords, and security questions. This tells us that the service where the pictures were stored was not to blame, but that the perpetrator was likely able to break into accounts. Therefore, it's important to make your passwords as air-tight as possible.
If you need some advice on bulking up your passwords, we've compared methods of managing passwords; LastPass is an awesome tool to simplify the password process, or if you prefer the old-fashioned way be sure to follow tips to create a memorable yet strong password.
While we're on the subject of passwords, it's important to make sure that you keep them to yourself. If you wouldn't trust someone with your credit card number, don't share passwords with them. Obviously your spouse is a special case, but those should be rare.
If you've passed around this personal information before, do yourself a favor and change your passwords. You don't need to be hyper-sensitive and change them once a week or anything, but it's a good idea if you've been lax in the past.
Take Advantage Of Two-Factor Authentication
Two-factor authentication adds an additional layer of security to any account that supports it. In addition to your password (something you know), to gain access to your account someone must have a code from your phone (something you have). It isn't 100% bulletproof, and it might seem inconvenient at first, but the added security it brings is well worth any small hassle. Should a person with malicious intent crack your password, they'll still be locked out without a code.
We've written about the most critical services to enable two-factor authentication on, and recommend using Authy as your primary code-generating app. Finally, if you're interested, TwoFactorAuth.org lists the full details of two-factor compatibility for hundreds of websites; your bank or favorite retail sites might offer it too!
Stay In Charge Of Your Accounts
It's no secret that Facebook changes up their workings often, and this unfortunately includes privacy settings. Because of this, you need to stay vigilant and check what you're sharing regularly; Facebook's newer privacy menu helps, but it too could change. Have you added any third-party apps? If so, head to your allowed apps in Facebook and make sure that the list is safe and current. Any entries you haven't used in a while or even have never heard of before should be chucked.
The more information about yourself and pictures you share with the public, the greater the chance that your security will be breached. There's nothing wrong with sharing on Facebook or other social media; just be sure to know your audience. Go over your friends list once a month to be sure you haven't accepted requests from anyone weird or someone you don't know well. A good test of your current privacy state is found on your Timeline: click the three dots menu to the right of View Activity Log and choose View As... to see what your page looks like to the public.
Another good idea is to Google yourself occasionally. Knowing the first few results that come up when someone is looking for you helps you estimate how much of your personal details are immediately accessible. If you find anything that you don't want out there, identify the site it's found on and fix it as soon as you can.
Let's take an example of a real hack to illustrate another point. Scarlett Johannson was a victim a few years ago, and her hacker had used the Forgot Password function along with readily accessible Internet information to get into her account. While he was in, he set up forwarding to send every message from her inbox to an email address he could monitor. This let him continue to read her messages even if she had changed her password.
The lesson here is to keep an eye on your outgoing messages on all sites. You're surely seen a social media scam where a friend's account is compromised and sends you a link to some junk website or worse. Often, people have no idea that this happened until their friends tell them, and someone who isn't tech-savvy may have already fallen for it. Be diligent and be sure there's no one using your account silently.
You != Jennifer Lawrence
With these tips, you're much less likely to become a victim of privacy invasion. Since you're likely not a person who's well-known like these women, there's less of a risk, but know that you are still a target regardless.
Now that you've secured yourself, sit back and enjoy the more lighthearted take: the funniest tweets about the celebrity nudes leak.
What other methods keep you safe from being hacked? Do you have any victim stories? Leave a comment!
Image Credits: Burglar Via Shutterstock, Index finger Via Shutterstock, Mouse and Key via morgueFile; xkcd Passwords via xkcd; PIN Hand via Shutterstock