We live in an interconnected, super-networked world. New technologies constantly appear on the market. Unless you constantly read networking, computing, or hacker news, you may find terminologies floating around that you don't understand.
So, here are common networking terms, what they mean, and where you're likely to encounter them.
1. WLAN
WLAN stands for Wireless Local Area Network.
A Wireless Local Area Network links two or more devices via wireless distribution. A WLAN usually operates within a restricted area, only providing connectivity to those devices within its confines. Any device that moves outside of the coverage area will lose its connection to the network.
It is highly likely you operate a WLAN in your home: your home Wi-Fi network. WLAN refers to a wireless local area network, which is precisely what your Wi-Fi network is.
2. WPAN
WPAN stands for Wireless Personal Area Network.
A Wireless Personal Area Network (WPAN) describes a network used to communicate between intrapersonal devices. When you are sat at your desk using a Bluetooth mouse, Bluetooth headphones, and a wireless mouse and keyboard, you are utilizing a WPAN. It's the same when connect your mobile to your PC over Bluetooth.
A WPAN describes the communication between devices in close proximity. However, it can also refer to devices in a wider range, i.e., connected via a Wireless Local Area Network (see above for more information on WLANs).
3. IPV4 and IPV6 Protocols
The internet uses a range of standardized protocols allowing network communication. The internet protocol suite is known as TCP/IP, which stands for Transmission Control Protocol/Internet Protocol.
The first major version of TCP/IP was Internet Protocol Version 4 (IPv4). Its successor is Internet Protocol Version 6 (IPv6), though both protocols are in use.
Both protocols define data transmission across the internet. Furthermore, the type of IP address defines the number of Internet Protocol (IP) addresses available for use. For example, you've probably seen IP addresses that look like "192.19.254.1".
This series of numbers refers to a specific location on the internet. Every site, router, and device connected to the internet is assigned a specific IP.
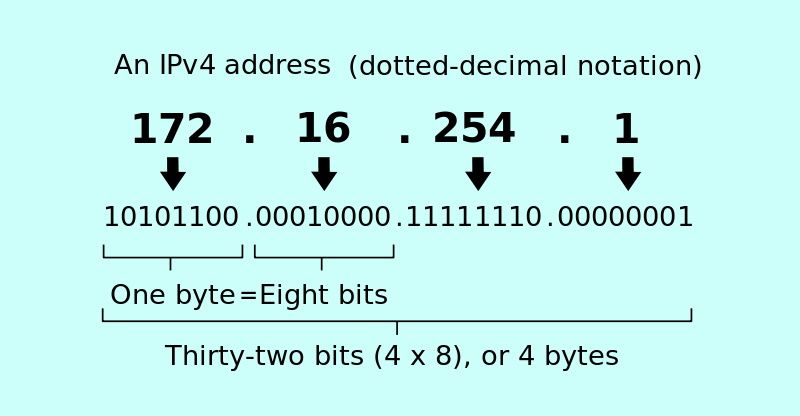
IPv4 limited the number of available IP addresses to 4,294,967,296. Sounds like a lot, right? IPv4 address exhaustion has long since passed, way back in February 2011. This is because IPv4 IPs were designed as 32-bit integers, limiting the available number of addresses. See the below image for a brief explanation.
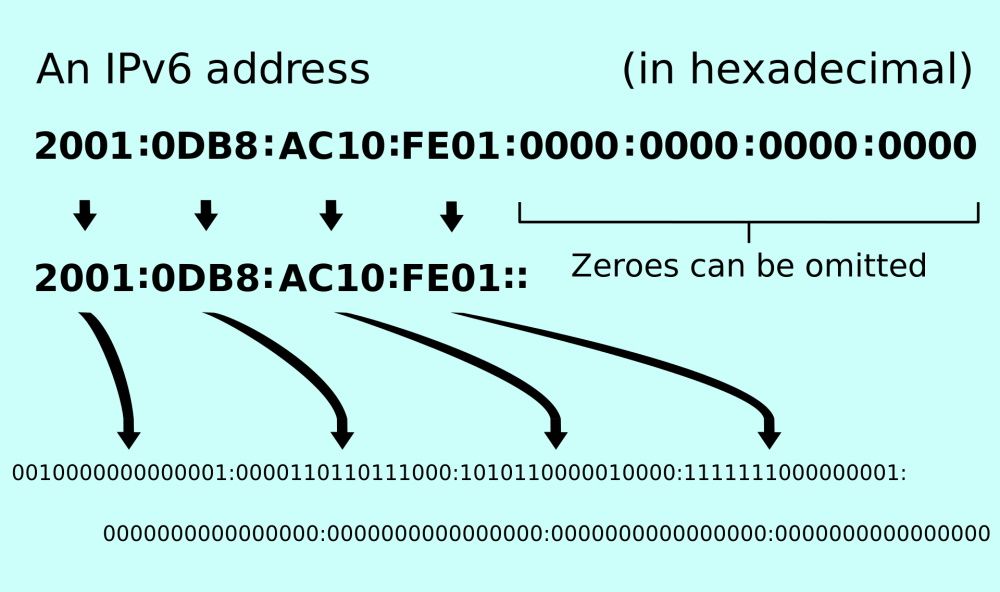
The IPv6 standard was launched to address this problem with the introduction of 128-bit hexadecimal IP addresses, providing a 3,400,000,000,000,000,000,000,000,000,000,000,000,000 address space for the internet to grow into. An IPv6 IP address looks different to its IPv4 counterpart, too: 4532:1cb8:75a3:4942:1771:9e2c:1350:8331
While IPv6 provided the necessary IP address expansion required for the rapidly expanding internet, it is not interoperable with IPv4. This means that IPv6 essentially operates on a parallel network. However, many IP translation gateways are already in operation, so you shouldn't notice much difference.
4. NAT
Network Address Translation is most commonly used by routers to share a single IP address (see above for information on the IPv4 and IPv6 protocols) across multiple devices. If you have a wireless router in your home, it likely uses NAT to enable each of your connected devices to access the internet through a single gateway (see below for more information on Gateways).
From the outside, your router has just a single IP address. Your router can assign individual IP addresses to the devices in your home network, creating a Local Area Network.
5. Gateway
Gateway refers to a device in your network that enables traffic to move freely from one network to another. Your router works as a gateway, allowing data to route from the internet to your connected devices.
6. Packet
A packet is the most common format of data carried over the internet. It cannot store a huge amount of data. At most, a packet can fit 65,535 bytes (or 0.065 megabytes) of information within them. However, your average internet packet won't even be this big. Typically, internet packets store only 1,500 bytes (0.0015 megabytes) of data.
A packet traditionally consists of two types of data: control information and user data.
Control information refers to the data the network requires to deliver the user data: source and destination addresses, sequencing information, and error detection codes.
User data refers to the actual data being transferred, be that looking up a website, clicking a link, or transferring files.
7. P2P
Peer-to-Peer refers to any network that connects users directly in a distributed network. Each connected computer is known as a peer. Peers are simultaneously users and providers to the network, allowing a P2P network to engage in more powerful activities while remaining beneficial to all connected users.
P2P is widely known due to its involvement in file-sharing networks, of which some shared content breaks copyright law. However, P2P file-sharing is also used for many legal activities as its task distribution allows low resource data transfer of larger files.
For example, many Linux distros use P2P to keep operating costs down, while cryptocurrencies such as Bitcoin use P2P to ensure the network's integrity. Furthermore, overlay and anonymity focused networks such as Tor and I2P also use peer-to-peer models, while Microsoft's Windows 10 uses a proprietary Delivery Optimization peer to peer network to make update delivery more efficient.
8. Protocols: TLS/SSL—HTTPS
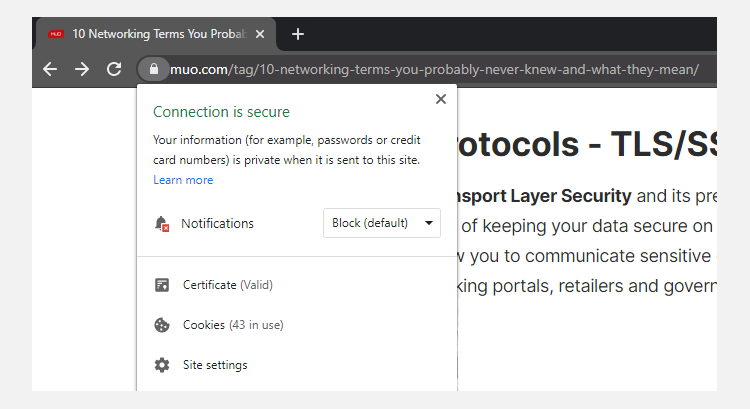
Transport Layer Security and its predecessor, Secure Sockets Layer, form an important part of keeping your data secure on the internet. They are cryptographic protocols that allow you to communicate sensitive data securely with various websites, such as online banking portals, retailers, and government gateways.
TLS/SSL works by layering encryption onto the existing Hypertext Transfer Protocol (HTTP) we all use to browse the web. This gives us Hypertext Transfer Protocol Secure (HTTPS), which you may have noted when accessing your banking or purchasing through an online retailer.
9. DDoS
DDoS stands for Distributed Denial of Service.
A Distributed Denial of Service is a type of cyberattack that overwhelms a service with requests, forcing it offline. Attackers target a specific website, service, or video game and flood the servers running with data requests. The number of requests can rapidly overwhelm the server infrastructure hosting the service, forcing it offline.
A DDoS isn't always malicious. If too many users attempt to access the same IP address simultaneously, it can overload the website's hosting server, causing access to the service to be denied. This unintentional denial of service is a regular occurrence when a website with a large user-base links to a much smaller one.
Indeed, when someone posts an interesting link to Reddit and the user base piles in, it often takes the smaller site offline. This is affectionately known as "the Reddit hug of death."
At any one time, there can be multiple DDoS attacks taking place around the world. You're more likely to hear about them when they knock a major service offline, but you can use the Digital Attack Map as an approximation as to what's going on.
10. DNS
DNS stands for Domain Name System.
The Domain Name System is how our computers translate our regular, everyday text into network readable IP addresses. When you type muo.com into your browser address bar and hit enter, your computer contacts its DNS server. The DNS server responds with the corresponding IP address of muo.com, connects, and displays glorious technology content for your enjoyment.
You can set your DNS servers to be different from their default, as several alternative DNS providers exist, such as Google Public DNS or OpenDNS. In some cases, switching to an alternative DNS provider can return small speed benefits when loading webpages, improve reliability with your Internet Service Provider, and provide additional security benefits.
Learning Network Protocols Is Handy
You don't have to take a comp-sci course or become a network engineer to learn about common networking terms. But in the hyper-connected world, understanding some of the more basic and commonly-used terms will help you get along online.
Image Credit: kubais/Depositphotos