How would you feel if all you needed was to press a button and all your systems were up to date, all the necessary packages installed and ready to go? Sounds fantastic, right?
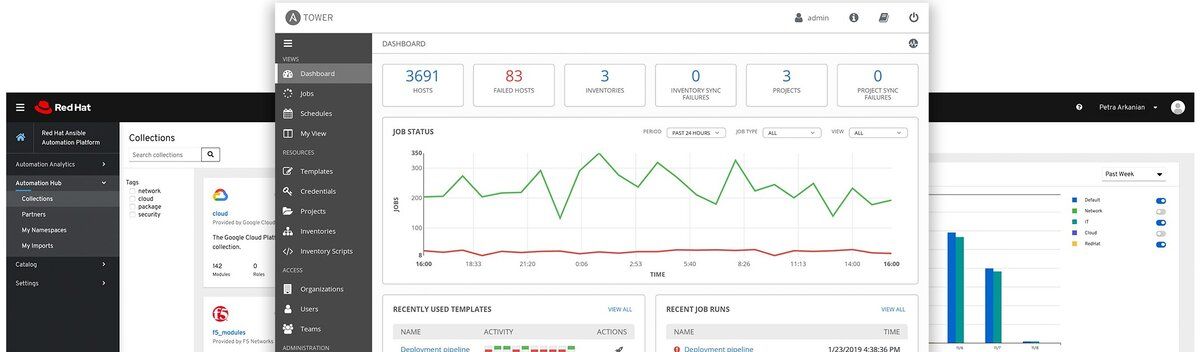
In the modern IT world, DevOps engineers are bringing this dream to a reality. We now have tools such as Ansible, which makes IT management processes more manageable and quicker via a few clicks reducing errors and the manual input from a human.
Read on to learn everything you need to know about Ansible, including a brief overview of how to use it.
What Is Ansible?
Ansible is a powerful open-source automation engine. It is cross-platform, allowing developers to manage devices from any operaing system, including Windows, macOS, and Linux.
Ansible offers a range of features: configuration management, application deployment cloud provisioning, system updates, security automation, continuous delivery, and many more. It is a lightweight tool and does not require additional software or packages to run, making it easy to deploy.
Core Ansible Features
The following are some of the features offered by Ansible as an automation tool.
App Deployment
Ansible allows developers to quickly and easily deploy apps on servers. It eliminates the need to write custom code or perform package management manually. Instead, you define the tasks required for an application to run and execute them remotely on the target system instead of using Ansible playbooks. You can ship a single Playbook into multiple devices simultaneously and run the application on numerous servers.
Cloud Provisioning
Cloud provisioning is the method using installing, configuring, and managing cloud computing resources.
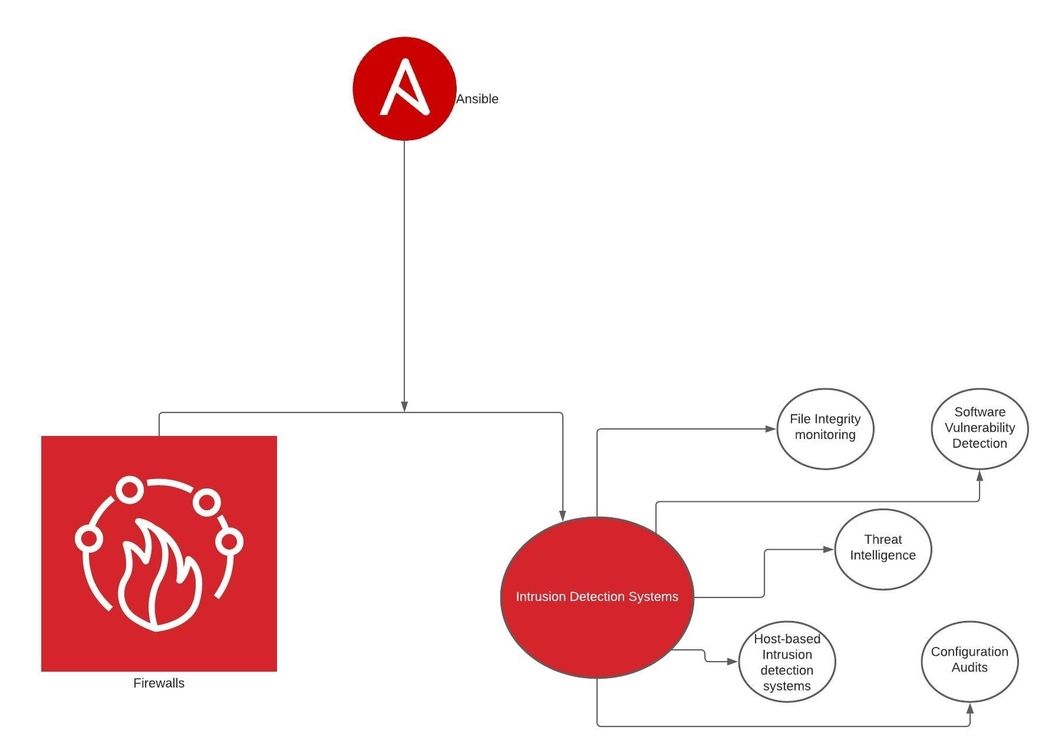
Ansible allows you to automate cloud provisioning tasks, including setting up the infrastructure, setting up hosts, managing network interfaces, managing firewalls and users on the remote hosts.
Configuration Management
Configuration management is another feature of Ansible. Using Ansible playbooks or ad-hoc commands, you can quickly get your systems up and running in a few commands. Since Ansible uses YAML as the default configuration language, it is easy to create tasks in a human-readable format and execute them on remote machines.
For example, if you have a freshly provisioned server, you can use Ansible to update the system, install the necessary packages and start the services on the server.
Security Automation
Ansible is helpful in security automation tasks. For example, using a few Ansible commands, you can set up custom firewall rules, check for malware, clean your system using custom tools, and more. It also allows you to monitor your system's health and quickly perform backups of your system in case of failure.
It also uses SSH to authenticate users and execute commands on remote hosts, making it very secure to use.
Ansible Architecture
Let us learn more about the parts that make up Ansible Engine.
Inventories
Ansible manages remote hosts by the use of inventories. An inventory is a simple text file that contains IP addresses and hostnames of remote machines. Hosts in the inventory file can be organized into various groups such as webservers, databases, backups, etc. Organizing hosts into groups helps users to execute commands on a specific group of machines.
Note: You must populate Ansible inventory file with at least one host before running any tasks.
Playbooks
Ansible playbooks are simple text files written in YAML (YAML Ain’t Markup Language). They contain instructions or commands to execute on a remote host to perform a specific task.
Since Ansible playbooks are written in YAML, they are in the form of human-readable format. This makes it very easy to use and understand Ansible as the users do not need to master new syntax. Each playbook comprises at least one or more tasks executed on all or specific hosts.
Related:
Modules
Ansible provides users with modules. Modules are commands that help to manage a remote host from the control node. These modules enable Ansible to manage users, install and uninstall packages, update systems, etc. They are executed in Playbooks for specific tasks as required. Ansible provides more than 4600 modules. Check out all Ansible modules.
Plugins
Ansible architecture allows for custom plugins. They help extend or improve the base functionality of the Ansible engine. Although it comes with several plugins by default, you can also create custom plugins to fit your needs.
API
Ansible extends functionality by providing users with various API endpoints for debugging, running commands, callbacks, and more.
Getting Started With Ansible
Ansible is easy and quick to set up and use. This section will demonstrate how to install Ansible on a host machine, configure remote hosts, and perform basic automation tasks.
Ansible is cross-platform and thus supported by major Operating systems. For simplicity, this guide will discuss Ansible installation on a Debian-based Linux distribution. Check Ansible installation process for other operating systems.
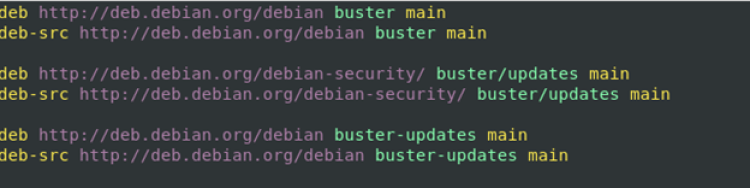
Start by editing the /etc/apt/sources.list file
sudo vim /etc/apt/sources.list
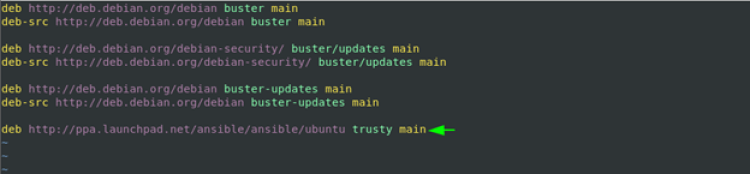
Inside the file, add the following entries:
deb http:<em>//</em>ppa.launchpad.net/ansible/ansible/ubuntu trusty main
The above entry will add Ubuntu PPA to the Debian repositories allowing you to install Ansible.
Next, run the commands below:
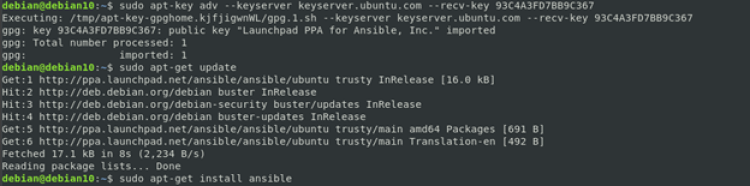
$ sudo apt-key adv --keyserver keyserver.ubuntu.com --recv-keys 93C4A3FD7BB9C367
$ sudo apt update
$ sudo apt install ansible -y
The first command adds the required keys.
The following commands update the software repositories and finally install Ansible.
Now that you have Ansible installed on your system, proceed.
Creating an Inventory
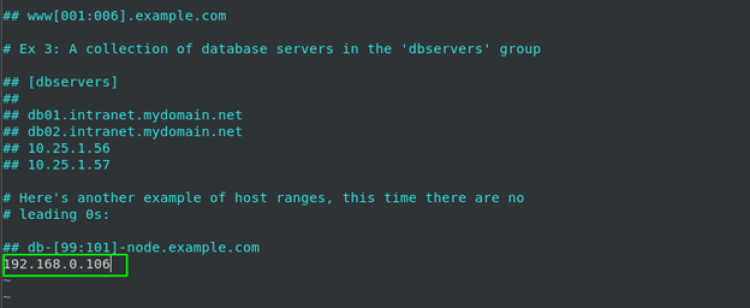
The first step before performing any Ansible automation tasks is to set up a host inventory file.
The default inventory file is located in /etc/ansible/hosts. Using your favorite text editor, add the IP addresses of the remote hosts you wish to automate.
$ sudo vim /etc/apt/hosts
Save the file and close.
Creating a Simple Playbook
Ansible playbooks allow users to automate tasks by setting the commands that are executed on the remote host.
You will create a simple Ansible playbook that installs Apache Web Server, create a firewall rule to allow Apache, and restarts the service
Ansible uses YAML as the default configuration language for its playbooks.
Create a YAML file using the touch command as:
$ touch first-playbook.yaml
Using your text editor, add the entries as shown in the example playbook below:
$ vim first-ansible-playbook.yaml
---
- hosts: all
become: true
tasks:
- name: Update apt packages
apt:
state: latest
update_cache: yes
- name: Install Apache
apt:
name: apache2
state: latest
- name: Install UFW Firewall
apt:
name: ufw
state: latest
- name: Allow HTTP ufw
ufw:
state: enabled
rule: allow
port: "80"
proto: tcp
- name: Restart Apache
service:
name: apache2
state: restarted
In the playbook above, start by specifying the hosts you want to execute the playbook. Since there is only one host in the inventory file, set the hosts to all.
Next, set the become statement, which allows the tasks in the playbook to run as root.
The preceding lines define the tasks to be carried out on the remote host. They include a name that describes the functions and the actual tasks to run on the host.
The first tell Ansible to update the repository cache; this corresponds to the command:
$ sudo apt-get update
The following instruction installs the latest version of the Apache webserver.
Following that is the task of installing the UFW firewall. This requires enabling and port 80 allowing, which Apache uses on TCP protocol.
Finally, the last statement restarts the Apache webserver.
Run Ansible Playbooks
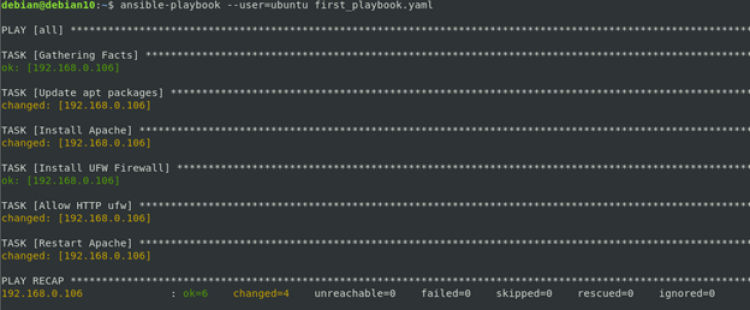
To run the Ansible playbook, we need to use the ansible-playbook command, which comes with Ansible upon installation.
To run the first-playbook.yaml file, use the command:
$ ansible-playbook --user=ubuntu first-playbook.yaml
In the command above, the --user option is passed, which specifies the user on the remote host.
NOTE: Ensure you have SSH keys installed on the remote host.
Once you execute the command above, you will get an output as shown.
The above shows all the commands have been executed successfully on the remote host.
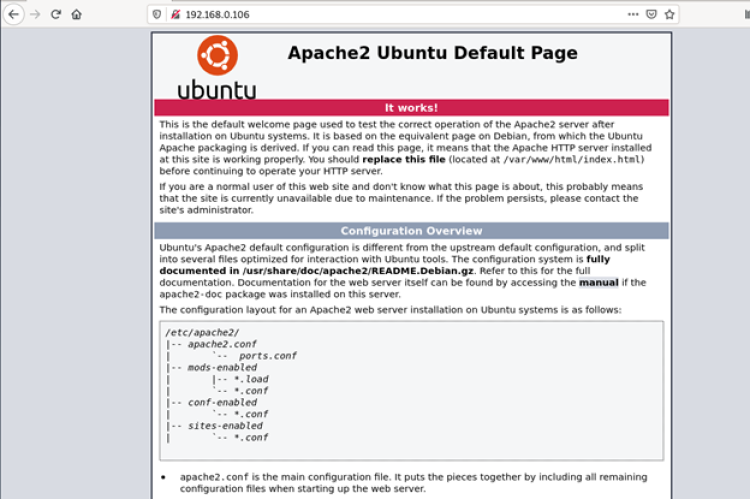
Verify Tasks
To verify the tasks in the playbook have been executed successfully, open your browser and navigate to the remote host’s IP address.
If the commands have been executed and the Apache server is running, you should see the default Apache Ubuntu default page as:
Should You Use Ansible?
In closing, it is clear that Ansible is a powerful tool. Its flexibility, features, and capabilities make it a promising tool for current and future automation tasks. If you are a DevOps engineer looking to automate your IT tasks quickly and easily, Ansible will play a significant role in your journey.