What do you do when it is your turn at the ATM? Are you ready to pounce, majestically maneuvering your card to the slot, gracefully extracting your hard-earned dollars, and running to the nearest bar? Or are you more considered, scanning your surroundings for any inkling of malicious activity on or around the ATM itself?
We've all been the former -- in a rush, millions of things to do -- but taking those few moments before popping your card into the slot could be the difference between spotting an ATM that has been tampered with, and becoming a penniless statistic.
The range of tools available to scammers has risen in recent years, and largely follow a singular path. But while the tools remain roughly the same, the technology evolves, easing their obfuscation and aiding their camouflage. Let's take a look at some tell-tale signs of tampering, and how you can keep your cash firmly locked in your account.
Identifying The Issues
If you're diligent, you might spot the fake components, but you will have to actively look for the malicious parts. I mean, the malefactors want them to remain hidden for as long as possible, so they won't be covered in purple glitter and pink polka dots. Here are some commonly found ATM hacks.
Skimmers
A skimmer is a malicious card reader. It sits over the top of the existing ATM card reader slot and scans the magnetic strip of every card that enters the machine. Even with advances in banking card technology, such as card specific chips, the magnetic strip still contains vital information as to remain backwards compatible with outdated systems.
Indeed, even after the US finally rolled out EMV (Eurocard, Mastercard, Visa) cards, commonly referred to as "Chip and PIN," a massive amount of vendors still require a magnetic swipe to complete some transactions.
Typically, skimmers are small, fitting over the card reader slot and may have been artificially "worn" to match the appearance of an older ATM. In recent years skimmers have further evolved to easily fit within the "throat" of the card slot itself, making their detection nearly impossible. Other technological advances have seen massively increased battery life for installed devices without access to an alternative power source. As well as this, some advanced skimmers are able to transmit their data via Bluetooth, allowing a thief to return to the ATM as a regular "customer," pair with the device and download the pilfered card information.
- Consider the locale of the ATM. Dark and shady? Out of sight? Minimal footfall? No surveillance?
- Give the card slot a wiggle. If it feels loose, moves around in its specific slot, or heaven forbid, actually comes loose from the machine, you should move on.
- Consider the slot. Many ATMs have arrows to indicate where to insert the card, or other markings making each slot easily identifiable. Does the reader cover any of the markings or arrows? If so, it could be a sign of tampering.
- Check graphics and instructions. Another indicator can be misaligned instructions or graphics, or perhaps colors slightly out of sync.
- Cross-check with other ATMs. If the ATM is part of a pair (or more), check its neighbor for any discrepancies.
The thieves aren't silly, and come up with innovative ways to help you part with your cash. You might actually have your details swiped before you even reach the ATM. How, you ask? Well, those ATMs behind a security door that require you to swipe your card to enter, seemingly offering one of the safest options of all? Yes -- your card details were skimmed at the door, and your PIN was recorded with a pinhole camera.
Many ATM manufacturers now integrate anti-skimming devices, while it is easy for individual vendors to purchase an anti-skimming device for retrospective fitting. Card skimmers are typically used in conjunction with a minute camera, stationed above or extremely close to the number pad.
PINhole Camera
The next tool in the scammer's arsenal is the pinhole camera. To complete a physical transaction using cloned card details, there must be a PIN number to verify the process, captured alongside the card information. Many ATMs actually come with their own camera. There are no hard and fast statistics on how many ATMs have their own cameras, but it varies depending on their location. Those situated within a bank or mall are likely to have a camera to view your face, while others in gas stations or a bar may not.
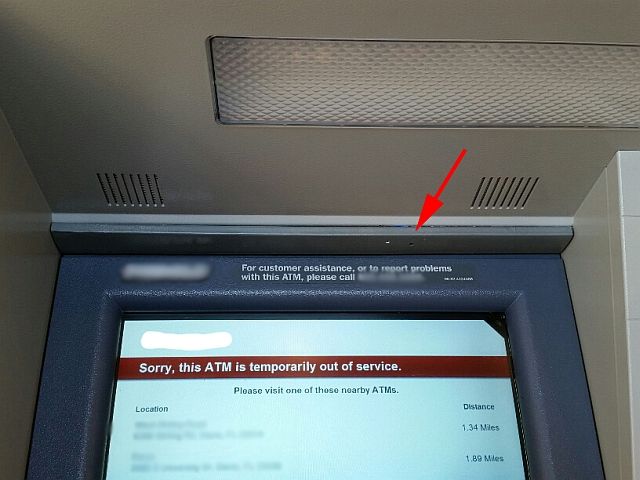
Pinhole cameras are different to those officially installed. Thieves will install a tiny physical camera somewhere on the ATM to capture PIN entries corresponding to the details swiped using the aforementioned skimmer. Their presence isn't always easy to spot. Their housing will be as close to the color of the ATM as possible, and will attempt to fit snug to the machine façade.
- Wiggling is your friend. If you cannot spot a skimming device, but have a bad feeling, wiggle and prod the area you suspect. If it moves, it could be the camera housing. Check all around, but particularly the areas directly in front of the number pad, and the panel/fixture where the ATM adjoins the building.
- Check the ATM. Look for any panels that don't fit quite right, bits of protruding material or off-colored panels; these could indicate a camera is in use.
- Consider your surroundings. Without raising potential paranoia levels any higher, the camera might not be situated on the machine itself. If you're in a gas station, assess how close the merchandise racks are to the ATM.
- Cover your PIN. Okay, so they might still get it, but at least you're making a concerted effort to stop thieves walking away with your banking details.
Number Pad
The final tool completing the thieves' tainted trifecta is the false number pad. Just as with the card skimmers and pinhole cameras, these vary massively in quality and cost, meaning some are thankfully easier to spot. However, those malefactors with enough enterprise and capital can research the specific model of their ATM target and purchase a false number pad that fits snug to the machine.
The number pad is often used alongside the card skimmer to replace a camera, working in the same vein as keystroke logging malware you might encounter on your computer. Once installed, each individual button press is logged, along with the time, to match up with the skimmed details.
- Check the height. The false number pad might not align correctly with its ATM surroundings, or may well appear to be slightly higher than it should be. As with the card skimmers, there might be symbols or arrows that are slightly obscured.
- Go on, give it a wiggle. Though this is less useful with a false number pad as they are usually fixed to the frame of the ATM, if it is moving more than you would expect i.e. at all, it should set your alarm bells ringing. A real ATM keypad shouldn't move at all -- it is integrated with the machine.
- Check the alignment. The keys themselves can sometimes give the game up. Misaligned or poorly printed replacement keys are usually an indicator something is afoot.
- Check the edges. If the number pad has been replaced by an entire panel, there may well be gaps around the edges of the ATM itself, where the fixture should be relatively, if not completely, seamless.
- Consider the age. Is the ATM you're about to use worn out? Does it have an astoundingly shiny number pad that looks out of place? It could be a sign of a recently installed malicious number pad.
If the design of the number pad replacement is exceptional, it will be difficult to spot. As with the pinhole cameras, if the thieves have enough money to purchase premium equipment it will make spotting any malicious activity that little bit more difficult.
Other ATM Issues - Malware
Aside from the physical alterations that can be made to an ATM, we must remember these are basically computers designed to spit money on command. Almost any device can be hacked, and ATMs are absolutely no different -- it just requires a different strategy.
ATM machines running the now extremely outdated Windows XP are a particular issue, and are unlikely to receive any software updates to protect against newly found vulnerabilities.
Security researchers at Kaspersky Lab have "identified 49 modifications" of a single type of ATM malware designed to turn the entire machine into a single skimming device, as well as being able to dispense cash at will from a selected cassette (the bit that holds the money). Meanwhile, researchers at Trend Micro recorded a 15% rise in fraudulent attacks involving European ATMs, identifying numerous manufacturer specific malware variants throughout the entire globe.
ATM malwares have different targets. While some may certainly target regular users such as you and I, other malware types seek "only" to empty the machine of its cash, on demand. Researchers at Proofpoint detailed GreenDispenser, which allows a thief to empty an entire machine using only a set of pre-designed PIN codes, and then, using a "deep delete" process, remove any trace of the malware.
Other ATM Issues -- Cover The Entire Machine
The scammers will go the extra mile to ensure your money ends up in their bank account. We touched briefly on the upper-end of the ATM thief scale: components tailored to specific machines, making use of the latest and greatest in manufacturing technologies to ensure parts blend in. Professional thieves and/or coordinated gangs can have an entire ATM façade manufactured, with multiple locations to hold their data capture devices.
As you can see in the linked video, the whole of the ATM is covered, completely subverting any potential customers whist making it extremely difficult to detect.
Trust…
Nobody, or anything. Or perhaps just your gut. I forget which one is best, but if you suspect something is wrong with the ATM you're stood in front of, just move on. You'll be saving yourself an immense amount of hassle, and enough stress to fill the Grand Canyon.
If you realize the ATM has a malicious device attached to it, do not remove it. There have been instances of criminals following their do-gooder citizen away and reclaiming their device -- remember, they may have paid thousands of dollars for the equipment. No: immediately phone the police and let them deal with the vendor and any would be criminals.
It can be difficult to spot an ATM that has been tampered with, for obvious reasons. Take just a moment, and reap the internal rewards.
Have you spotted a malicious ATM? What did you notice? What did you do? Let us know below!
Image Credits: Shocked woman by Kaspars Grinvalds via Shutterstock, Pinhole Camera via KrebsonSecurity, Pinhole Camera in Merchandise via Hoax-Slayer, Fake Keyboard via MyBroadband, ATM Malware Families via Trend Micro