The National Crime Agency (NCA) is Britain's answer to the FBI. They have jurisdiction in all parts of the United Kingdom, and are responsible for combatting human, weapon and drug traffickers; cyber criminals; and economic crime.
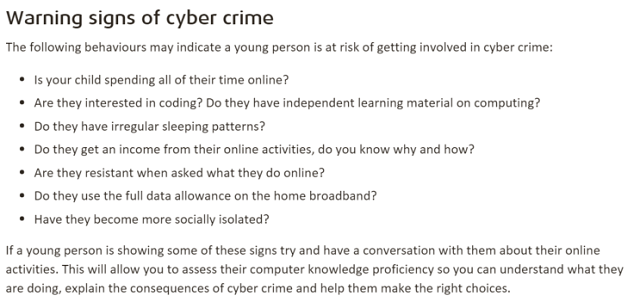
On Tuesday, they launched a campaign to deter young people from embarking upon a life of computer crime. As well as a video and a hashtag ("#CyberChoices"), the NCA also published a list of warning signs a parent could use to tell if their child was on the road to becoming a digital ne'er-do-well.
Worst. Advice. Ever.
I can't fault the intentions of the National Crime Agency. Cybercrime destroys lives. The Ashley Madison data leak tore an untold number of families asunder. The 2007 TJX Hack resulted in the leaking of 45.6 million credit card numbers, and cost the company an eye-watering $256 million.
Then there's the personal cost to the hackers themselves.
Albert Gonzales, the TJX hacker, was sentenced to 20 years in jail. He was 28. Jake Davis, who was the silver-tongued voice behind Lulzsec, was extradited to London from his Shetland Island home, and sentenced to two years in a young offender's institute, and had severe restrictions imposed on his use of the Internet.
Clearly, the National Crime Agency want to stop people from committing computer crimes. But the overall tone of the campaign is that they want to dissuade teenagers (who are naturally impulsive, and can struggle to understand the consequences of a given action) from doing something which has the potential to define the rest of their lives.
But here's the problem: They gave some really terrible advice.
Advice that is so broad, if you were to follow it to the letter, you could safely assume anyone reading this article is a hacker. No, that isn't an exaggeration.
Well, the following is by no means an exhaustive list of their advice. That can be found on the National Crime Agency website, or in the screenshot above. I've chosen to pick the advice which I feel is the most egregiously bad, and explain why.
Are They Interested in Coding?
Saying someone interested in computer programming is at risk of becoming a computer criminal is sort of saying that anyone interested in cars is at risk of developing into the type of reprobate I play on Grand Theft Auto V. They're just not.
I know, most people are smart enough to not equate a legitimate profession that's surging with jobs, with something that's highly illegal. But I worry about the one parent who, despite having the best intentions, will read it and prevent their child from learning about software development for fear of them getting arrested. That's what worries me.
Do They Have Independent Learning Material on Computing?
On the National Crime Agency, this question was on the same bullet point as "Are they interested in coding?". But it's important, so I'm going to address it on its own.
Do you know what makes a great developer? Curiosity.
Great developers are always reading things on their own time. They learn about new libraries and frameworks on their weekends, and above all, they have the ability to teach themselves. These people, by and large, are not computer criminals.
The traits that make great developers start to present at a young age. High school computing classes have a very limited syllabus. While they might cover the basics of learning to program, they often fail to cover more exciting topics, like web development and robotics.
It's natural for bright, curious young people to want more from their computing education, and to pursue things they're interested in. Rather than treat this with suspicion, we should applaud it.
Do They Have Irregular Sleeping Patterns?
Show me a teenager who actually goes to bed when their parents tell them to. If they're anything like me and my friends growing up, they're probably going to be staying up to play video games and talk on MSN Messenger (or 2015's equivalent). This is just part of being a teenager.
There is also a myriad of medical reasons why someone might experience disturbed sleep patterns. One's called Delayed Sleep Phase Disorder, and it disproportionately affects teenagers. The symptoms of this disorder affect when a person falls asleep, and when they wake up, with sufferers generally falling asleep some hours after midnight, and then struggling to wake up in the morning.
Do They Get an Income From Their Online Activities?
Are we supposed to be suspicious of ambition and entrepreneurship now?
There are hundreds of legal ways for people make money online. You don't need to be an adult for most of them.
If your child is flush with cash from the Internet, it's probably thanks to their Twitch or YouTube channel, or a side-gig in website testing. Not from port-scanning the NSA and distributing malware from botnets.
Are They Resistant When Asked What They Do Online?
I think most teenagers are pretty resistant to talking about what they do online. That was definitely the case with me. When I was 15, I played video games for hours on end with absolute strangers in America and Finland. I hung out on obscure music message boards, and I had a secret blog where I ranted about inanities in the way only a conceited, terminally ill-informed teenager could. When my parents would ask me what I was up to, the answer was always the same.
"Stuff. Things. Go away. You wouldn't understand!"
I wasn't doing anything untoward or criminal. As teenagers go, I was as vanilla as they got. I don't think I ever even had a detention in high school! But like most teenagers, I was moody and hormonal, and thought my parents simply wouldn't get what I was up to.
That's not criminal. That's just being an adolescent.
Do They Use the Full Data Allowance on the Home Broadband?
Wait, what? Seriously NCA? Did you write this in 2004?
Capped connections are so rare in the UK, two of the three biggest ISPs (Virgin Media and Talk Talk) don't even offer them. There's just no market for them, thanks to the stratospheric rise of Netflix and YouTube.
But beyond that, you don’t need that much bandwidth to hack a computer. The fact is, most attacks use less bandwidth than a YouTube video. SQL injection (SQLi) and Cross Site Scripting (XSS) attacks can be done in the browser. All you need to do is pass a specially crafted input into a web form, or a search box, or through some URL parameters. That's it.
Likewise, you don't need a lot of bandwidth to use MetaSploit or Nessus, or to scan for open ports on a server. These attacks can be measured in the kilobytes.
Put simply, there's no real link between bandwidth use and cybercriminality.
Have They Become More Socially Isolated?
Oh, look. The same, tired "loner geek" trope. Except, for the most part, that's utter bullshit.
Many of the members of lulzsec had families. Sabu, the leader of Lulzsec, was a foster parent to two young girls. Ryan Cleary, who went by the name of ViraL, had a girlfriend. The TJX hackers started off as friends, before going on to hack one of the largest clothing retailers on the planet.
I should know what hackers are like. I've been to a number of computer security conferences, both in the UK, and abroad. I've mingled with all shades of the hat spectrum, from black to white. For the most part, hackers are gregarious and raucous. The complete opposite of a shy, basement dweller.
Terrible Advice. Please Ignore
So, we know the NCA has given out some pretty poor advice. Not only does it treat natural, teenage behavior as suspicious, but it also inherently discourages the qualities we want to see from our young people.
Suppose you know a parent who's worried about their child getting involved in computer hacking. What advice would you give them? Tell me all about it in the comments below.
Photo Credits: Young Girl Uses Laptop by Sean Locke Photography via Shutterstock, CultureTECH BT Monster Dojo (Connor2NZ), Money (Keith Cooper), BT Home Hub (Tom Page), Sleeping Teenager (Dan DeLuca)