The smartphone has evolved into an integral part of life. Think about it, how many times do you use your phone for some task in single day? Numerous times I suppose. Yet, for a device that is so important, I am often shocked by the mistakes people make on their smartphones and unnecessarily expose themselves to security risks.
The following is a run-down of ten of the most common smartphone mistakes.
Not Locking That Phone
It may be a tad irritating to have to enter a screen lock password every time you want to use your phone but this is one of the easiest ways to prevent unauthorized access and/or use of your phone. While tech savvy villains can crack any screen lock security with time, implementing this measure provides you with at least some basic form of security that will prevent most people from accessing your phone.
The best type of screen lock is a PIN or password. Avoid screen lock patterns which can easily be hacked. Set the phone to lock the screen after one minute of being idle.
Joining Public Wi-Fi Networks
Public Wi-Fi networks may be cheap but they are also a major security risk. Information sent over public Wi-Fi networks is visible to anyone on the network if they know how to view it. Hackers can easily steal your information and remotely access your device. If you must use a public Wi-Fi network, connect to the Internet using a VPN. VPN stands for Virtual Private Network and is a method to connect to websites securely even on public networks. Otherwise, use your mobile data network.
Not Using An Antivirus & Other Security Software
Many people don't realize that a smartphone is actually a computer and is still prone to the same malware risks. They will go to great lengths to make sure they have the latest and most up-to-date antivirus for their PC but have zero protection for their smartphone. According to the Journal of Information Systems Technology and Planning, over 96% of smartphones do not have pre-installed security software. Few smartphone users go to the trouble of installing antivirus and other security software.
Some good free antivirus software for Android phones include; Bitdefender, AVG and Avast. Apple says their iPhones are practically impermeable to malware but only time will tell.
By installing an antivirus on your smartphone, you also avoid transferring a virus to your computer via USB which is a common problem these days. In addition to that, it is also a good idea to install antitheft software that prevents access to your phone after it has been stolen. An application such as Prey wipes your data remotely if your phone is stolen.
To track your phone using GPS, you can also install an app such as Where's My Droid for Android or Find My iPhone for iPhones.
Forgetting To Install Those Updates
Smartphone manufacturers and app developers regularly issue software updates to improve functionality and to patch security gaps. In general, you should accept updates to your phone's operating system as soon as you are notified. The same goes with apps running on your phone. Make it a habit to regularly update the software running on your smartphone.
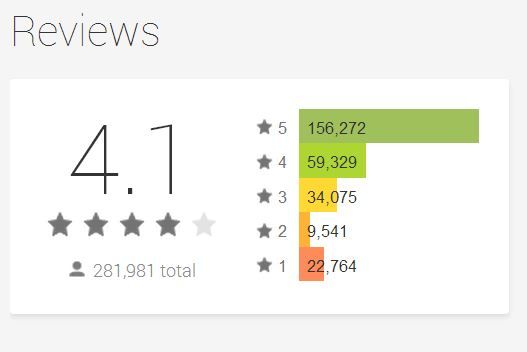
Not Verifying Your Apps
Few people verify apps before they download and install them. By verify, I mean checking to see the developer's history, prior products, reviews and going online to carry out some basic research before installing an app. Many smartphone users download and install apps that come packaged with malware that gives a remote hacker root access. The problem is mainly with Android phones due to the relaxed rules required to host an app in the Play Store. iPhone users are safer due to Apple's closed wall policy.
Simply Tapping On Links
According to RSA's cyber security experts, smartphone users are more susceptible to phishing attacks than desktop users. They tend to be less vigilant about security. It is harder to spot a fake login page on a smartphone than on a computer. Further, shortened URLs make it harder to detect illegitimate addresses. The best defense is to avoid clicking on links sent via SMS or instant messaging apps. Also, always open email links using your computer.
Jailbreaking or Rooting
I know I will get lots of flak for this from hardcore 'jailbreakers' and 'rooters' on this one. The fact of the matter is that non-rooted Android devices and non-jailbroken iPhones have security safeguards that limit the amount of access a user has to vital parts of the phone's operating system. Jailbreaking or rooting gives you access to hidden system settings that allows you to do much more with your phone. Of course, the price you pay for that is greater security risk.
But, I am not saying you should not jailbreak or root your phone. All I am saying is that if you choose to do so, make sure you know what you are doing. If you are new to these concepts, please read our Android Rooting Guide and our article on Jailbreaking for newbies.
Not Switching Off Bluetooth
Have you heard of the terms bluejacking, bluebugging or bluesnarfing? These all describe a situation where a hacker gains access to your phone using your Bluetooth connection. Using this technique, the hacker only needs to be at least 30 feet away from you and you'll never know what hit you. Within seconds, a Bluesnarfer can steal data such as confidential information and even login data to various sites. So, unless you are transferring or receiving a file, switch off your Bluetooth connection.
Forgetting To Log Out
If you are always logged into PayPal, Amazon, eBay and other sensitive sites where your finances are within easy reach, you might as well leave your credit card lying on the table at your local eatery. Don't keep your phone permanently logged into such websites. Don't check the box in the app that asks to save your username and password. It is convenient not to have to log into the app every time but it exposes you to considerable financial risk. If your phone were to be stolen, a thief would have unrestricted access to your finances and you could end up with a massive bill for things you never bought.
The same goes for a browser. If you log into sensitive sites such as mentioned above, do not give the browser permission to save your username and password. Also, make sure you clear your browser history after surfing for sensitive material. Chris Hoffman published an excellent article on how to delete your Android browser history and for the iPhone users, read "How to Delete Any and All History on Your iPhone" by Joshua Lockhart.
Storing Sensitive Data On Your Phone
I have never quite understood why some people insecurely store credit card PINs, bank online passwords, social security numbers and other such sensitive data on their phones. In the event your phone is stolen, it wouldn't take a genius to figure out that a four digit number stored as a phone contact is a PIN to one of your accounts. With a bit more digging, a clever crook can mess up your life.
The Take Away
The safeguards for all the mistakes listed here are easy and simple to implement. The problem is that many people take security for granted and assume the worst won't happen to them. Security is about 'when' you get hit not 'if'you get hit. At the end of the day, you must take charge of your smartphone's security.
Now, over to you, are you guilty of any of these mistakes? What other security recommendations do you have? Please share with us in the comments below.
Image credits: warrenski via Flickr, Rocco Lucia via Flickr, quinn.anya via Flickr, ryanne via Flickr, Shopping Cart Icon Via Shutterstock