Millions of switches, routers and firewalls are potentially vulnerable to hijacking and interception, after American security firm Rapid7 discovered a serious issue with how these devices are configured.
The problem - which affects both home and business users - is found in the NAT-PMP settings used to allow external networks to communicate with devices operating on a local network.
In a vulnerability advisory, Rapid7 found 1.2 million devices that suffer from misconfigured NAT-PMP settings, with 2.5% vulnerable to an attacker intercepting internal traffic, 88% to an attacker intercepting outbound traffic, and 88% to a denial of service attack as a result of this vulnerability.
Curious about what NAT-PMP is, and how you can protect yourself? Read on for more information.
What Is NAT-PMP, And Why Is It Useful?
There are two kinds of IP addresses in the world. The first is internal IP addresses. These uniquely identify devices on a network and allow devices within a LAN to communicate with each other. These are also private, and only people on your internal network can see and connect to them.
And then we have public IP addresses. These are a core part of how the Internet works, and allow different network to identify each other, and to connect with each other. The problem is, there aren't enough IPv4 addresses (the dominant IP addressing system - IPv6 hasn't yet replaced it) to go around. Especially when we consider the hundreds of millions of computers, tablets, phones and Internet Of Things appliances floating about.
So, we have to use something called Network Address Translation (NAT). This makes each public address go much further, as one can be associated with multiple devices on a private network.
But what if we have a service - like a web server or a file server - running on a network that we'd like to expose to the greater Internet? For that, we'd need to use something called Network Address Translation - Port Mapping Protocol (NAT-PMP).
This open standard was created around 2005 by Apple, and was designed to make the process of port mapping much easier. NAT-PNP can be found on a range of devices, including ones that aren't necessarily made by Apple, such as those produced by ZyXEL, Linksys and Netgear. Some routers which don't support it natively can also get access to NAT-PMP through third-party firmwares, such as DD-WRT, Tomato and OpenWRT.
So, we get that NAT-PMP is important. But how can it be vulnerable?
How The Vulnerability Works
The RFC which defines how NAT-PMP works says this:
The NAT gateway MUST NOT accept mapping requests destined to the NAT gateway's external IP address or received on its external network interface. Only packets received on the internal interface(s) with a destination address matching the internal address(es) of the NAT gateway should be allowed.
So, what does that mean? In short, it means that devices that aren't on the local network should not be able to create rules for the router. Seems reasonable, right?
The problem arises when routers ignore this valuable rule. Which, seemingly, 1.2 million of them do.
The consequences can be severe. As previously mentioned, traffic sent from compromised routers can be intercepted, potentially leading to data leakage and identity theft. So, how do you fix it?
What Devices Are Affected?
This is a hard question to answer. Rapid7 haven't been able to definitively prove what routers have been affected. From the vulnerability assessment:
During the initial discovery of this vulnerability and as part of the disclosure process, Rapid7 Labs attempted to identify what specific products supporting NAT-PMP were vulnerable, however that effort did not yield especially useful results. ... because of the technical and legal complexities involved in uncovering the true identity of devices on the public Internet, it is entirely possible, perhaps even likely, that these vulnerabilities are present in popular products in default or supported configurations.
So, you have to do a bit of digging yourself. Here's what you need to do.
How Can I Find Out I'm Affected?
First, you need to log into your router and look at your configuration settings through its web interface. Given that there are hundreds of different routers, each with radically different web interfaces, giving device-specific advice here is nigh on impossible.
However, the gist is pretty much the same across most home networking devices. Firstly, you need to log into the administration panel of your device through your web browser. Check your user manual, but Linksys routers can usually be reached from 192.168.1.1, which is their default IP address. Likewise, D-Link and Netgear use 192.168.0.1, and Belkin use 192.168.2.1.
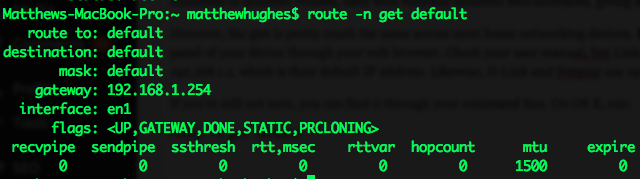
If you're still not sure, you can find it through your command line. On OS X, run:
route -n get default
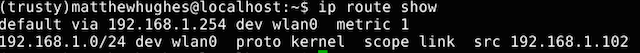
The 'Gateway' is your router. If you're using a modern Linux distro, try running:
ip route show
In Windows, open the Command Prompt and enter:
ipconfig
Again, the IP address for the 'Gateway' is the one you want.
Once you've gained access to your router's administration panel, have a poke around in your settings until you find the ones which relate to Network Address Translation. If you see anything that says something like 'Allow NAT-PMP On Untrusted Network Interfaces', turn it off.
Rapid7 has also gotten the Computer Emergency Response Team Cordination Center (CERT/CC) to start narrowing down the list of devices that are vulnerable, with the aim of working with device manufacturers to issue a fix.
Even Routers Can Be Security Vulnerabilities
We often take the security of our networking gear for granted. And yet, this vulnerability shows that the security of the devices we use to connect to the Internet isn't a certainty.
As always, I'd love to hear your thoughts on this topic. Let me know what you think in the comments box below.